Welcome back, my budding hackers!
I began this series on Linux basics because several of you have expressed befuddlement at working with BackTrack on Linux. As a hacker, there is no substitute for Linux skills.
Linux beginners are often faced with the issue of how to find files and programs, especially considering the radically different directory structure as compared to Mac OS or Windows. Beginners sometimes get frustrated trying to find the necessary files or binaries, so I'm dedicating this tutorial to finding stuff in Linux.

Before we dive in, make sure to check out my previous guides on Linux basics (1, 2, and 3) to get current on our lessons.
Finding Files in a Directory (Find)
The first command I want to show you is find. As you probably guessed, find is able to find stuff by looking in a directory for the file you're hunting for. By default, it's recursive, which means it will look in all sub-directories and display a list of everywhere it finds the file. For instance, if we are looking for aircrack-ng, we could type:
- bt > find -name aircarck-ng
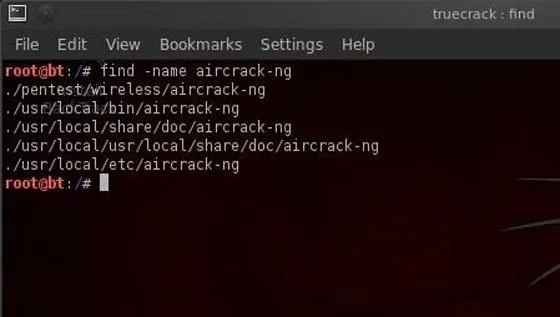
Note that we need to tell Linux that we want to search by name (-name) and then the name of the file we're searching for.
It then returns the full path of every place where it finds aircrack-ng. We can be more specific and ask Linux to only tell us where it finds aircrack-ng in the /pentest directory. We can do this by typing:
- bt > find /pentest -name aircrack-ng
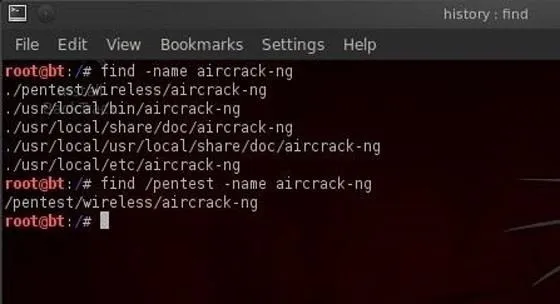
This command says, "look in the pentest directory and all its sub-directories and tell me where you find something called aircrack-ng".
Now, Linux only returns those paths to files that are in the directory /pentest or its sub-directories, such as /pentest/wireless/aircrack-ng and the others.
Finding Binaries in Path Variables (Which)
The next searching command we want to look at is which. This command allows us to search for binaries that are in our path variable. Hmm...even I think that's a lot of techo-googlygoop. Let's try to make some sense of it.
Binaries are the files that are the equivalent of executables in Windows. These are files that do something like echo, ls, cd, mv, etc. Our path variable is the variable that keeps the directory path to our binaries. Usually, our binaries are in the /bin (bin is short for binaries) or /sbin directory and that's reflected in our path variable. Our path variable setting can be checked by asking Linux to echo the value in the variable. We do this by typing:
- bt > echo $PATH
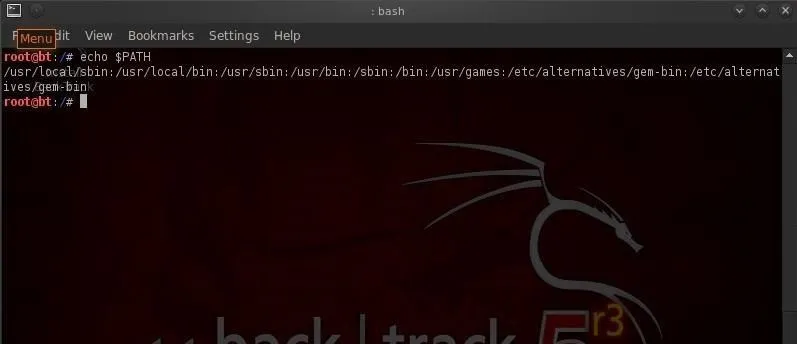
Linux responds with the value in our path variable. These are the places that which will search for binaries. So when we type:
- bt > which ls
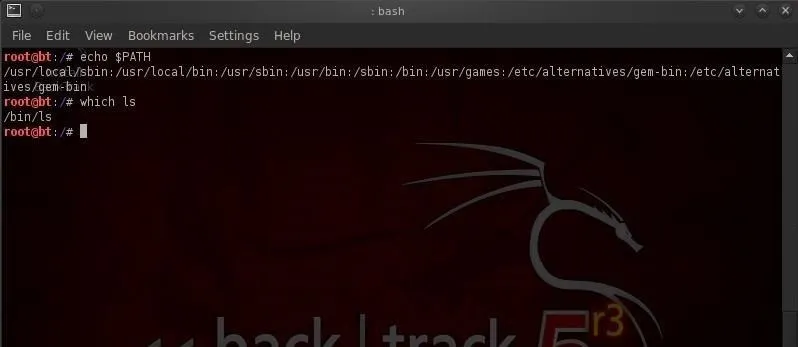
It returns the path to that binary. If we use which to search for aircrack-ng:
- bt > which aircrack-ng
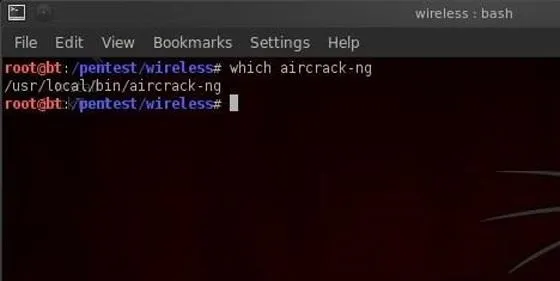
Then we can see that Linux returns /usr/local/bin/aircrack-ng. If aircrack-ng were not in a directory that was in our path, it would not be able to help us.
Finding Any File in Any Directory (Whereis)
Unlike which, whereis is not limited to finding binaries in our path. It can locate files in any directory, and in addition, it also locates the files manual or man pages. So, when we type:
- bt > whereis aircrack-ng
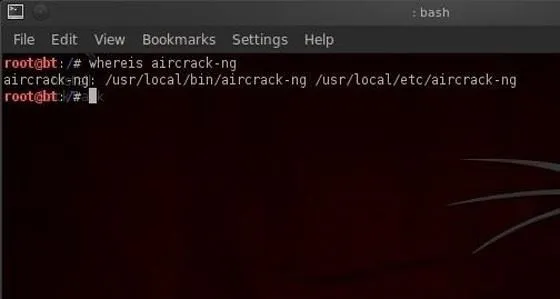
We can see that whereis returns the path to multiple locations of aircrack-ng including the man pages.
Finding Files Using the Database (Locate)
The locate command can also be used to find files and usually is much faster than either which or whereis. The difference is that locate uses a database of all the files in the file system and searches therefore take place much faster.
The drawback to locate is that new files will NOT be found by locate as the database is typically only updated daily, usually scheduled in the middle of the night when activity on the system is light as updating this database can be CPU intensive.
- locate aircrack-ng
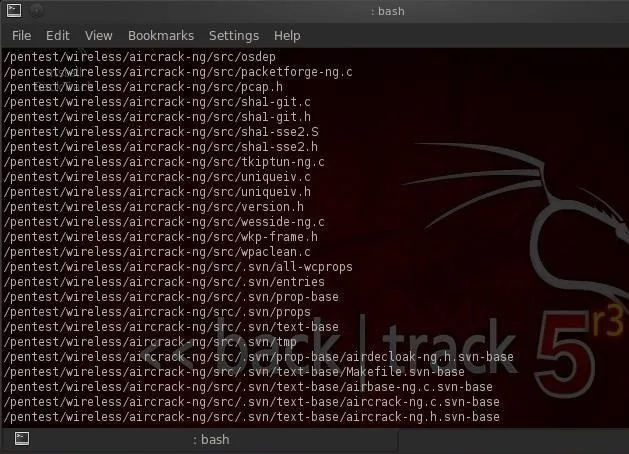
You can see in the screenshot above that locate returns a path every time it encounters any file with aircrack-ng in it, binary or not.
Hope this helps you in finding what you need in BackTrack Linux, therefore making you a better hacker. Make sure to check out the first three parts of this series (1, 2, and 3), and if you have any questions, ask away in the comments below or hit up the Null Byte forum for more help.
Come back for my next Linux basics tutorial, and we'll look at how to install new software!

























Comments
Be the first, drop a comment!