Can someone explain the stealth methods of the Zeus malware please ?
Forum Thread: Zeus Malware
- Hot
- Active
-
 Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
1 wk ago -
 Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
2
Replies
Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
2
Replies
3 wks ago -
 Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
3 wks ago -
 Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
2 mo ago -
 Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
2 mo ago -
 Metasploit Error:
Handler Failed to Bind
41
Replies
Metasploit Error:
Handler Failed to Bind
41
Replies
2 mo ago -
 Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
3 mo ago -
 How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
3 mo ago -
 How to:
Crack Instagram Passwords Using Instainsane
36
Replies
How to:
Crack Instagram Passwords Using Instainsane
36
Replies
3 mo ago -
 Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
3 mo ago -
 Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
3 mo ago -
 Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
4 mo ago -
 How to:
Sign the APK File with Embedded Payload (The Ultimate Guide)
10
Replies
How to:
Sign the APK File with Embedded Payload (The Ultimate Guide)
10
Replies
4 mo ago -
 Forum Thread:
How to Run and Install Kali Linux on a Chromebook
18
Replies
Forum Thread:
How to Run and Install Kali Linux on a Chromebook
18
Replies
5 mo ago -
 Forum Thread:
How to Find Admin Panel Page of a Website?
13
Replies
Forum Thread:
How to Find Admin Panel Page of a Website?
13
Replies
6 mo ago -
 Forum Thread:
can i run kali lenux in windows 10 without reboting my computer
4
Replies
Forum Thread:
can i run kali lenux in windows 10 without reboting my computer
4
Replies
6 mo ago -
 Forum Thread:
How to Hack School Website
11
Replies
Forum Thread:
How to Hack School Website
11
Replies
6 mo ago -
 Forum Thread:
Make a Phishing Page for Harvesting Credentials Yourself
8
Replies
Forum Thread:
Make a Phishing Page for Harvesting Credentials Yourself
8
Replies
6 mo ago -
 Forum Thread:
Creating an Completely Undetectable Executable in Under 15 Minutes!
38
Replies
Forum Thread:
Creating an Completely Undetectable Executable in Under 15 Minutes!
38
Replies
7 mo ago -
 Forum Thread:
Hacking with Ip Only Part [1] { by : Mohamed Ahmed }
5
Replies
Forum Thread:
Hacking with Ip Only Part [1] { by : Mohamed Ahmed }
5
Replies
8 mo ago
-
 How To:
Scan for Vulnerabilities on Any Website Using Nikto
How To:
Scan for Vulnerabilities on Any Website Using Nikto
-
 How To:
Crack Shadow Hashes After Getting Root on a Linux System
How To:
Crack Shadow Hashes After Getting Root on a Linux System
-
 How To:
Find Vulnerable Webcams Across the Globe Using Shodan
How To:
Find Vulnerable Webcams Across the Globe Using Shodan
-
 How To:
Find Passwords in Exposed Log Files with Google Dorks
How To:
Find Passwords in Exposed Log Files with Google Dorks
-
 How To:
Spy on Traffic from a Smartphone with Wireshark
How To:
Spy on Traffic from a Smartphone with Wireshark
-
 How To:
Dox Anyone
How To:
Dox Anyone
-
 How To:
Use SQL Injection to Run OS Commands & Get a Shell
How To:
Use SQL Injection to Run OS Commands & Get a Shell
-
 How To:
Get Root with Metasploit's Local Exploit Suggester
How To:
Get Root with Metasploit's Local Exploit Suggester
-
 How To:
Top 10 Things to Do After Installing Kali Linux
How To:
Top 10 Things to Do After Installing Kali Linux
-
 Hack Like a Pro:
Reconnaissance with Recon-Ng, Part 1 (Getting Started)
Hack Like a Pro:
Reconnaissance with Recon-Ng, Part 1 (Getting Started)
-
 How To:
Phish for Social Media & Other Account Passwords with BlackEye
How To:
