Welcome back, my novice hackers!
The worst thing that can happen to any hacker is being detected by a security admin, the security technologies (IDS, firewall, etc.), or a forensic investigator.
Every time we send a packet to our intended target, that packet contains our IP address in the IP header. When we make a TCP connection, the target system will log our IP address as it logs all connections. If we set off any security alarms or alerts, our IP address will be logged. All of these events increase the possibility of detection.

In order to hack anonymously with the least chance of detection, we need to use an intermediary machine whose IP address will be left on the target system. This can be done by using proxies.
These systems are designed to accept our traffic and then forward it on to the intended target. Of course, the proxy will likely log our traffic, but an investigator would have to get a subpoena or search warrant to obtain the logs.
If we string multiple proxies in a chain, we make it harder and harder to detect our original IP address. If one of those proxies is outside the jurisdiction of the victim, it makes it very unlikely that any traffic can be attributed to our IP address.
Both Kali and BackTrack have an excellent tool for proxying our traffic called proxychains. In this tutorial, I will show how to use this simple, but powerful tool.
Find Proxychains
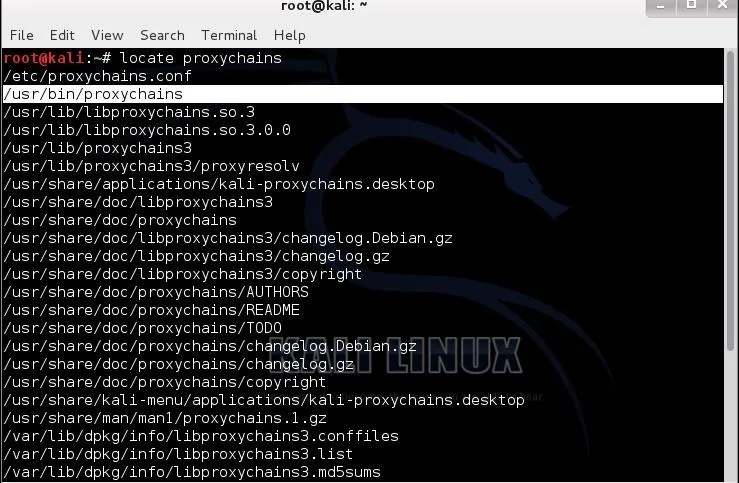
Let's start by finding proxychains. Type:
- kali > locate proxychains
As we can see in the screenshot below, proxychains is in the /usr/bin directory. Since /usr/bin is in our PATH variable, we can use it from any directory. This is just as we would want since we use proxychains with other commands, which may NOT likely be in the PATH variable.
Proxychains Syntax
The syntax for the proxycahins command is simple and straightforward.
- kali> proxychains
So, if I wanted to use proxychains to scan a site with nmap anonymously, I could type:
- kali> proxychains nmap -sS
Set Up the Config File
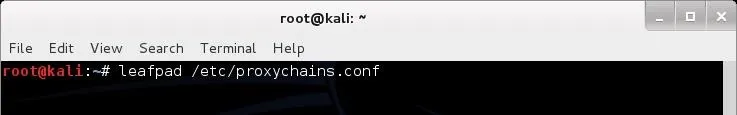
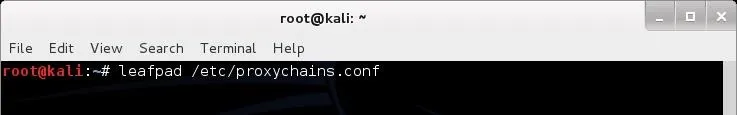
Like nearly every application in Linux/Unix, configuration is managed by a simple text file called the config file. In the case of proxychains, this file is /etc/proxychains.conf. We can open it in leafpad or any other text editor (vi, emacs, gedit, kwrite, etc.), by typing:
- kali > leafpad /etc/proxychains.conf
When we do so, we will see a file like that displayed below. If we scroll down this file a bit, we will see a section that I have highlighted labeled "add proxy list here...".
