Most of you lot would be aware what WPA/WPA2 is so I won't bang on about the encryption or protocols a great deal. In short WPA and WPA2 both have a maximum of 256bit encrypted with a maximum of 64 characters in the password. The encryption is really only 64bit but x 4 because of the way the authentication functions as a 4 way handshake.
Before starting with oclHashcat. I would suggest to test for a WPS/Wifi Protected Setup' using Reaver and more recently the Pixie-dust method as it can effectively crunch the 11,000 WPS pins and extract the WPA pre shared key a lot faster than a complex WPA/WPA2 password. If WPS is secure I would suggest to then move onto WPA/WPA2 this method or the Evil twin method that clones the AP.
The tool Hashcat has been around for sometime and is CPU based, oclHashcat makes use of modern GPU processors and makes use of its physics abilities to crack most modern encrypted user/pass hashes.
oclHachcat will function in linux and also in windows.
.
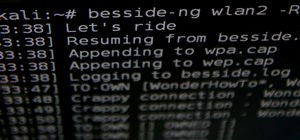
Step 1: Start Monitor Mode + Airodump-Ng
Method 1 - I use kali linux 2.1 myself so will be listing the linux commands. First up is to capture a WPA/WPA2 4 way handshake authentication in a .cap file. First up, Start monitor mode with airmon-ng. Then sniff the air waves with airodump-ng.
#:~$:airmon-ng start wlan0mon
Then
#:~$:airodump-ng wlan0mon
Then
#:~$:airodump-ng -c 1 -b 00:00:00:00:00 wlan0mon -w write2file
Once airodump-ng is busy, Pop up another terminal and send deauthentication packets towards the desired access point and connected device so it will disconnect and have to reconnect to the AP and capture the 4 way handshake with aireplay-ng, You can also just leave airodump-ng to capture the handshakes passively without spraying out deauthentication packets with aireplay-ng and over time it will capture handshake/s but generally takes a little longer and end up with a larger capture file. This aireplay-ng command can fail, You may need to do it a few times for it to function as it should. Just keep in mind with aireplay-ng the -a switch is for AP/wifi mac address, -b is for the wifi mac address of a device connected to that AP.
#:~$:aireplay-ng --deauth 100 -a routerMac -c connectedDeviceMac wlan0mon
Method 2 - I'll list a few methods here as the GUI tool are very simple. There is aircrack based GUI tools wifite and Fern, I prefer method 1. For windows users, You can setup a linux in a virtual machine within windows or there is a app for android called 'Wi-Fi PCAP Capture' that makes use of a Alfa RTL8187L wifi adapter. But would need to convert the .cap file into .hccap via the oclHashcat conversion page and it comes back in a download as a .hccap file.
Just pop up a terminal and simply enter:
#~:$wifite -wpa
or
#~:$fern-wifi-cracker
or
#~:$gerix-wifi-cracker-ng
Step 2: Convert the .Cap to .Hccap
Next, Is to convert the WPA capture file containing the WPA/WPA2 handshake to a file to .hccap format so oclhashcat/hashcat can work with it.
#:aircrack-ng input.cap -J output
If your using windows, You could effectively capture a WPA handshake with a Android phone app and a Alfa RTL8187L wifi adapter. The oclHashcat site has a page you can upload upto 5mb wpa.cap files and then download the back file back as a .hccap
Step 3: Crack the Capture File with oclHahscat
In these next steps we will make use of oclhashcat/hashcat to crack the WPA/WPA2 handshake.hccap.
A few things to note about oclHashcat-
- The hashcat tool set can be used in linux or windows.
- The -m switch is for hash type, We can easliy find the information needed for using the -m switch with WPA. This can easily be done with other hashes MD5 etc.
?#?:~:$oclhashcat? --help | grep WPA
Which will output:-
#:~:$2500 = WPA/WPA2
Which can be used with the -m switch.
E.g - If you replace grep WPA with grep MD5 and it will output 0 for that switch.
STEP 4 - Here we will make use of oclHashcat/Hashcat. It is a versitile tool set and can be used with or without a wordlist. It can create wordlists on the go without slowing down and storring massive dictionary files.
First up we will cover using oclHachcat with a wordlist.
