Everything Else


How To: Master Excel with This Certification Bundle
Microsoft Excel is one of the most useful tools you can bring into your professional life. However, as useful as Excel is, it can also be difficult to learn on your own. The All-In-One Microsoft Excel Certification Training Bundle is an incredible tool that will take you from Excel beginner to Master for $33.99, on sale for 98% off.

How To: This Python Bundle Can Teach You Everything You Need to Know
Python is one of the most commonly used programming languages in the world. From data science to game design, Python appears in almost every industry that requires coding of some kind. If you're looking to get into or get promoted to a higher level in one of those industries, then your next step is to learn this versatile programming language.
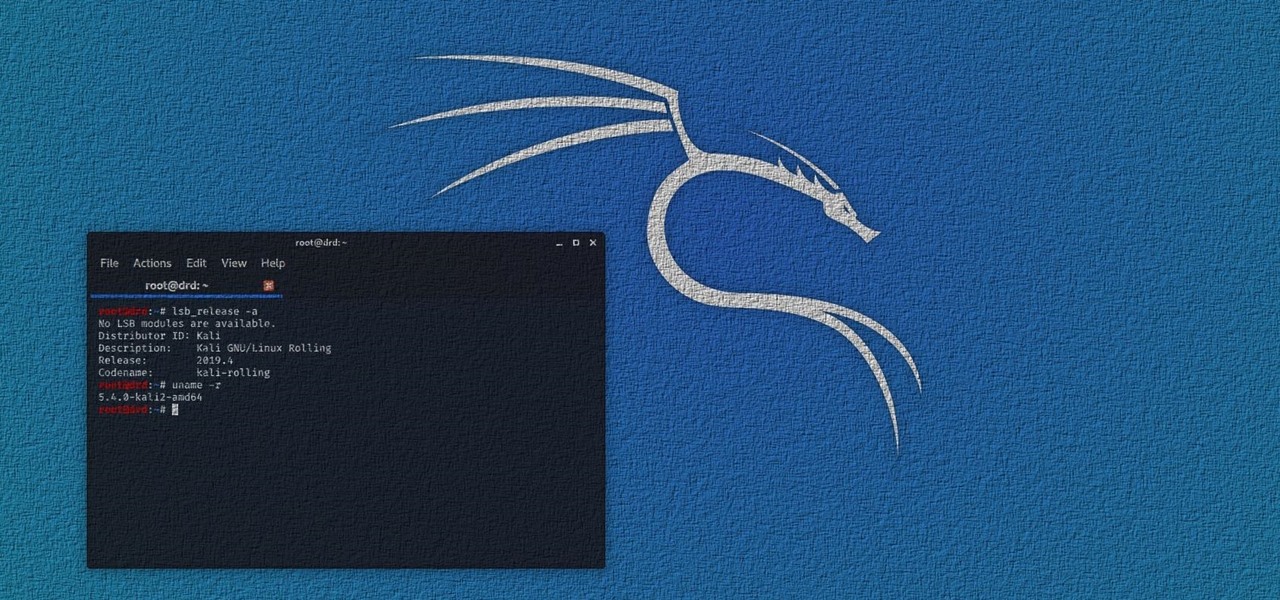
How To: Get Started with Kali Linux in 2020
Kali Linux has come a long way since its BackTrack days, and it's still widely considered the ultimate Linux distribution for penetration testing. The system has undergone quite the transformation since its old days and includes an updated look, improved performance, and some significant changes to how it's used.

How To: Hack MacOS with Digispark Ducky Script Payloads
The USB Rubber Ducky and the Digispark board both suffer from the same issue when attacking macOS computers: a keyboard profiler pop-up which tries to identify any non-Apple USB keyboards. While it's an annoying setback, the solution is a simple modification that allows Mac computers to be targeted, which affects the ability to target Windows and Linux devices.

How To: Secure Your Identity & Become Anonymous Online in 2019
Your social security number, credit card information, and medical history can fall into the wrong hands if you're not careful about how and where you share your data online. If you really care about your data, there are tools and techniques you can utilize to protect yourself from cyberstalkers, advertisers, and hackers in a time when digital lives are a high commodity.

How To: Take Control of Sonos IoT Devices with Python
Many popular IoT devices have terrible security. For instance, a hacker who's on the same Wi-Fi network as a Sonos speaker can assume direct control over the device's behavior. If an IoT device doesn't secure the messages used to control it over a network, it's easy for somebody to write a few Python scripts to make it do whatever they want.

Hacking macOS: How to Configure a Backdoor on Anyone's MacBook
The conversation of which operating system is most secure, macOS vs. Windows, is an ongoing debate. Most will say macOS is more secure, but I'd like to weigh in by showing how to backdoor a MacBook in less than two minutes and maintain a persistent shell using tools already built into macOS.

How To: Setup Dendroid (Android RAT)
This is my first How-To on Null-Byte, so I hope it's not too complicated written, because I am not a native english speaker. I don't use pictures, but this Tutorial is a good supplement for my updated Tutorial here.

How To: Map Wardriving Data with Jupyter Notebook
With the Wigle WiFi app running on an Android phone, a hacker can discover and map any nearby network, including those created by printers and other insecure devices. The default tools to analyze the resulting data can fall short of what a hacker needs, but by importing wardriving data into Jupyter Notebook, we can map all Wi-Fi devices we encounter and slice through the data with ease.

