Welcome back, my amateur hackers!
As many of you know, Null Byte will soon be re-establishing its IRC channel. In preparation of that event, I want to show how to set up a secure IRC client with OTR, or Off the Record.
OTR does all the right things to make your instant messages secure; AES encryption, Diffie-Hellman key exchange, and SHA-1 hash. If you don't know what those items are, check out my article on Cryptography Basics for the Aspiring Hacker.
OTR provides us the security we need to communicate freely:
- Authentication: You can be certain the person you are talking to is who they say they are.
- Deniability: After a chat session ends, no one can identify either end of the conversation.
- Encryption: No one can read your messages en route.
- Perfect Forward Security: If your private keys are intercepted or otherwise obtained by a third party, your previous conversations will not be compromised.
If you need any testimonials as to the security of OTR, when Edward Snowden was being hunted down by the NSA in Hong Kong and Russia, he would ONLY communicate by OTR and, of course, he remained free. If that's not a testimonial to its security, I don't know what would be.
OTR is really a protocol for secure IRC communication. As such, many IRC clients use OTR if properly configured, while others require a plugin to use OTR. In this tutorial, we will be installing Pidgin with the OTR plugin.

Install Pidgin with OTR
The first thing we need to do is install a client with OTR. I have chosen Pidgin because it is widely used and has an OTR plugin. Of course, many other IRC clients have OTR plugins and you are free to use those.
We can get Pidgin and OTR together from the Kali repository by typing;
kali > apt-get install pidgin-otr
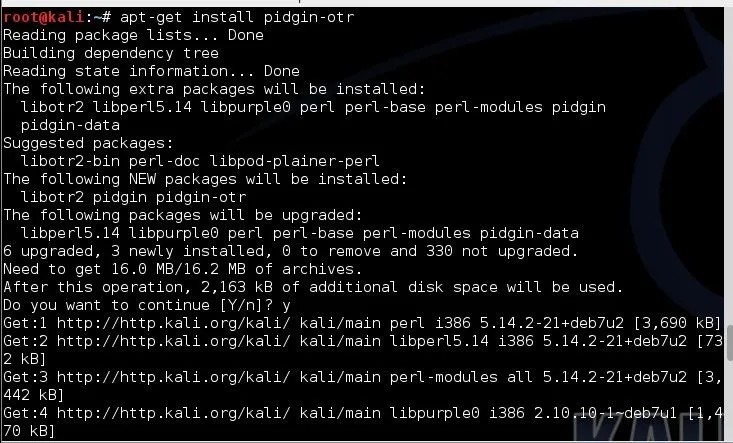
As it installs, it will look something like this. Make certain to answer "y" when prompted.
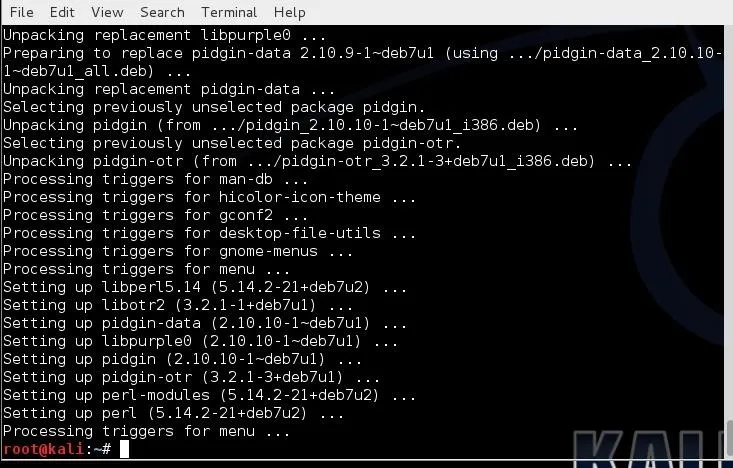
When it has completed installing all the necessary components and libraries, it will look something like the above.
Open Pidgin
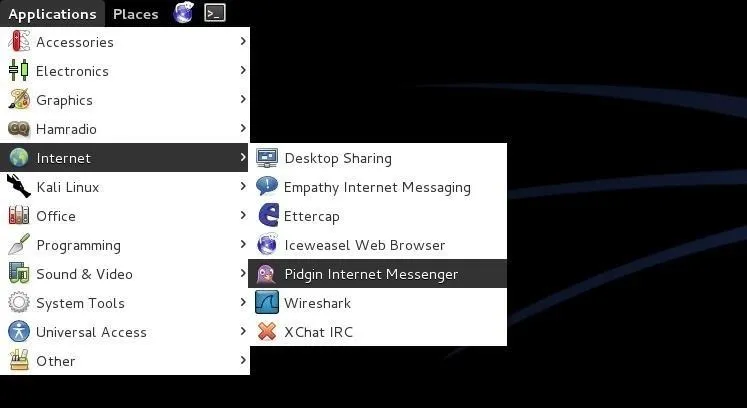
Now that we have installed Pidgin, it will be installed on our Kali GUI at Applications -> Internet -> Pidgin Internet Messenger, as seen below.
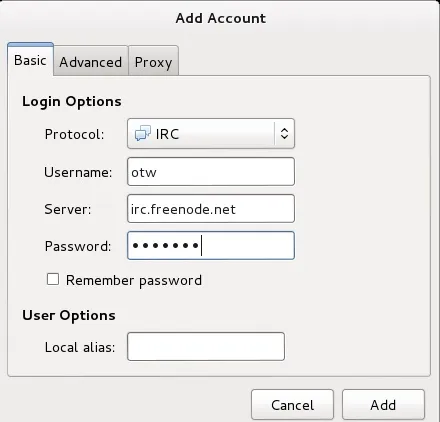
When you click on Pidgin, you will be greeted by a screen like that below—click on Add to add an account to Pidgin.