There many wordlists that can be found on the web, But why store them in files when oclHashcat creates them on the fly. Another thing to keep in mind about wordlists, Not all wordlists you find online will be created for WPA/WPA2 as they need to start a 8 characters in length.
Step 4: oclHashcat with a Wordlist
#:oclhashcat -m 2500 /root/handshake.hccap /root/wordlist.txt
Note - A modern GPU such as R9290x at full speed can munch through 180,000 WPA attempts per second. This can vary depending a small amount depending on drivers at the time. This can be corrected with the -u switch to get full speed. The -u switch ends with amount of RAM on the gpu. For me my AMD R( is 4096mb. For eg. -u 4096.
#:oclhashcat -m 2500 -u 4096 /root/Hccap/filename.hccap /root/Numeric8-10char.txt
With wordlist the results will vary depending on the strength of your GPU and if the password is in your list at all. It flys through small lists, You can make a list.txt of compile wordlist/or hashes of the same type and pipe that into the command.
or
Step 5: oclHashcat Without a Wordlist
I prefer to not clog up hdd space with massive wordlist., Below is a table of the built in character sets for oclHashcat. There is various masking options to create .txt files to go through your preferred charsets. I wont get in to that now but the masking options work well.
?l = abcdefghijklmnopqrstuvwxyz
?u = ABCDEFGHIJKLMNOPQRSTUVWXYZ
?d = 0123456789
?s = !"#$%&'()+,-./:;??@\^`{|}~
?a = ?l?u?d?s (?a = All of the above characters)
- More charsets and switches
:
?l?l?l?l?l?l?l?l = a-z, 8 Characters in length.
?u?u?u?u?u?u?u?u = A-Z, 8 Characters in length.
?d?d?d?d?d?d?d?d = 0-9, 8 Characters in length.
?s?s?s?s?s?s?s?s = All, special characters, 8 characters in length.
?a?a?a?a?a?a?a?a = a-z, A-Z, 0-9, All special characters, 8 characters in length.
Lets just say you password is 12345678. You can use the custom mask option ?d?d?d?d?d?d?d?d
Note- For a mask/Brute-force options you will need to use the -a 3 switch.
The Hybrid options gel well also, It jumbles wordlist with masks or brute force methods.
Attack modes:
0 = Straight
1 = Combination
3 = Brute-force
6 = Hybrid dict + mask
7 = Hybrid mask + dict
For the example I will use a-z, 8 characters in length.
#:oclhashcat -m 2500 -u 4096 /root/hccap/filename.hccap -a 3 ?l?l?l?l?l?l?l?l
- Summary
This tool does it's slowest work when put up against WPA/WPA2 because of the 4 way handshake slowing it down. It does extremely well with other hash types For eg Md5 is cracked at 10million attempts per second and NTLM is a bit faster than Md5. The oclHashcat website has some more in depth .info.
hashcat cap2hccap - advanced password recovery
CAP-to-HCCAP online converter page for WPA/WPA2
Just updated your iPhone? You'll find new emoji, enhanced security, podcast transcripts, Apple Cash virtual numbers, and other useful features. There are even new additions hidden within Safari. Find out what's new and changed on your iPhone with the iOS 17.4 update.





















6 Comments
i have also heard that pyrit use gpu to crack the same
well explained,i like it
good job
Device #1: Not a native Intel OpenCL runtime. Expect massive speed loss.
You can use --force to override, but do not report related errors.
help
this is great i used recently crunch to create on the go wordlist and brute force .cap file but the max speed is 2300 KB/s (on i7 3rd gen with built in GPU which in case of crunch doesn't used )which is too slow then i got your post let me try i will upload speed difference with OCLHASHCAT soon after trying
I NEED Help !!!
Most routers here dont change the default password . They are ussually 8 character long and use numbers and Upper but only A-F . I tried using hashcat. Witj uppercase and digit but takes 2 long. Is there a way to use only A-F thank you.
i have the newest kali version and hashcat 5.1.0 but it is NOT OCLhashcat and i can't really get it working, can anyone help me get OCLhashcat or how to do this with normal hashcat?
thx
Share Your Thoughts