Welcome back, rookie hackers!
We recently began an exploration of ways to hack using the Bluetooth protocol. As you know, Bluetooth is a protocol that connects near field devices such as headsets, speakers, and keyboards. Its minimum range is a 10-meter radius (~33 feet) and maximum is at 100 meters (~328 feet).
I already explained the basics of Bluetooth technology in my first article in this series, and even showed off how Elliot used Bluetooth hacking in Mr. Robot. In this article, we will examine the use of the MultiBlue Dongle.

This dongle is capable of connecting to any Bluetooth device and enabling you to use your computer keyboard to control the device. Ostensibly developed and sold to enable users to use their computer keyboard and mouse on their mobile device, as you can imagine, it can be used for more surreptitious activities. It's available from many retailers including Amazon.com for about $35
In this tutorial, we will need physical access to the device, but as we expand and deepen your knowledge of Bluetooth, we will work toward using this dongle to control Bluetooth devices without physical access.
Although Bluetooth is limited to 10-100 meters, that is more than enough to cover most homes, neighborhoods, offices, libraries, schools, coffee shops, etc. With an antenna, this range can be extended. Now let's see how to connect to an Android device and control it via your computer keyboard.
Human Interface Device
HID, or human interface device, is a protocol of those devices that work directly with the human. Such things as monitors, keyboards, and microphones all fit into this category. With the MultiBlue Dongle, we will be using the HID protocol to send keyboard and mouse input through the Bluetooth protocol to the target system
Insert into Your Computer
The MultiBlue Dongle was developed to work with either Windows or Mac OS X operating systems. In this tutorial, I will be using it on a Windows 7 system. If you only use Linux, you can use it with Wine.
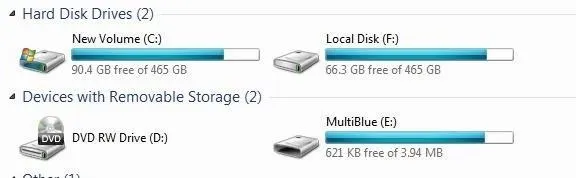
MultiBlue doesn't need any drivers as everything it needs is installed on the dongle. The dongle is actually a 4 GB thumb drive with Bluetooth capabilities. Simply place it in any USB slot on your computer.
Enable MultiBlue
Once you plug MultiBlue into your system, it will appear just like any other USB flash drive. Click on the MultiBlue icon and it will open a subdirectory showing two choices, Win and Mac. Click on Windows.
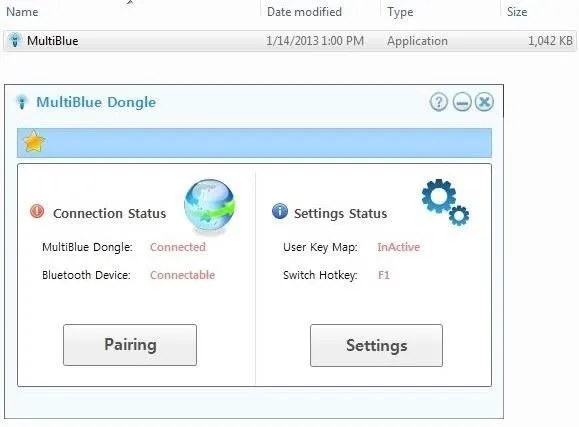
When you do so, it will activate the MultiBlue application as seen below.
