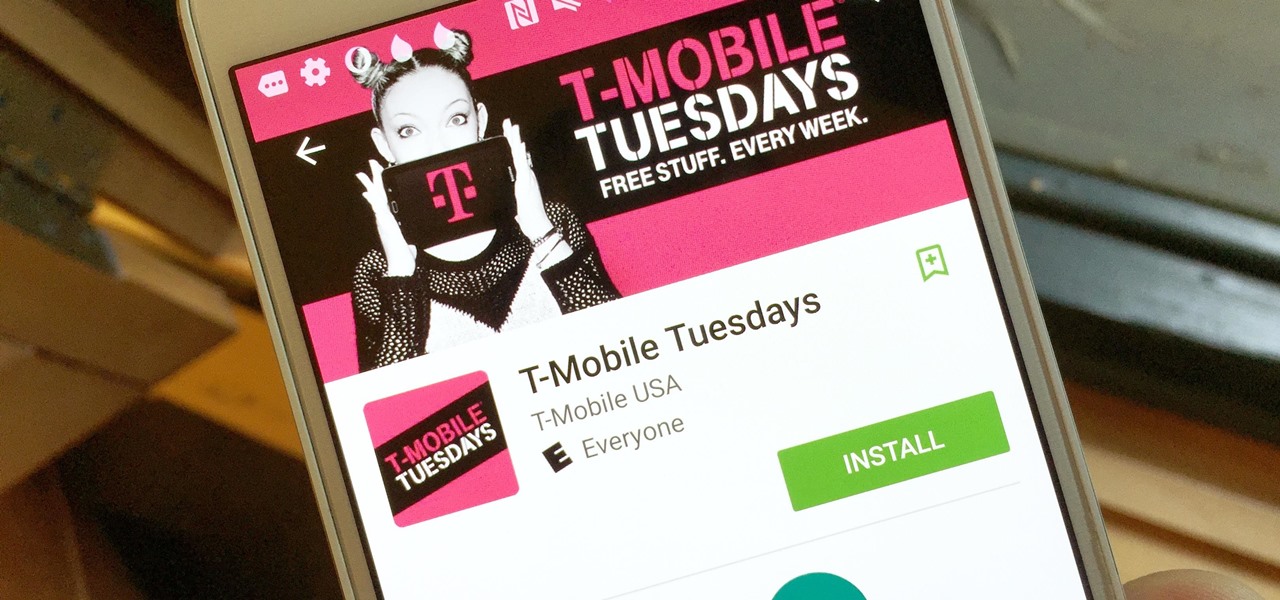
T-Mobile is going for broke. The carrier recently announced it will be giving away free stuff to its customers every Tuesday through a new app called T-Mobile Tuesdays for Android and iOS, and that's in addition to one share of stock and free in-flight Wi-Fi.

The app will give out "food, movie tickets, gift cards, subscriptions, ridesharing, and more," the announcement said. You just have to be the primary account holder and you're good to go. One person will win a huge prize every Tuesday, like a trip for two to Vegas or an expedition to Machu Picchu. And this will hopefully go on for a long time, since the giveaways will continue "until further notice."



The app is part of a new "Un-carrier 11" program that aims to just shower customers in cool free stuff. Beyond T-Mobile Tuesdays, they're giving away one share of T-Mobile stock to primary account holders (worth about $43 at the time of this writing) along with one free hour of in-flight Wi-Fi through GoGo, every time you fly.
Everything rolls out tomorrow, and if you're hungry for the stock, it's only available through June 21st. You can check out the terms for more details, and if you want even more freebies, we've got a good list of free stuff from carriers you should check out.
Just updated your iPhone? You'll find new emoji, enhanced security, podcast transcripts, Apple Cash virtual numbers, and other useful features. There are even new additions hidden within Safari. Find out what's new and changed on your iPhone with the iOS 17.4 update.























Be the First to Comment
Share Your Thoughts