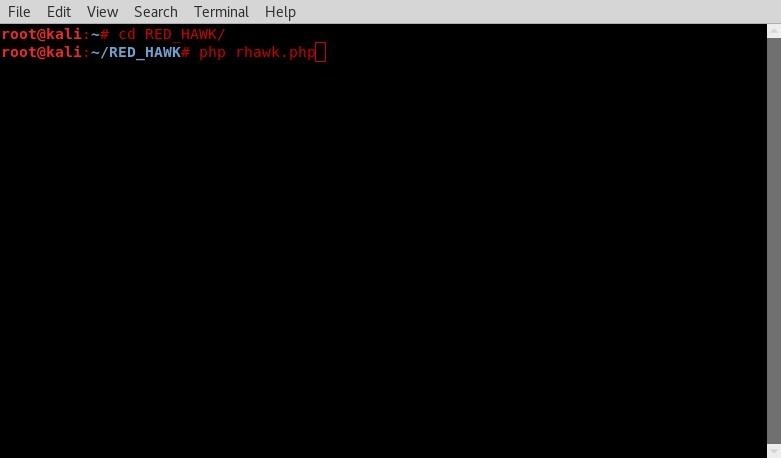
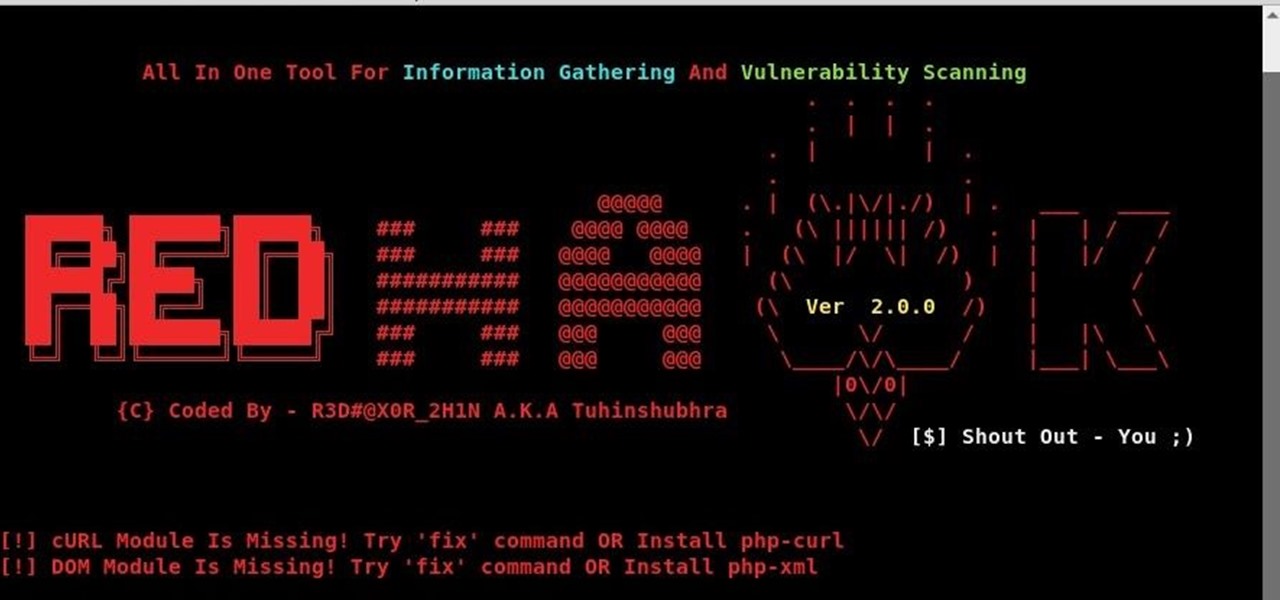
Welcome back hackers and pentesters to a tutorial on an all in one information gathering, and vulnerability analysis with a linux tool called Red Hawk. Recon and mapping out our target is a key step before we begin to hack or exploit anything. This tool helps automate this by seeing what our targeted site is running and if there are any exploits for it. Lets install it from our terminal and change to its directory, and then run it:
git clone github.com/Tuhinshubhra/RED_HAWK
Then change to red hawk directory:
cd RED_HAWK
Now lets run it:
php rhawk.php
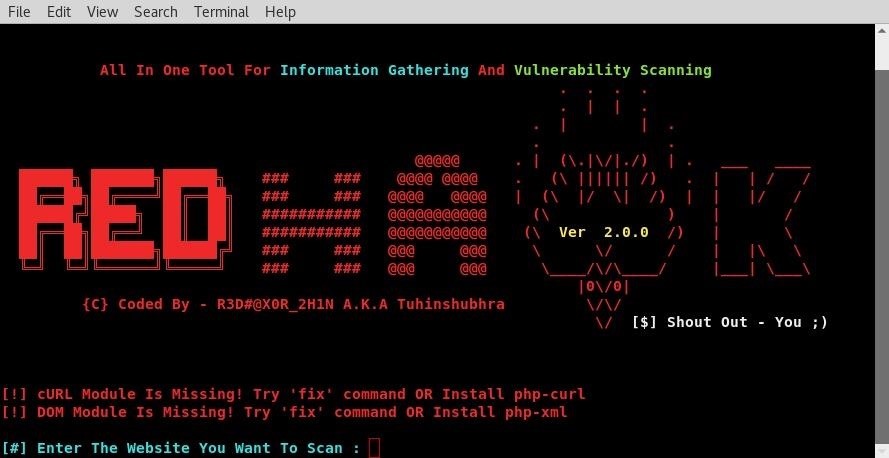
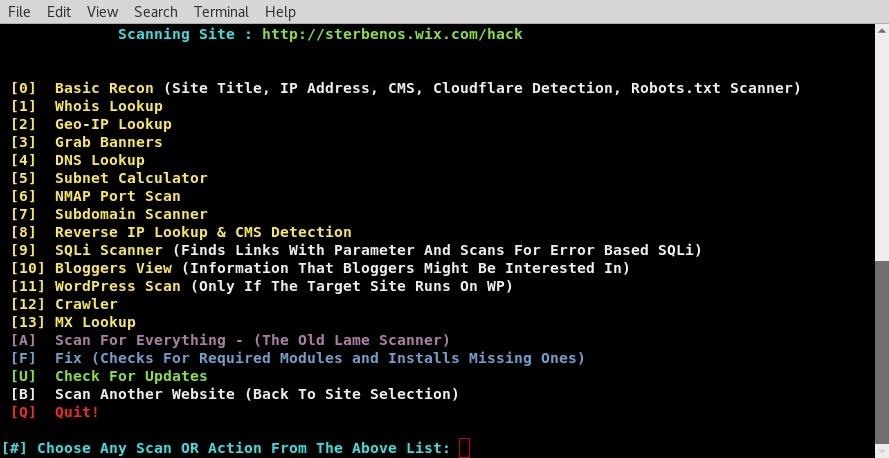
Now enter your website and hit enter. Then specify between whether it uses http or https. We now have options of what we would like red hawk to