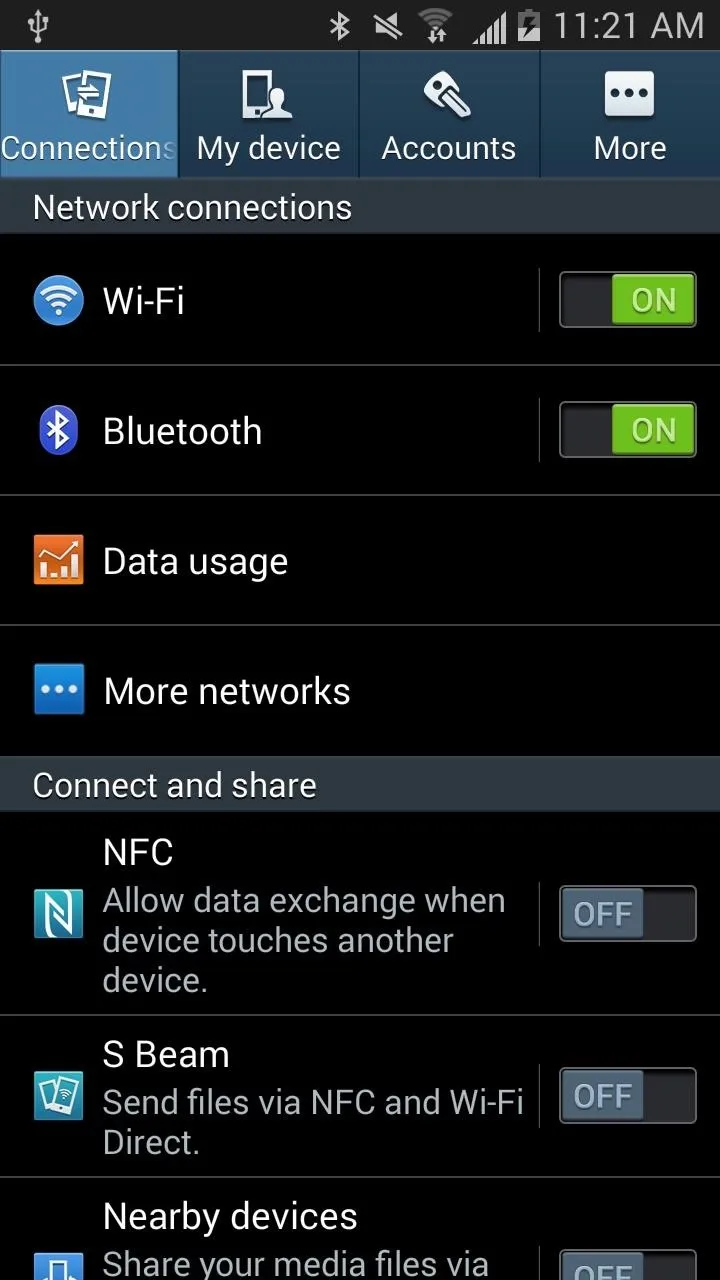
Place the Device in Discoverable Mode
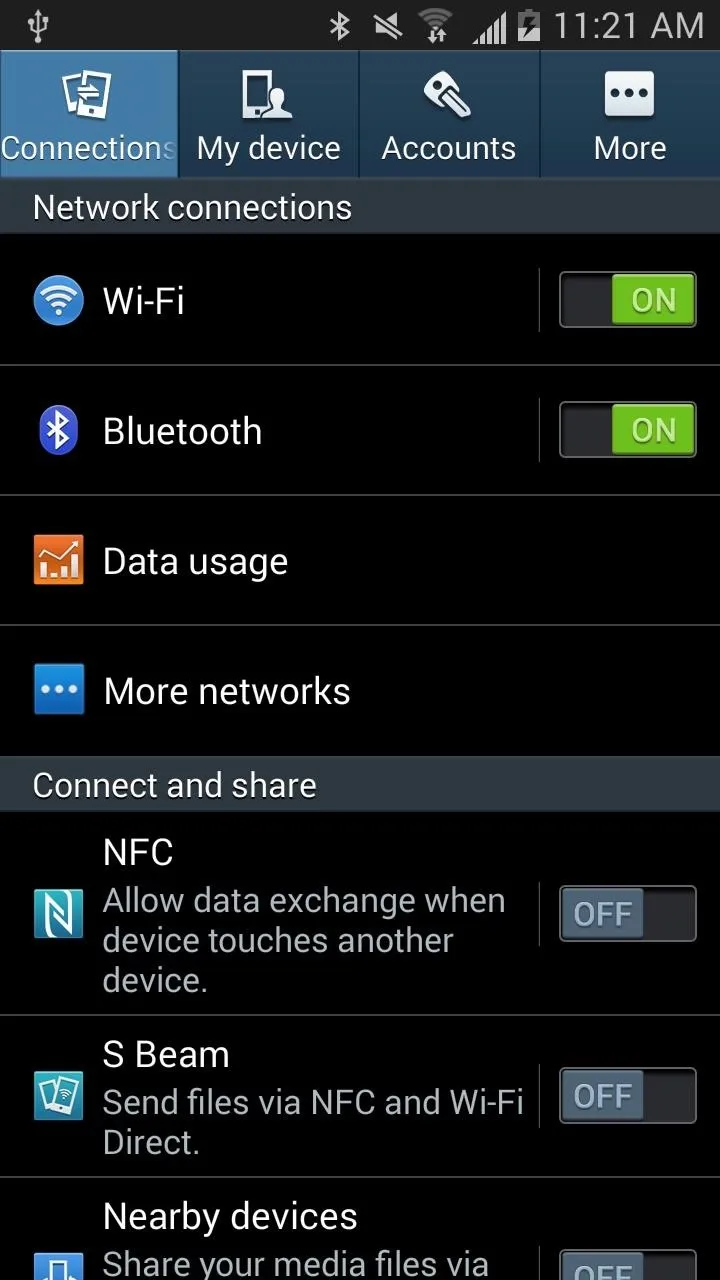
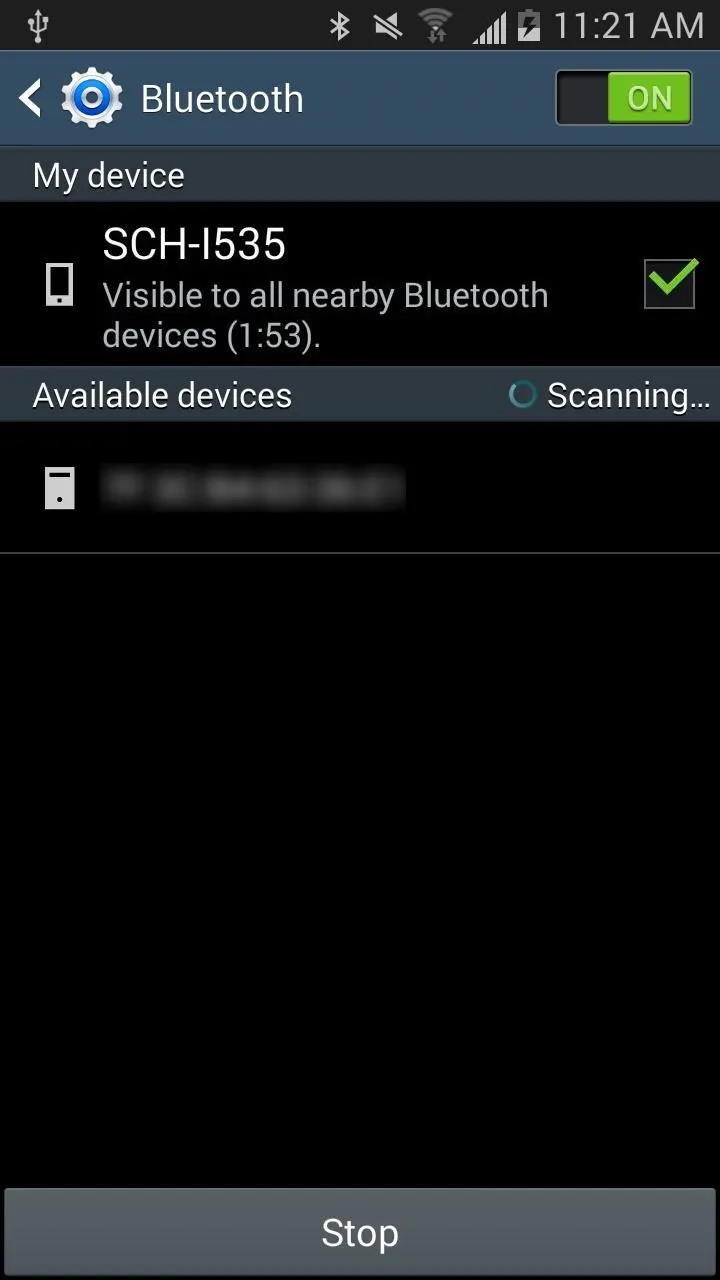
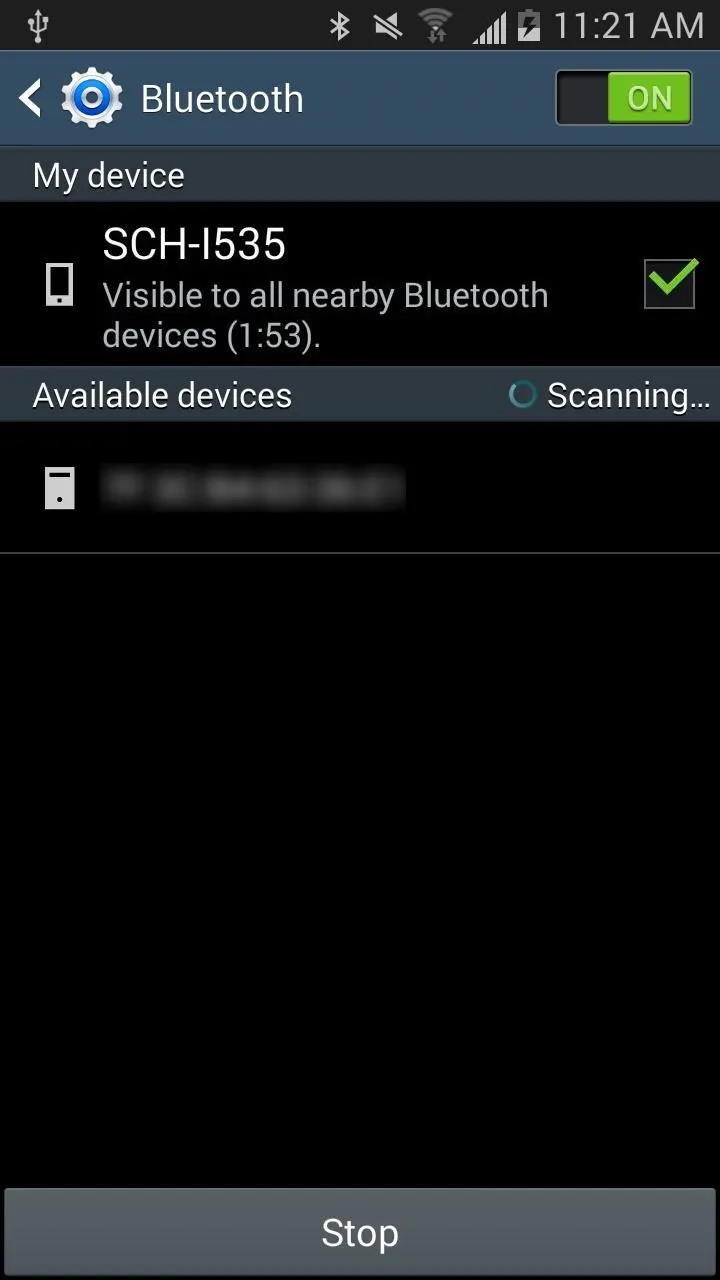
Now, we need to place the Bluetooth-enabled target mobile device in discoverable mode. As you can see below, this Android phone is now in discoverable mode for 2 minutes.
