Welcome back, my budding hackers!
In my continuing series on Linux basics for aspiring hackers, I now want to address Loadable kernel modules (LKMs), which are key to the Linux administrator because they provide us the capability to add functionality to the kernel without having to recompile the kernel. Things like video and other device drivers can now be added to the kernel without shutting down the system, recompiling, and rebooting.
Loadable kernel modules are critical to the hacker because if we can get the Linux admin to load a new module to their kernel, we not only own their system, but because we are at the kernel level of their operating system, we can control even what their system is reporting to them in terms of processes, ports, services, hard drive space, etc.
So, if we can offer the Linux user/admin a "new and improved" video driver with our rootkit embedded in it, we can take control of his system and kernel. This is the way some of the most insidious rootkits take advantage of the Linux OS.
So, I hope it's clear that understanding LKMs is key to being an effective Linux admin and being a VERY effective and stealthy hacker.
What Is a Kernel Module?
The kernel is a core component of any Linux operating system, including our BackTrack System. The kernel is the central nervous system of our operating system, controlling everything an operating system does, including managing the interactions between the hardware components and starting the necessary services. The kernel operates between user applications and the hardware such as the CPU, memory, the hard drive, etc.
As the kernel manages all that is taking place with the operating system, sometimes it needs updates. These updates might include new device drivers (such as video card or USB devices), file system drivers, and even system extensions. This is where LKMs come in. We can now simply load and unload kernel modules as we need them without recompiling the kernel.
Checking the Kernel
The first thing we want to do is check to see what kernel our system is running. There are at least two ways to do this. We can type:
- uname -a
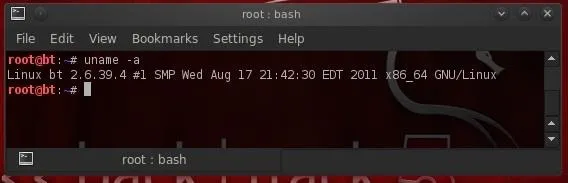
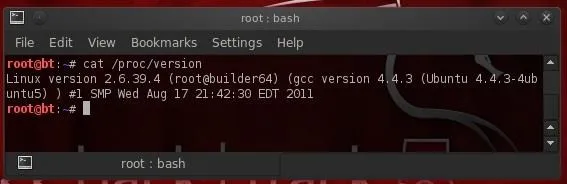
Note that the kernel tells us its kernel build (2.6.39.4), but also the architecture it is built for (x86_64). We can also get this info by "catting" the /proc/version file, which actually gives up even more info.
- cat /proc/version
Kernel Tuning with Sysctl
Sometimes, a Linux admin will want to "tune" the kernel. This might include changing memory allocations, enabling networking feature, and even hardening the kernel from hackers.
With modern Linux kernels, we have the sysctl command to tune kernel options. All changes you make with the sysctl remain in effect only until you reboot the system. To make any changes permanent, the configuration file for sysctl must be edited at /etc/sysctl.conf.
Be careful in using systctl because without the proper knowledge and experience, you can easily make your system unbootable and unusable. Let's take a look at the contents of sysctl now.
- sysctl -a |less
To view the configuration file for sysctl, we can get it at /etc/sysctl.conf.
- less /etc/sysctl.conf
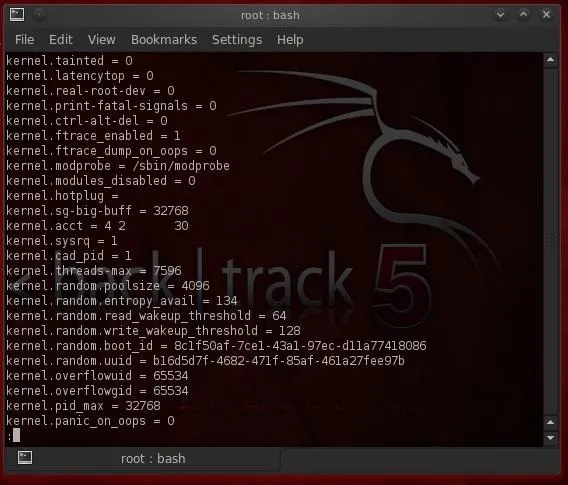
One of the ways we may want to use sysctl for hacking is to enable ipforwarding (net.ipv4.conf.default.forwarding) for man-in-the-middle attacks. From a hardening perspective, we can disable ICMP echo requests (net.ipv4.icmp_echo_ignore_all) so as to make more difficult, but not impossible, for hackers to find our system.