Phish for Social Media & Other Account Passwords with BlackEye
-
 How To:
Use Kismet to Watch Wi-Fi User Activity Through Walls
How To:
Use Kismet to Watch Wi-Fi User Activity Through Walls
-
 How To:
Hack 5 GHz Wi-Fi Networks with an Alfa Wi-Fi Adapter
How To:
Hack 5 GHz Wi-Fi Networks with an Alfa Wi-Fi Adapter
-
 How To:
Automate Wi-Fi Hacking with Wifite2
How To:
Automate Wi-Fi Hacking with Wifite2
-
 How To:
Hack Coin-Operated Laudromat Machines for Free Wash & Dry Cycles
How To:
Hack Coin-Operated Laudromat Machines for Free Wash & Dry Cycles
-
 How To:
The Top 80+ Websites Available in the Tor Network
How To:
The Top 80+ Websites Available in the Tor Network
-
 Android for Hackers:
How to Exfiltrate WPA2 Wi-Fi Passwords Using Android & PowerShell
Android for Hackers:
How to Exfiltrate WPA2 Wi-Fi Passwords Using Android & PowerShell
-
 How To:
Clear the Logs & Bash History on Hacked Linux Systems to Cover Your Tracks & Remain Undetected
How To:
Clear the Logs & Bash History on Hacked Linux Systems to Cover Your Tracks & Remain Undetected
-
 How To:
Set Up a Wi-Fi Spy Camera with an ESP32-CAM
How To:
Set Up a Wi-Fi Spy Camera with an ESP32-CAM
-
 Hacking Windows 10:
How to Create an Undetectable Payload, Part 1 (Bypassing Antivirus Software)
Hacking Windows 10:
How to Create an Undetectable Payload, Part 1 (Bypassing Antivirus Software)
















6 Responses
This is from http://www.wiki-security.com/wiki/Parasite/ZeusTrojan/
The Stealth Strategies of the Zeus Trojan
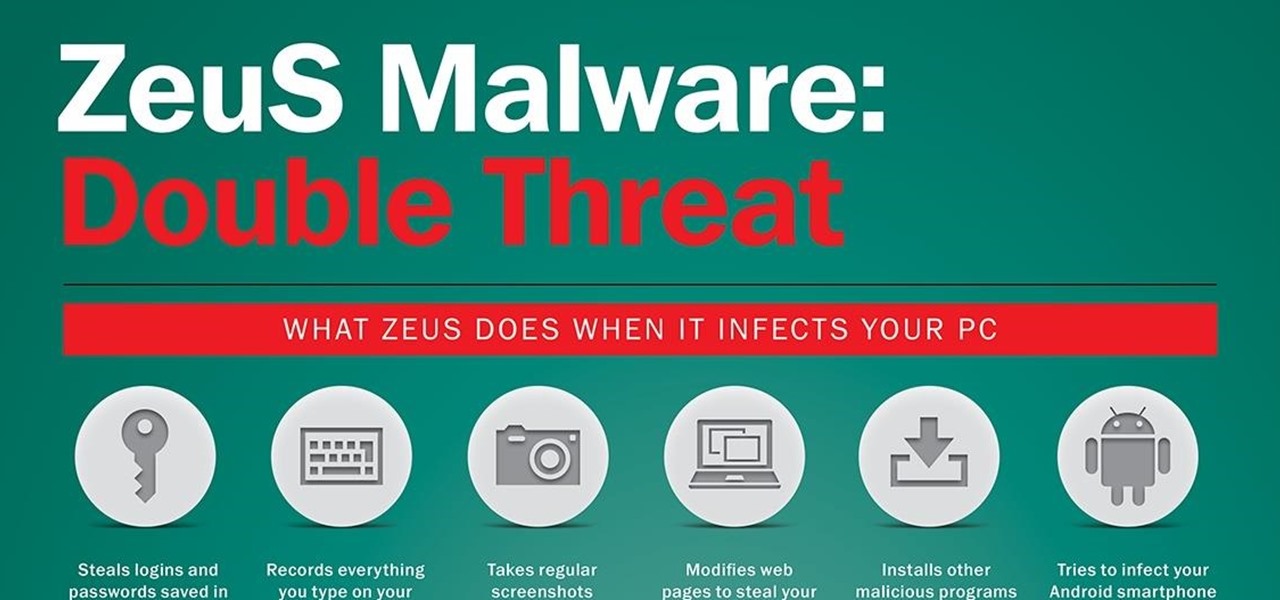
The Zeus Trojan steals personal data such as email passwords and financial information such as online banking passwords. Hackers use the Zeus Trojan to steal information and send such information to remote servers. Furthermore, these cybercriminals use the information to log into online banking accounts and make unauthorized money transfers through a complex and stealthy network of money mules. The Zeus Trojan may be spread through drive-by downloads or via phishing messages sent through emails or social networks like Facebook. Even just the simple clicking of a corrupt email link can install this Trojan instantly in any PC or mobile phone.
Just FYI, A money mule is a person who transfers stolen money between different countries. From http://www.actionfraud.police.uk/fraud-az-money-muling
That's my question, what do they mean by "stealthy network" , how those hackers did it ?
The Zeus Trojan uses file names such as PP06.EXE, PP08.EXE, NTOS.EXE, LD08.EXE, LD12.EXE, LDnn.EXE and PPnn.EXE. Many infections have also been traced to the presence of a WSNPOEM folder. From http://www.wiki-security.com/wiki/Parasite/ZeusTrojan/
"They are victims in a crime. So if they don't know they are doing it" , you mean they did it by luck ?!
"how can an agency track down who is actually doing it" , that means they are idiots! I doubt that's right!
From https://paulsinternetsecurityblog.wordpress.com/2013/03/19/zeus-banking-trojan-now-in-rootkit-form/
Encrypts its communication with its controlling computer so that
security analysts can't track them.
Protects the identity of its controlling computer.
Adds additional malware onto the computer in which it resides.
Hides itself from even the best anti-malware software.
Also, I suggest you read the following document. Long story short, the "employee" is tricked into performing a wire transfer to a third party that the criminal is associated with. The money mules is used once then all relationships are no more. This process hides the criminals involvement. https://www.us-cert.gov/sites/default/files/publications/money_mules.pdf
Thank you!
I certainly will.
Share Your Thoughts