This is the second installment of the short series on how to remove user passwords in Windows. Once again this has only been tested on Windows 7. If I can find some time between two jobs and school I'll test all the ways on Windows 10 and Windows 8/8.1.
Startup Repair
The route of using the command line can be a little more complex than the other two ways. On the other hand it can be more simple in that we don't need to rely on having a bootable usb, everything we need is already installed on the machine. Our first step is to force the computer into its startup repair mode. To do this we need to boot the computer up and the moment that the Windows logo appears perform a hard reset. In short, hold down the power button down until it turns off completely. Next, reboot the computer and let it load up until you get a screen like below.
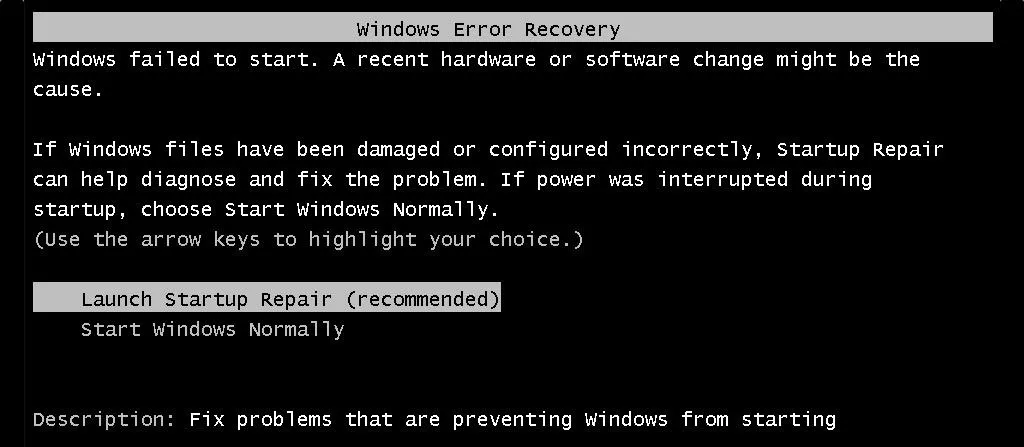
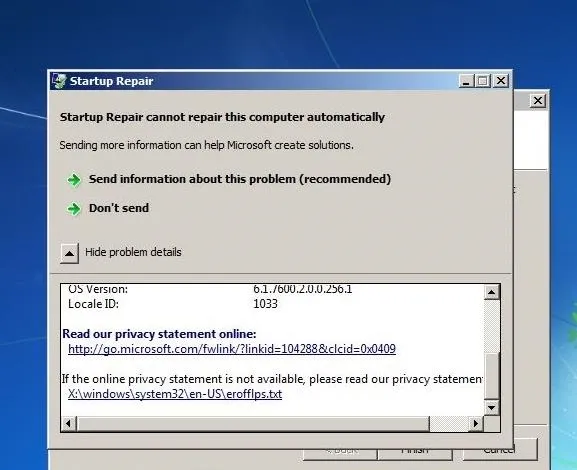
The option that we want to choose is Launch Startup Repair. Let it run its course and when we get a pop up window that says "Startup Repair cannot repair this computer automatically." there will be a button with a down arrow on it with text to the right that says "View problem details.". Once you locate that arrow click on it and scroll all the way to the bottom. There will be a link that looks like the one in the picture below.
Navigating and Renaming
Click that link and it will open up a text file. We don't care about the contents of the file, rather we use it as a path to the next step. Go to File and click Open. What this does is give us a way to access the System32 file. But before we get to that point go ahead and change the type of file from Text Documents to All Files. This is very important in that if we don't do this we won't be able to see the files that we need to rename. Once that is done in the left hand pane click on Computer. The next series of steps is literally just clicking to navigate to System32. The order should go something like Local Disk>Windows>System32.
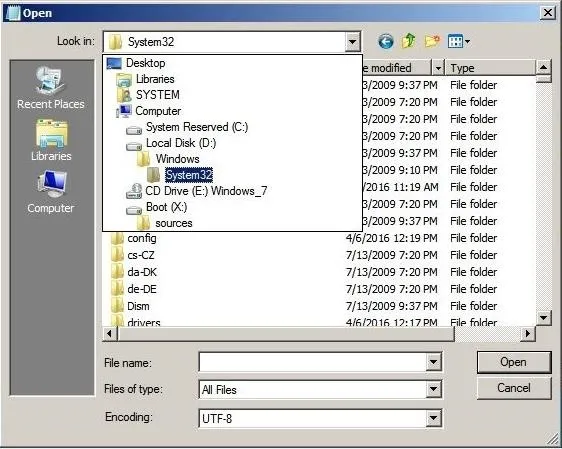
Once we are here we need to find the cmd executable and sethc. In short, we are going to rename them with each others name. It is very important to rename one of them a variation of one of their names before you try to give either one the specific name. For instance, I renamed cmd to sethc1 then renamed sethc to cmd and then back to sethc1 and removed the 1. Now I'm sure that there is a more streamlined way to do this but it's just how I did it this time. Once we have accomplished this back out of where you are and restart the computer.
Changing the Password Using Command Prompt
As it boots let it go to the login screen like a normal boot up. Instead of putting in a password as usual, we are going to hit the right shift key five times. What this does is brings up a command prompt window. In the newly opened command prompt window type in the command net user (username)(password). It is very important to note that the username is the user we are trying to access and the password is whatever we want the new password to be.
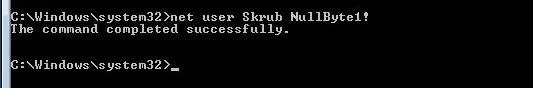
In this example I have chosen to go for the User Skrub and make the Password NullByte1! If we're successful the response will look like the one above. Now we can log in with your new password.
Cleaning Up
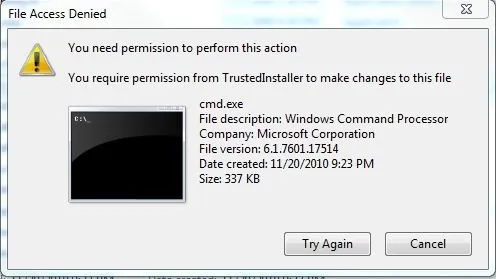
Don't forget that we need to revert the names of the files to their original. If we try to rename it while logged on to the user we get an error that looks like the picture below.
For us to successfully rename the programs back all we need to do is run startup repair again and it will be reverted to original. That's it! We've successfully created a new password, gained access to the user, and reverted the changes that we had to make in the process. Thanks for reading!

























Comments
Be the first, drop a comment!