- Hot
- Active
-
 Forum Thread:
Gaining Access into the Victim's Whatsapp on Android
12
Replies
Forum Thread:
Gaining Access into the Victim's Whatsapp on Android
12
Replies
11 hrs ago -
 Forum Thread:
Whatsapp Hack?
19
Replies
Forum Thread:
Whatsapp Hack?
19
Replies
12 hrs ago -
 Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
3 days ago -
 Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
2
Replies
Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
2
Replies
3 wks ago -
 Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
3 wks ago -
 Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
2 mo ago -
 Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
2 mo ago -
 Metasploit Error:
Handler Failed to Bind
41
Replies
Metasploit Error:
Handler Failed to Bind
41
Replies
2 mo ago -
 Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
3 mo ago -
 How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
3 mo ago -
 How to:
Crack Instagram Passwords Using Instainsane
36
Replies
How to:
Crack Instagram Passwords Using Instainsane
36
Replies
3 mo ago -
 Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
3 mo ago -
 Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
3 mo ago -
 Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
4 mo ago -
 How to:
Sign the APK File with Embedded Payload (The Ultimate Guide)
10
Replies
How to:
Sign the APK File with Embedded Payload (The Ultimate Guide)
10
Replies
4 mo ago -
 Forum Thread:
How to Run and Install Kali Linux on a Chromebook
18
Replies
Forum Thread:
How to Run and Install Kali Linux on a Chromebook
18
Replies
5 mo ago -
 Forum Thread:
How to Find Admin Panel Page of a Website?
13
Replies
Forum Thread:
How to Find Admin Panel Page of a Website?
13
Replies
6 mo ago -
 Forum Thread:
can i run kali lenux in windows 10 without reboting my computer
4
Replies
Forum Thread:
can i run kali lenux in windows 10 without reboting my computer
4
Replies
6 mo ago -
 Forum Thread:
How to Hack School Website
11
Replies
Forum Thread:
How to Hack School Website
11
Replies
6 mo ago -
 Forum Thread:
Make a Phishing Page for Harvesting Credentials Yourself
8
Replies
Forum Thread:
Make a Phishing Page for Harvesting Credentials Yourself
8
Replies
6 mo ago
-
 How To:
Dox Anyone
How To:
Dox Anyone
-
 How To:
Scan for Vulnerabilities on Any Website Using Nikto
How To:
Scan for Vulnerabilities on Any Website Using Nikto
-
 How To:
Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
How To:
Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
-
 How To:
Gain SSH Access to Servers by Brute-Forcing Credentials
How To:
Gain SSH Access to Servers by Brute-Forcing Credentials
-
 How To:
Brute-Force Nearly Any Website Login with Hatch
How To:
Brute-Force Nearly Any Website Login with Hatch
-
 How To:
Crack Shadow Hashes After Getting Root on a Linux System
How To:
Crack Shadow Hashes After Getting Root on a Linux System
-
 How To:
Enumerate SMB with Enum4linux & Smbclient
How To:
Enumerate SMB with Enum4linux & Smbclient
-
 How To:
The Top 80+ Websites Available in the Tor Network
How To:
The Top 80+ Websites Available in the Tor Network
-
 How To:
Build an Off-Grid Wi-Fi Voice Communication System with Android & Raspberry Pi
How To:
Build an Off-Grid Wi-Fi Voice Communication System with Android & Raspberry Pi
-
 How To:
Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
How To:
Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
-
 How To:
Crack SSH Private Key Passwords with John the Ripper
How To:
Crack SSH Private Key Passwords with John the Ripper
-
 How To:
Check if Your Wireless Network Adapter Supports Monitor Mode & Packet Injection
How To:
Check if Your Wireless Network Adapter Supports Monitor Mode & Packet Injection
-
 How To:
Find Identifying Information from a Phone Number Using OSINT Tools
How To:
Find Identifying Information from a Phone Number Using OSINT Tools
-
 How to Hack Wi-Fi:
Cracking WPA2 Passwords Using the New PMKID Hashcat Attack
How to Hack Wi-Fi:
Cracking WPA2 Passwords Using the New PMKID Hashcat Attack
-
 How To:
Use Kismet to Watch Wi-Fi User Activity Through Walls
How To:
Use Kismet to Watch Wi-Fi User Activity Through Walls
-
 How to Hack Wi-Fi:
Cracking WPA2-PSK Passwords Using Aircrack-Ng
How to Hack Wi-Fi:
Cracking WPA2-PSK Passwords Using Aircrack-Ng
-
 How To:
Extract Bitcoin Wallet Addresses & Balances from Websites with SpiderFoot CLI
How To:
Extract Bitcoin Wallet Addresses & Balances from Websites with SpiderFoot CLI
-
 The Hacks of Mr. Robot:
How to Hide Data in Audio Files
The Hacks of Mr. Robot:
How to Hide Data in Audio Files
-
 Hacking macOS:
How to Hack a Mac Password Without Changing It
Hacking macOS:
How to Hack a Mac Password Without Changing It
-
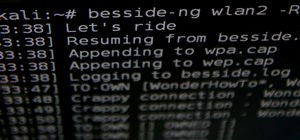
 How to Hack Wi-Fi:
Automating Wi-Fi Hacking with Besside-ng
How to Hack Wi-Fi:
Automating Wi-Fi Hacking with Besside-ng
















6 Responses
"how to hack my boyfriend's phone"
Step 1:
Grow up and confront him if you cannot trust him, instead of getting controlling.
Step 2:
That's it. Be a better person.
It's really simple.
Follow steps here Link
Our notifications show "how to hack my boyfriend's phone..."
(Since you changed the title)
So, this is neither ethically nor legally right. I find it right under no circumstances and perspectives, and I shall soon justify it.
Justification 1: If I were the person you'd spy on, and I get it from anywhere (eg. Data Usage, Packet Analysis and GeoIP), then believe me, I'm not letting it go. Since I already know you well (probably...), this would be a decision that'll haunt you forever, that you shall regret but receive no mercy.
Justification 2: If you can not trust him, I doubt any amount of surveillance can smoothen the friction. How much would anyone let you spy on him, first? You'll already cross the lines like that.
Justification 3: You don't have infinite legal reach. And even if you did, a surveillance like that if does not yield results and is noticed, can lead you well into jail, or worse (read justification 1).
Now, if you still want to spy, the question that requires immediate attention is- are YOU worth it?
-The Joker
Can by done by sending a payload and setting a listener port.
so is it possible or not?
Yes
Share Your Thoughts