Welcome back, my aspiring hackers!
Domain Name System (DNS) is one of those things we seldom think about unless it doesn't work. Then, it can be very frustrating when we attempt to navigate to a website and we get that frustrating error message.
DNS enables us to type in a domain name in our browser, such as wonderhowto.com, rather than a numerical IP address of the site we are trying to reach. In its simplest form, DNS simply translates domain names into IP addresses, making our lives much simpler. Can you imagine trying to remember all of the IP addresses of the hundreds of sites you visit daily?
For most of us working in Linux, we have two DNS concerns. First, as a client we need to access DNS services to translate our domain names into IP addresses. Second, as a server we need to provide DNS services. Here, I will limit myself to managing DNS from a client perspective and leave providing DNS services to another tutorial.
It's important to remind you here that in Linux, nearly everything is a file, and configuration is usually through the editing of a simple text file. This rule certainly applies to DNS.
/Etc/Hosts
In Linux, we have what is referred to as a "hosts" file. It's found where nearly all the configuration files are in the /etc directory, so /etc/hosts. This hosts file acts similarly to DNS, but it is static. This means that it's not updated like DNS is. The hosts file is the simplest and fastest method for mapping hostnames to IP addresses, but also the most time consuming.
Let's look at the /etc/hosts file in BackTrack. Type:
- bt > kwrite /etc/hosts
This will open the following file. Note that the default configuration in BackTrack has just the entries for localhost at 127.0.0.1 and then some notes on IPv6.
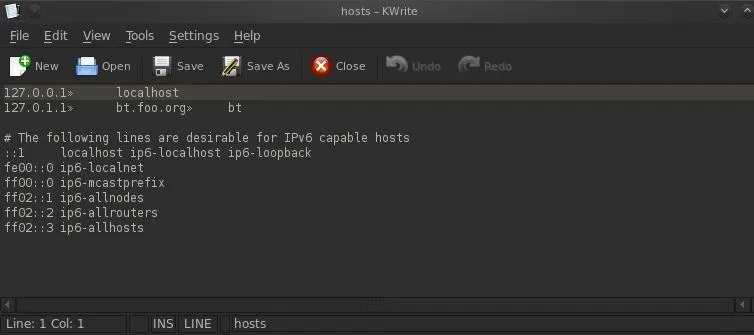
We could add additional lines to this file to provide simple name resolution services. If we wanted to resolve the word "hacker" to a system on our internal network, we could simply add a line to our hosts file, such as:
- 192.168.116.7 hacker
When we save our /etc/hosts and type "hacker" into our browser, we will be directed to the IP 192.168.117.7.
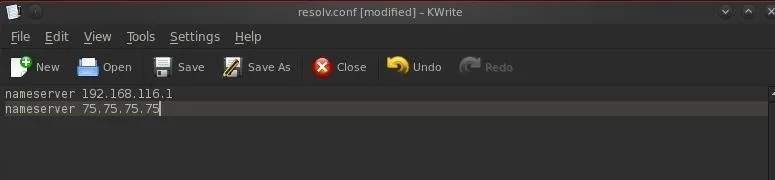
/Etc/resolv.conf
The primary file for pointing your system to a DNS server is the /etc/resolv.conf. Please note that the file name is similar to the English word resolve, but without the "e" at the end. It is here that we tell our system where to look for DNS services.
Let's open it with kwrite.
- bt> kwrite /etc/resolv.conf
When we hit ENTER, kwrite opens the file as below.
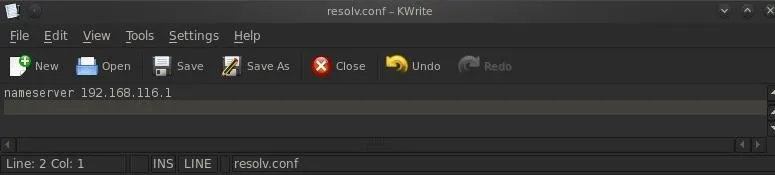
The format of this file is:
- nameserver IPaddress
As you can see, my /etc/resolv.conf is pointing to a DNS server on my local network, 192.168.116.1. I can change this to point to any public DNS server by simply editing and deleting the internal IP address with that of a public DNS server, such as Comcast's at 75.75.75.75.
If you have an internal DNS server, you would probably prefer to use it as it will give you faster responses, but people very often will put in both an internal DNS server first and then a public DNS server, second. In this way, your system will check the internal DNS server first and if it doesn't find a listing on that DNS server, it will then progress to the public IP server and will hopefully find it there.
I've edited my /etc/resolv.conf to include the public DNS server for Comcast at 75.75.75.75. All I do now is Save the /etc/resolv.conf file and my system will look to my internal DNS server first and then to the Comcast public DNS server, if it doesn't find the name in my private DNS server.
/Etc/nsswitch.conf
Lastly, we have the /etc/nsswitch.conf file. Here is where we tell our system the order of where to look for name resolution. We have opened it with kwrite and have displayed it below.
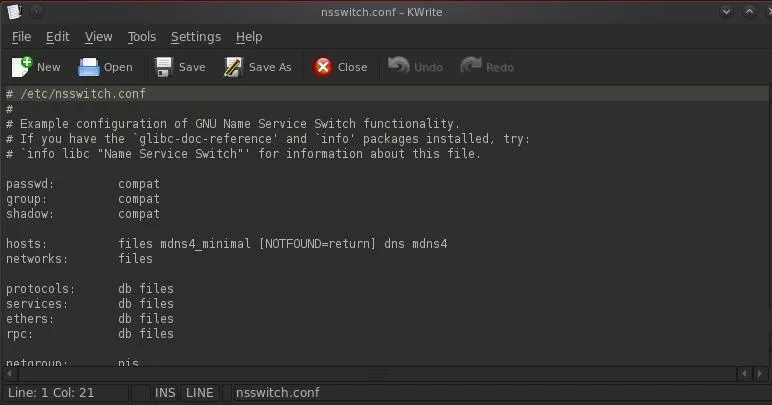
Note the line that begins with "hosts". This line line tells the system the order of which to search for name resolution. The system will try each in order until it finds the name it is looking for. Let's examine each separately.
- files - Refers to the /etc/hosts file. Generally, we want the system to look here first as it is the fastest.
- mdns4_minimal - This is a legacy multi-cast DNS protocol.
- dns - This tells the system to go to the /etc/resolv.conf for find a DNS server.
- [NOTFOUND=return] - This indicates that if the mdns_minimal search returns NOTFOUND, this should be treated as authoritative and the search ceases.
- mdns4 - This is multicast DNS, a relatively rare DNS-like protocol for small networks without DNS servers.
Stay tuned for more Linux Basics for the Aspiring Hacker.
Www image via Shutterstock

























Comments
Be the first, drop a comment!