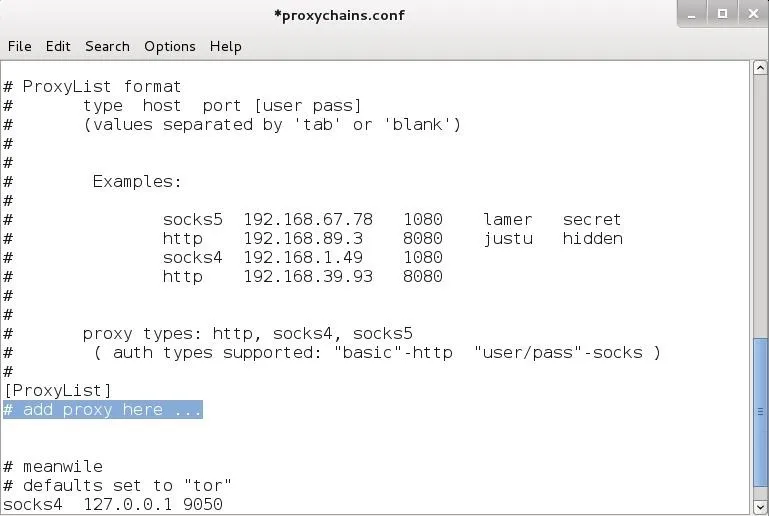
To get proxychains to use intermediary proxies, we simply need to add the IP addresses of the proxies we want to use here. It's important to note that proxychains defaults to use Tor.
Notice the last line in the screenshot above. It directs proxychains to send the traffic first through our host at 127.0.0.1 on port 9050 (the default Tor configuration). If you are using Tor, leaves this as it is. If you are not using Tor, you will need to comment out this line.
As much as I like Tor, it is very slow and we now know that the NSA has broken Tor, so I am much less likely to depend upon it for anonymity.
Let's Test It
Now that we have put a proxy between us and any traffic we send, let's test it out. In this case, I am simply going to do an nmap scan to wonderhowto.com anonymously by sending the scan through a proxy. The command would be as follows:
- kali > proxychains nmap -sS 8.26.65.101
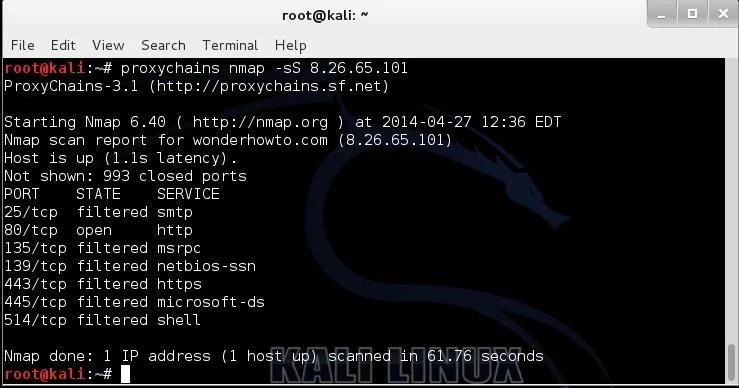
As you can see in the screenshot above, I have successfully scanned wonderhowto.com through my chosen proxy and returned the results back to me. In this way, it appears that my proxy scanned wonderhowto.com and not my IP address.
Some More Interesting Options
Now that we have proxychains working, let's look at some options that we can configure through the proxychains.conf. As we now have it set up, we are simply using a single proxy. We can put in numerous proxies and use all of them, we can use a limited number from the list, or we can have proxychains change the order randomly. Let's try all of those options.
Add More Proxies
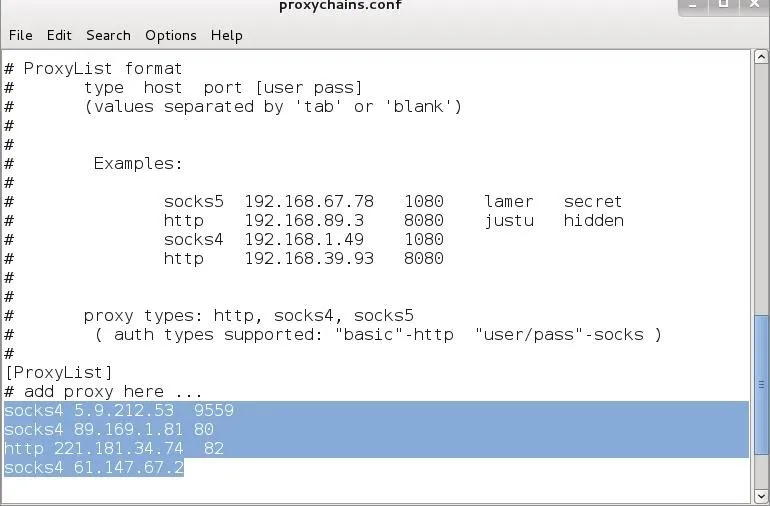
First, let's add some more proxies to our list. Open /etc/proxychains.config and add more proxy IPs like I've done below.