Add Accounts
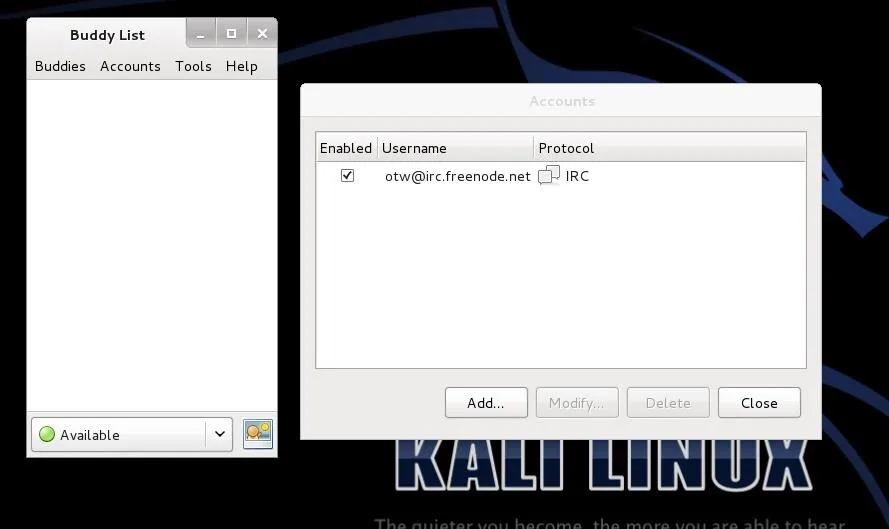
In this case, I am adding my IRC (protocol) account under the username "otw" to the freenode.net server. Of course, use your own username and password. Also, you can use the Pidgin client on any "chat" protocol including AIM, Google Talk, ICQ, MSN, Yahoo, and others.
When I click "Add," it opens a Buddy List and a screen to enter more accounts.
Add the OTR Plugin
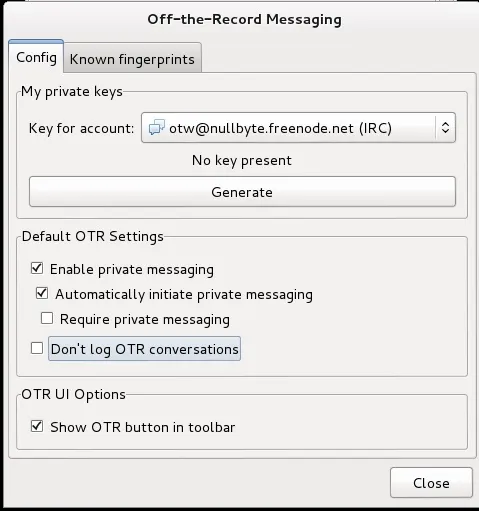
Next, we need to add the OTR plugin to our Pidgin client. On the Buddy List, click on Tools -> Plugins -> Off-the-Record, then click "Configure Plugin."
Now check the button next to the OTR then click close, and close again to enable the plugin. Make certain that the checkboxes "Enable private messaging" and "Automatically initiate private messaging" are checked. Then will automatically encrypt your communication when using this client. I would also suggest that you check "Don't log OTR conversations" so that no record exists of your conversation
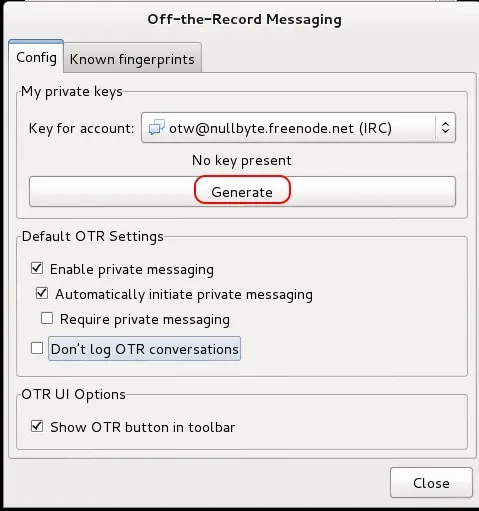
Lastly, we need to generate private keys. From the same OTR Plugin configuration screen, click on the "Generate." Be patient, this can take awhile.
Now we are capable of safe and secure IRC and other chats knowing that no one can intercept and read our conversations. That should enable us to speak freely about any subject without fear of repercussions.
In my next article on OTR, I will show you how to authenticate a user with OTR in our Pidgin client so that you can be certain that the person you are communicating with is actually who they say they are, so keep coming back my amateur hackers!

























Comments
Be the first, drop a comment!