Pair & Get the Pin
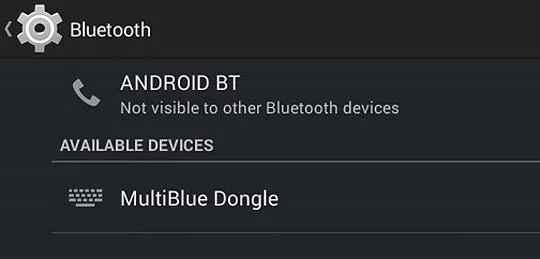
The mobile device will now get a paring request from MultiBlue as seen below. Accept the pairing request.
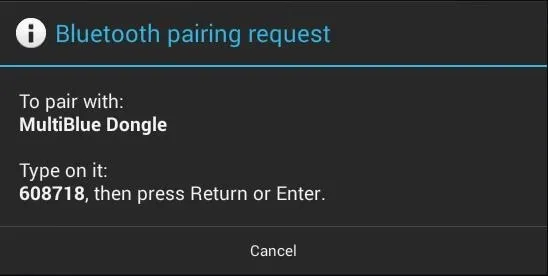
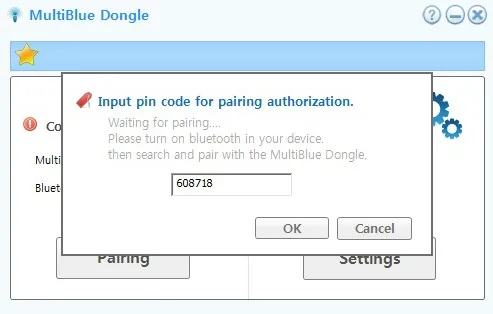
When you do so, the mobile device will present you with a numeric code as seen below. You will need to enter this code into the MultiBlue application on the Windows system. As you might have guessed, this numeric code is the pre-shared key that is critical to Bluetooth authentication and encryption. We will see in later posts here in Null Byte that we can get this code in various ways (e.g., sniffing) without having physical access to the phone.
In addition, notice that the MultiBlue Dongle announces itself as the "MultiBlue Dongle" to the pairing system. We will see in a later tutorial that we can spoof that name to something that seems safe to the target such as "My iPod" or "My Speakers," fooling the user that it is their device they are seeking to pair.
Now we enter the code into the MultiBlue application, as mentioned above.
When we're done, MultiBlue responds showing us that the device has been paired.
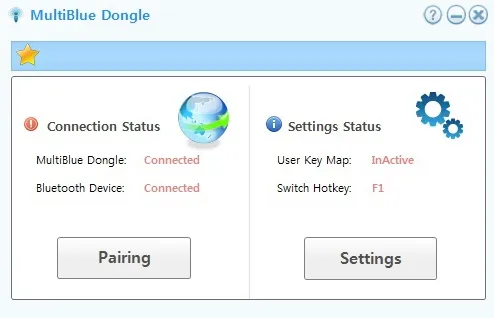
Now, we have both our keyboard and mouse to control of the phone or tablet!
How to Use It
Now that we have control of the device, we can do just about anything we want with it (while it is in range). One of the things we may want to do is download the mobile device spyware that I demonstrated here in this article. In addition, we may want to open a terminal to run in the background so that we can use it (when in range).
Now that we know we can control the device with the MultiBlue Dongle, we will work towards being able to do that same thing without physical access and without the MultiBlue. So keep coming back, my rookie hackers!
Cover image via MultiBlue Dongle

























Comments
Be the first, drop a comment!