I was watching this guy on youtube and at 3:50 he talked about an interceptor. Please explain what this is and how to make one.
Forum Thread: What Is an "Interceptor"
- Hot
- Active
-
 Forum Thread:
Gaining Access into the Victim's Whatsapp on Android
12
Replies
Forum Thread:
Gaining Access into the Victim's Whatsapp on Android
12
Replies
10 hrs ago -
 Forum Thread:
Whatsapp Hack?
19
Replies
Forum Thread:
Whatsapp Hack?
19
Replies
12 hrs ago -
 Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
3 days ago -
 Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
2
Replies
Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
2
Replies
3 wks ago -
 Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
3 wks ago -
 Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
2 mo ago -
 Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
2 mo ago -
 Metasploit Error:
Handler Failed to Bind
41
Replies
Metasploit Error:
Handler Failed to Bind
41
Replies
2 mo ago -
 Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
3 mo ago -
 How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
3 mo ago -
 How to:
Crack Instagram Passwords Using Instainsane
36
Replies
How to:
Crack Instagram Passwords Using Instainsane
36
Replies
3 mo ago -
 Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
3 mo ago -
 Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
3 mo ago -
 Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
4 mo ago -
 How to:
Sign the APK File with Embedded Payload (The Ultimate Guide)
10
Replies
How to:
Sign the APK File with Embedded Payload (The Ultimate Guide)
10
Replies
4 mo ago -
 Forum Thread:
How to Run and Install Kali Linux on a Chromebook
18
Replies
Forum Thread:
How to Run and Install Kali Linux on a Chromebook
18
Replies
5 mo ago -
 Forum Thread:
How to Find Admin Panel Page of a Website?
13
Replies
Forum Thread:
How to Find Admin Panel Page of a Website?
13
Replies
6 mo ago -
 Forum Thread:
can i run kali lenux in windows 10 without reboting my computer
4
Replies
Forum Thread:
can i run kali lenux in windows 10 without reboting my computer
4
Replies
6 mo ago -
 Forum Thread:
How to Hack School Website
11
Replies
Forum Thread:
How to Hack School Website
11
Replies
6 mo ago -
 Forum Thread:
Make a Phishing Page for Harvesting Credentials Yourself
8
Replies
Forum Thread:
Make a Phishing Page for Harvesting Credentials Yourself
8
Replies
6 mo ago
-
 How To:
Dox Anyone
How To:
Dox Anyone
-
 How To:
Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
How To:
Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
-
 How To:
Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
How To:
Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
-
 How To:
Crack SSH Private Key Passwords with John the Ripper
How To:
Crack SSH Private Key Passwords with John the Ripper
-
 How To:
Check if Your Wireless Network Adapter Supports Monitor Mode & Packet Injection
How To:
Check if Your Wireless Network Adapter Supports Monitor Mode & Packet Injection
-
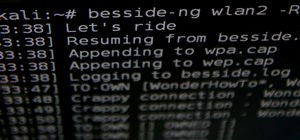 How to Hack Wi-Fi:
Automating Wi-Fi Hacking with Besside-ng
How to Hack Wi-Fi:
Automating Wi-Fi Hacking with Besside-ng
-
 How To:
Crack Shadow Hashes After Getting Root on a Linux System
How To:
Crack Shadow Hashes After Getting Root on a Linux System
-
 How To:
Scan for Vulnerabilities on Any Website Using Nikto
How To:
Scan for Vulnerabilities on Any Website Using Nikto
-
 How To:
Brute-Force Nearly Any Website Login with Hatch
How To:
Brute-Force Nearly Any Website Login with Hatch
-
 How To:
Set Up a Wi-Fi Spy Camera with an ESP32-CAM
How To:
Set Up a Wi-Fi Spy Camera with an ESP32-CAM
-
 How To:
Exploit EternalBlue on Windows Server with Metasploit
How To:
Exploit EternalBlue on Windows Server with Metasploit
-
 How To:
Enumerate SMB with Enum4linux & Smbclient
How To:
Enumerate SMB with Enum4linux & Smbclient
-
 BT Recon:
How to Snoop on Bluetooth Devices Using Kali Linux
BT Recon:
How to Snoop on Bluetooth Devices Using Kali Linux
-
 How To:
Use SQL Injection to Run OS Commands & Get a Shell
How To:
Use SQL Injection to Run OS Commands & Get a Shell
-
 How To:
Automate Wi-Fi Hacking with Wifite2
How To:
Automate Wi-Fi Hacking with Wifite2
-
 How To:
Use Kismet to Watch Wi-Fi User Activity Through Walls
How To:
Use Kismet to Watch Wi-Fi User Activity Through Walls
-
 How to Hack Wi-Fi:
Cracking WPA2-PSK Passwords Using Aircrack-Ng
How to Hack Wi-Fi:
Cracking WPA2-PSK Passwords Using Aircrack-Ng
-
 Hacking macOS:
How to Hack a Mac Password Without Changing It
Hacking macOS:
How to Hack a Mac Password Without Changing It
-
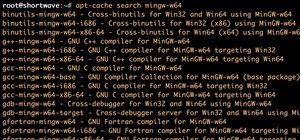
 How To:
Use MinGW to Compile Windows Exploits on Kali Linux
How To:
Use MinGW to Compile Windows Exploits on Kali Linux
-
 How To:
Seize Control of a Router with RouterSploit
How To:
Seize Control of a Router with RouterSploit
















6 Responses
He stated he run the trojan in a virtual machine, so it would not harm his system. He then sniffed for network traffic and saw that screenshot were taken fron his pc to the attacker's server. He then used probably some proxy to DoS him with very large fake screenshots, making his server crash. If you want my guess, he used something like wireshark and paros to get this done.
Funny vid btw. Wannabe scammer got pwned.
How this wouldn't harm his computer because I heard of something called pivoting so the hacker can hack the computers on his network or am I wrong?
But how did he use the proxy and managed to swap out the picture?
Well how could you DoS someone with a picture?
look @ 4:26 ... well if the pic is 850 MB and scammer's server was on a poor connection, it could possibly either clog it, or crash it because it can't handle so much data. We'd need more info on his setup, but let's say it's a custom trojan built by the inexperienced scammer... totally possible to DoS it with a single hhuge image.
Hilarious.
Share Your Thoughts