What can i do if i have full acces to a wifi?
What is pineapple?
mitm vs metaspoilt?
What is a goodsmartphone for hacking?i was thinking about htc one m7. If i install an OS suite for hacking on an android phone,can i still use it for calling?

What can i do if i have full acces to a wifi?
What is pineapple?
mitm vs metaspoilt?
What is a goodsmartphone for hacking?i was thinking about htc one m7. If i install an OS suite for hacking on an android phone,can i still use it for calling?
 Forum Thread:
Gaining Access into the Victim's Whatsapp on Android
12
Replies
Forum Thread:
Gaining Access into the Victim's Whatsapp on Android
12
Replies Forum Thread:
Whatsapp Hack?
19
Replies
Forum Thread:
Whatsapp Hack?
19
Replies Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
2
Replies
Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
2
Replies Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies Metasploit Error:
Handler Failed to Bind
41
Replies
Metasploit Error:
Handler Failed to Bind
41
Replies Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies How to:
Crack Instagram Passwords Using Instainsane
36
Replies
How to:
Crack Instagram Passwords Using Instainsane
36
Replies Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies How to:
Sign the APK File with Embedded Payload (The Ultimate Guide)
10
Replies
How to:
Sign the APK File with Embedded Payload (The Ultimate Guide)
10
Replies Forum Thread:
How to Run and Install Kali Linux on a Chromebook
18
Replies
Forum Thread:
How to Run and Install Kali Linux on a Chromebook
18
Replies Forum Thread:
How to Find Admin Panel Page of a Website?
13
Replies
Forum Thread:
How to Find Admin Panel Page of a Website?
13
Replies Forum Thread:
can i run kali lenux in windows 10 without reboting my computer
4
Replies
Forum Thread:
can i run kali lenux in windows 10 without reboting my computer
4
Replies Forum Thread:
How to Hack School Website
11
Replies
Forum Thread:
How to Hack School Website
11
Replies Forum Thread:
Make a Phishing Page for Harvesting Credentials Yourself
8
Replies
Forum Thread:
Make a Phishing Page for Harvesting Credentials Yourself
8
Replies How To:
Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
How To:
Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
 How To:
Exploit EternalBlue on Windows Server with Metasploit
How To:
Exploit EternalBlue on Windows Server with Metasploit
 How To:
Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
How To:
Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
 How To:
Enumerate SMB with Enum4linux & Smbclient
How To:
Enumerate SMB with Enum4linux & Smbclient
 How To:
Dox Anyone
How To:
Dox Anyone
 How To:
Use SQL Injection to Run OS Commands & Get a Shell
How To:
Use SQL Injection to Run OS Commands & Get a Shell
 How To:
Bypass File Upload Restrictions on Web Apps to Get a Shell
How To:
Bypass File Upload Restrictions on Web Apps to Get a Shell
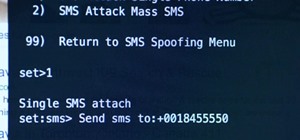 The Hacks of Mr. Robot:
How to Send a Spoofed SMS Text Message
The Hacks of Mr. Robot:
How to Send a Spoofed SMS Text Message
 How To:
Crack SSH Private Key Passwords with John the Ripper
How To:
Crack SSH Private Key Passwords with John the Ripper
 How To:
Scan for Vulnerabilities on Any Website Using Nikto
How To:
Scan for Vulnerabilities on Any Website Using Nikto
 How To:
Find Vulnerable Webcams Across the Globe Using Shodan
How To:
Find Vulnerable Webcams Across the Globe Using Shodan
 How To:
Target Bluetooth Devices with Bettercap
How To:
Target Bluetooth Devices with Bettercap
 How To:
Gain SSH Access to Servers by Brute-Forcing Credentials
How To:
Gain SSH Access to Servers by Brute-Forcing Credentials
 Tutorial:
Create Wordlists with Crunch
Tutorial:
Create Wordlists with Crunch
 How To:
Brute-Force FTP Credentials & Get Server Access
How To:
Brute-Force FTP Credentials & Get Server Access
 How To:
Buy the Best Wireless Network Adapter for Wi-Fi Hacking in 2019
How To:
Buy the Best Wireless Network Adapter for Wi-Fi Hacking in 2019
 How To:
Create Custom Wordlists for Password Cracking Using the Mentalist
How To:
Create Custom Wordlists for Password Cracking Using the Mentalist
 How To:
Run USB Rubber Ducky Scripts on a Super Inexpensive Digispark Board
How To:
Run USB Rubber Ducky Scripts on a Super Inexpensive Digispark Board
 How To:
Clear the Logs & Bash History on Hacked Linux Systems to Cover Your Tracks & Remain Undetected
How To:
Clear the Logs & Bash History on Hacked Linux Systems to Cover Your Tracks & Remain Undetected
 How To:
Perform Local Privilege Escalation Using a Linux Kernel Exploit
How To:
Perform Local Privilege Escalation Using a Linux Kernel Exploit
4 Responses
MITM, spoofing, the options are countless.
A device/router aimed at hacking.
They are two differenti things, it depends on the situation.
Smartphone for hacking? One that supporta monitor mode and has a good processor...
I don't know if you can still use it, I guess so but I don't know...
Male sure there are hacking kernels for the one you are going to choose!
· I've been trying to figure the same thing lately. There are some things to do with Wireshark, there are exploits with Metasploit that don't require social engineering (but I haven't tried yet), and I believe there's the possibility to make fake login websites (such as Facebook's) and auto-redirect the router to your localhost when someone types facebook.com into their browser. Or you could try to get cookie sessions, that'd be more convenient.
· This is a PineAPle. If I lived in the US (or a country with no closed customs, I'd get one to give it a try.
· I've also heard the Nexus phones are great for hacking, if you can afford one. Personally, I own the less hacker-ish phone, a Lumia 720. As far as I know, they're not as vulnerable as iPhone's and Android's, but maybe that's because no one cared to exploit them yet :P
If you are on the LAN you can do whatever you are capable of. You are in a predatory mode since 9/10 times you are undetected upon first arrival.
It depends on why you wanted into the network in the first place. To get free wifi? To make new zombie friends. To gain personal info on the target. To spy on the users. etc.
I would theorize that you would want to see if logging is enabled on the AP. Use -o switch alot for hard copies. Then footprint the network and all devices connected to it. Look for pivots if needed/possible. That's enough of a rough idea.
Long story short I would just init 0 if I didn't know what to do and go back to the dojo.
I think for the phone you could use nexus 5 and one plus one as they support nethunter I think... ( personally I love one plus one)
As for the wifi.. as everyone said their are countless things... think of what u want to do and their is a 80% chanve it can be done :):)
Ill explain easily as easy language is what I know lol:):).. mitm is as its full form says u sit in the middle of user and internet and all things go through you... metasploit is for getting control of the pc... ex - with mitm u can spoof a passwors of user when he inputs in a form... with metasploit u can keylog him... or more easily u can extract the saved password list from his pc!! :):)
Share Your Thoughts