Kernel Modules
To manage our kernels, Linux has at least two ways to do it. The older way is to use a group of commands built around the insmod command. Here we use one of those—lsmod—to list the installed modules in kernel.
- lsmod
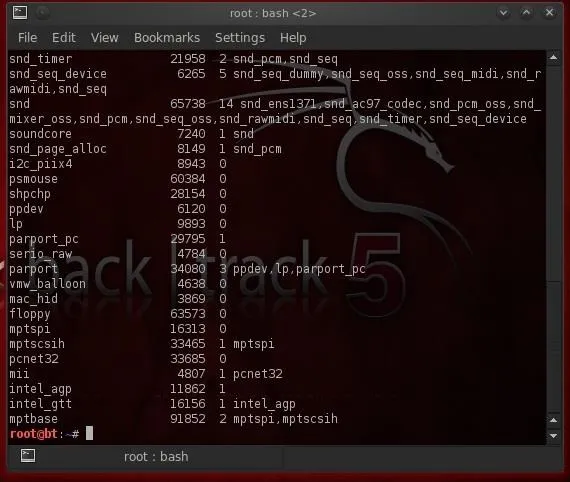
We can load or insert a module with insmod and remove a module with rmmod.
Modprobe
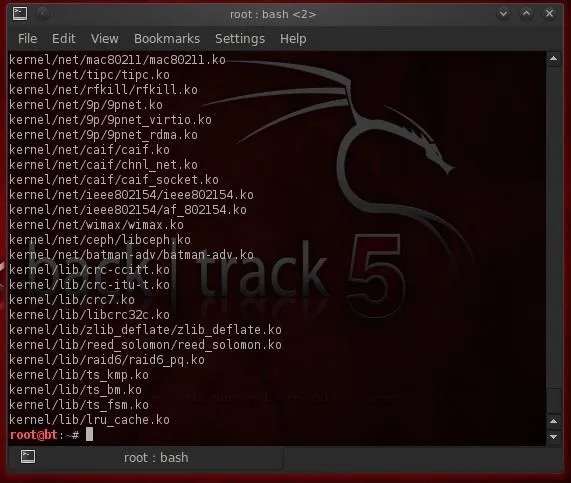
Most newer distributions of Linux, including our BackTrack 5v3, have converted to the modprobe command for LKM management. To see what modules are installed in our kernel, we can type:
- modprobe -l
To remove a module, we simply use the -r switch with modprobe.
- modprobe -r
A major advantage of modprobe is that understands dependencies, options, and installation and removal procedures for our kernel modules.
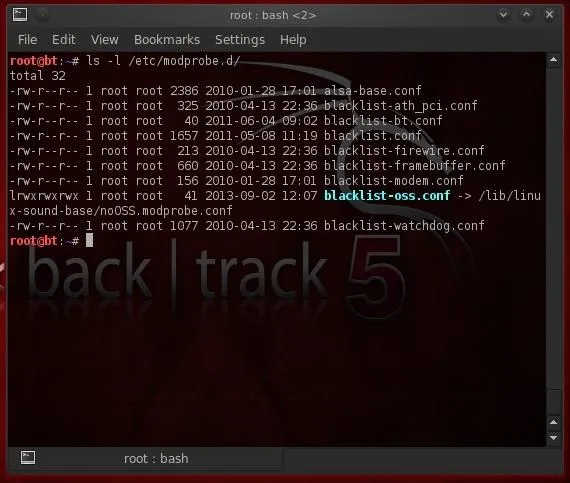
To see configuration files for the installed modules, we list the contents of the /etc/modprobe.d/ directory.
- ls -l /etc/modprobe.d/
Remember, the LKM modules are a convenience to a Linux user/admin, but are a major security weakness of Linux and one the professional hacker should be familiar with. As I said before, the LKM can be the perfect vehicle to get your rootkit into the kernel and wreak havoc!
Penguin image via Shutterstock

























Comments
Be the first, drop a comment!