search for. we are going to go with option one. As mapping out our target site is one of the first steps in pentesting, using red hawk can easily help speed up this process by having these tools in one place.
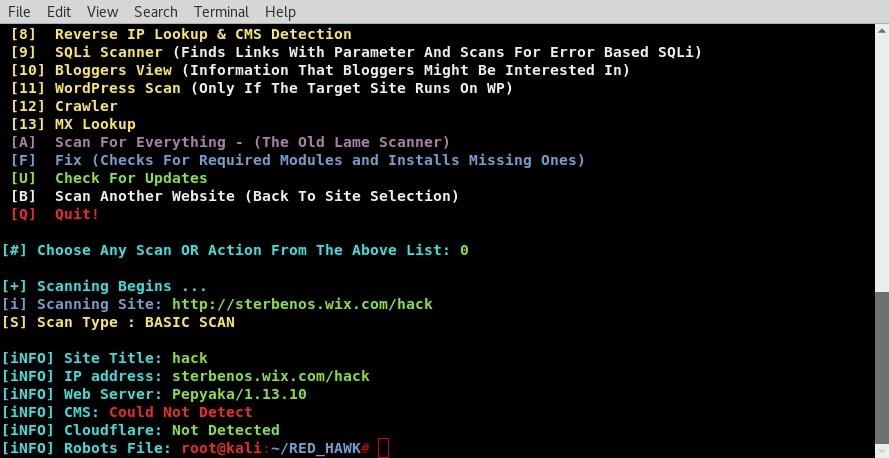
As you can see red hawk has scanned our target site. From these we learned the target site does not use cloudflare ddos protection, runs Pepyaka version 1.13.10 ect. This is all useful information for mapping out target and from there trying to find ways we can attack. To use it agin just enter php rhawk.php from the same terminal. if you closed it change directories to RED_HAWK/ agin. Thats all for today folks, get to scanning !








































1 Response
I don't know if anybody need it because i use a browser extension to see with webserver, cms, etc. is running.
Share Your Thoughts