Hello There,
i recently had some questions about hacking
- can i configure the length of a password
- specials tools used for hacking passwords
is there a tool used to define how many characters a passwords consist of like lets take h1king as a password and root_user as the user name of the ftp server and we are trying to brute force the ftp credentials and get server access so is there a way i can find the length of the characters find in the password
E.g. length of characters in the password h1king = 6
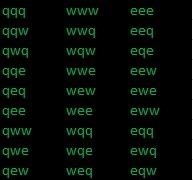
so i have spend some time on software development and hacking but the most common way to hack into a password is using password dictionary or adding phishing into the user and collecting some credentials related with the password but those tools don't seem very effective so is there any tool that could guess all possible outcome of a password (e.g. lets assume a password containing 3 characters /qwe/ and lets suggest the length of the characters would be 3 so the password can only contain 3 types of characters "qwe" and the length of the password should be 3 so the maximum possible outcome of this password would be "number of characters ^length of password" which produces 27 lists of passwords)
this was just a sample of my example so a standard keyboard contains 107 characters and a random strong password contains 12-15 characters so let assume the length of 20 characters password so there will be maximum of 3.8696845e+40 characters this might take a bit long but will be so much effective way to gain credential
or is there a tool used to guess the password character after character like lets take the example h1king
so the tool checks for the first character with trial and error (checks for all 107 characters and moves to the second character when the correct variable is found in this case h) same apply to the other characters
does those dream tools exist
and on many movies like ocean's 8 they use a specific hacking machine for identifying the passwords
take a look at 2:16 does those machine exist or are they just a myth









































1 Response
1) Try not to take hacking advice from media - it is, invariably, an unrealistic depiction of cybersecurity.
2) Try the tool "crunch"
3) True brute force attacks can take up a lot of time, power, and disk space - you're better off selecting another avenue of attack (preferably one that doesn't use brute force at all)
Share Your Thoughts