Proxychaining
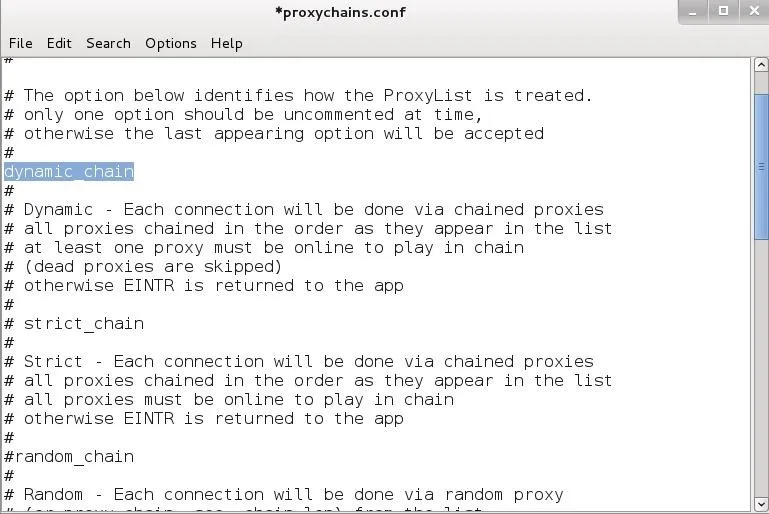
Now that we have multiple IPs in our proxychain.conf we can set up dynamic chaining. Dynamic chaining will enable us to run our traffic through every proxy on our list, and if one of the proxies is down or not responding, it will automatically go to the next proxy in the list without throwing an error.
To do so, let's first open the proxychains configuration file again.
With this file open, uncomment out the "dynamic_chains" line. This will enable dynamic chaining of our proxies allowing for greater anonymity and trouble-free hacking.
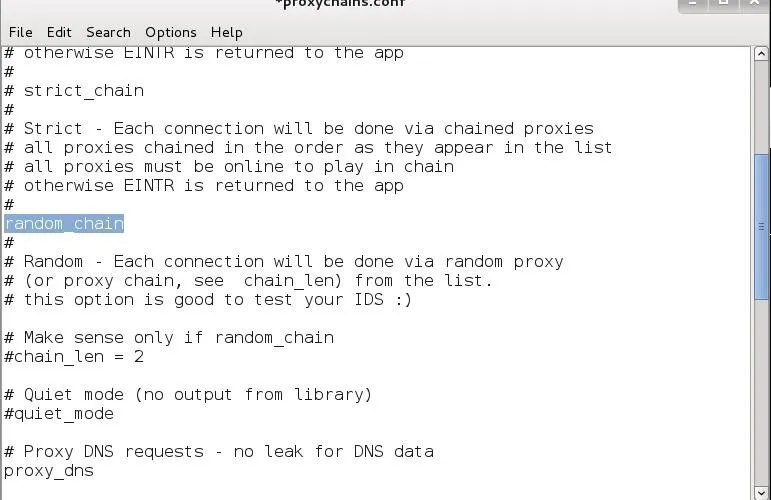
Random Chaining
Finally, we can also use "random chaining". With this option, proxychains will randomly choose IP addresses from our list and use them for creating our proxychain. This means that each time we use proxychains, the chain of proxy will look different to the target, making it harder to track our traffic from its source.
To do so, open the /etc/proxychains.conf file and comment out "dynamic chains" and uncomment "random chain". Since we can only use one of these options at a time, make certain that you comment out the other options in this section before using proxychains.
In addition; you may want to uncomment the line with "chain_len". This will determine how many of the IP addresses in your chain will be used in creating your random proxy chain.
Now that you know how to use proxychains, you can do your hacking with relative anonymity. I say relative, because there is no surefire way to remain anonymous with the NSA spying on all our activity. All we can do is make detection MUCH harder, and proxychains can help do this for us.
Image credits: Glove and keyboard and IP fingerprinting via Shutterstock

























Comments
Be the first, drop a comment!