This is my first article on here, it's based off of a project that I'm working on at school which is on three ways to bypass windows user password's. If all goes as planned and you all would like I'll work on part two and part three and post them as soon as I can. I do have to give credit to Puppy Monkey Baby and The Defalt, both of whom are my classmates at college and have helped me with writing this article.
Booting into Kali/Parrotsec and Navigation to SAM
In Part 1 we will focus on using Kali Linux or Parrotsec to remove the password of a specific user in the SAM file. We will need a bootable usb with your choice of operating system so that we can boot directly into Kali/Parrotsec. Once we have booted into our flavor of linux, we need to mount the local hard drive. We must mount before we can have access to the hard drive or it will not show up. To mount simply click on Places > Home > "Primary Hard Disk"(This name will vary with each computer.)
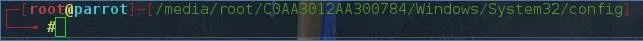
After we have accomplished this the next step is to open up a terminal. At this point we need to change directory using the cd command, to root. Now all we need to do is navigate to the place on the hard drive that contains the password information. Navigating to the location can get tricky for new users. The ls command is incredibly helpful with finding out what files and folders are located in the directory that we are currently in. Once we navigate to the config folder your location should look something like the image below. (Once again the name of the hard drive you are accessing will vary by system.)
Selecting the User
Our next act will be to use the chntpw -l SAM command without the brackets. What this command does is it lists the users and the corresponding permissions level. The very important part that we need to be aware of is the RID. The RID is what we will be using to specify which user account that we are going to modify.
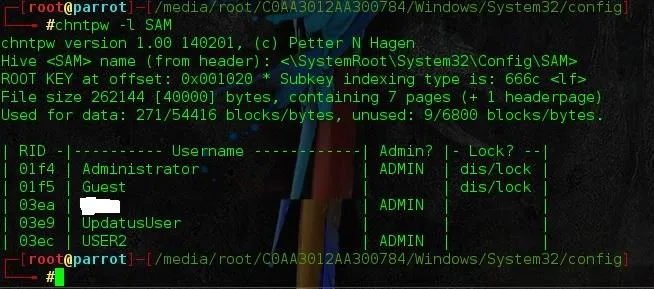
In this case we are going after USER2, so the RID we need is 03ec.
Removing the Password
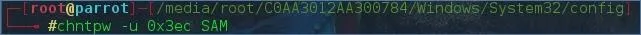
When we are sure of which user account that we want to modify we use the chntpw -u 0x03ec SAM command. It is very important that we put the 0x before the 03ec because if it's not there the command will not be recognized.
After we execute that command we will be presented with choices of what to do with that particular user.
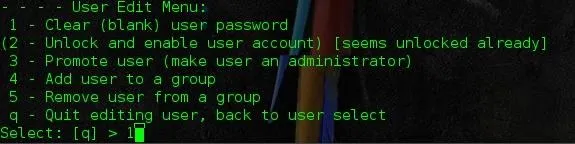
As shown above we want to choose the 1 option to remove the password. After that it will ask if we want to write to hive files. Type y otherwise all the work we have done will go out the window and we will have to re-execute the commands. Once this is done then reboot and if everything was done correctly, the user we chose should not have a password. If it still does then unfortunately we will have to redo all of the steps above. At this point I have only done this on Windows 7, I will be trying all three methods on my windows 10 laptop and update with the results.
Why Would We Need to Know These Technique's?
If we are working in an office as a tech there will inevitably be an occurrence of an end user forgetting a password. Now depending upon the organization that you are working for, there might be policies in place that allow for bypassing or disallow it altogether. Ethically we are bound by these policies. On the other hand lets say we are in class and feel like messing with a fellow classmate by changing their background or any other pranks (not that PMB nor I have any experience in this), these technique's will come in handy.
-Skrub

























Comments
Be the first, drop a comment!