Hacking macOS: How to Hide Payloads Inside Photo Metadata
Complex shell scripts can be implanted into photo metadata and later used to exploit a MacBook. In addition to obfuscating the true nature of an attack, this technique can be used to evade network firewalls as well as vigilant sysadmins.

Hacking Windows 10: How to Create an Undetectable Payload, Part 2 (Concealing the Payload)
Once a hacker has created a PowerShell payload to evade antivirus software and set up msfconsole on their attack system, they can then move onto disguising their executable to make it appear as a regular text file. This is how they will get a Windows 10 users to actually open the payload without knowing they are doing so.

Hacking Windows 10: How to Break into Somebody's Computer Without a Password (Setting Up the Payload)
A powered-off Windows 10 laptop can be compromised in less than three minutes. With just a few keystrokes, it's possible for a hacker to remove all antivirus software, create a backdoor, and capture webcam images and passwords, among other highly sensitive personal data.

How To: The White Hat's Guide to Choosing a Virtual Private Server
Conducting phishing campaigns and hosting Metasploit sessions from a trusted VPS is important to any professional security researcher, pentester, or white hat hacker. However, the options are quite limited since most providers have zero-tolerance policies for any kind of hacking, good or bad. After researching dozens of products, we came out with 5 potentials that are ideal for Null Byte readers.

Exploit Development: How to Read & Write to a Program's Memory Using a Format String Vulnerability
Format strings are a handy way for programmers to whip up a string from several variables. They are designed to save the programmer time and allow their code to look much cleaner. Unbeknownst to some programmers, format strings can also be used by an attacker to compromise their entire program. In this guide, we are going to look at just how we can use a format string to exploit a running program.

How To: Create an Evil Access Point with MitmAP
The threat of an evil access point has been around for a long time, and with the rise of open public Wi-Fi, that threat is often overshadowed by how comfortable we are using third-party Wi-Fi hotspots at coffee shops and public spaces. While we've shown an evil twin attack using the Aircrack-ng suite of tools, MitmAP is a Python tool to configure custom APs for many types of wireless attacks.

How To: Steal macOS Files with the USB Rubber Ducky
If you need a tiny, flexible attack platform for raining down human-interface-device (HID) attacks on unattended computers, the USB Rubber Ducky is the most popular tool for the job. By loading the Ducky with custom firmware, you can design new attacks to be effective against even air-gapped computers without internet access. Today, you'll learn to write a payload to make "involuntary backups" through copying a targeted folder to the Ducky's USB mass storage.

How To: Setup Practice Ctf's from Vulnhub on Kali Linux
Since Ive started to learn about nmap and metasploit and other tools I was learning well but I had one problem,

How To: MagSpoof Digitally Clones the Magnetic Stripe of Any Credit Card
Samy Kamkar, the security researcher known for the MySpace Worm and his combination lock cracking skills (using an online calculator), is back—and this time, he's after your credit cards!

Don't Be a Script-Kiddie part1: Introduction to Shell Script
Hello my anxious hackers, the week has started and here we begin a new series that I think will help many here and not only, for those that have the opportunity to follow our tutorials but they are not yet part of the community.
How To: SQL Injection Finding Vulnerable Websites..
Welcome Back !! TheGeeks. SQL Injection (SQLI) Part-1
How To: Hack Windows 7 (Become Admin)
Step 1: Introduction: Hello! Hackers

How To: Crack Any Game by Pop Cap
Hello fellow peoples of the earth and welcome to another tutorial by me! Noah! you know popcap make bejewled blitz and zuma and pvz for facebook but what if you want the big games like pvz or bejewled 3 from them but don't want to pay. Then worry not as this simple tutorial will help you get those games you enjoy for free without any trials or limitations! to the startthetutorialmobile

How To: Enable Code Syntax Highlighting for Python in the Nano Text Editor
With the plethora of programming that we promote at Null Byte, I figured a lot of you newbies that stop by IRC will need a big boost in the right direction to make your dive into programming a lot easier. A hot question that has been thrown around in IRC a lot when making the initial dive is, "How do I write code?". People who do not know much about computers can't understand how code is written. Code that we write here is usually scripted and written in Python, so we will use it as our examp...

How To: Code a Dead Man's Switch in Python 3 to Encrypt & Delete Files Whenever You Don't Check In
A dead man's switch is a fairly simple concept. If you don't perform a specific task before a set amount of time, it'll perform a specific action you set. They can be handy not just for hackers but for everyone who wants to protect themselves, someone else, or something tangible or intangible from harm. While there are more nefarious uses for a dead man's switch, white hats can put one to good use.

Hacking Windows 10: How to Evade Detection of Netstat & Tasklist
There are countless tutorials online that show how to use Netstat and Tasklist to find an intruder on your computer. But with a few PowerShell functions, it's possible for a hacker to evade detection from the almighty command line.

How To: Bypass PowerShell Execution Policy to Pwn Windows
PowerShell is an essential component of any Windows environment and can be a powerful tool in the hands of a hacker. During post-exploitation, PowerShell scripts can make privilege escalation and pivoting a breeze, but its execution policy can put a damper on even the best-laid plans. There are a variety of methods, however, that can be used to bypass PowerShell execution policy.

How To: Haunt a Computer with SSH
If you've ever needed to prove you have remote access to a device, or simply want a way to convince someone their computer is haunted, SSH can be used to make a device begin to show signs of being possessed.

Mac for Hackers: How to Set Up a MacOS System for Wi-Fi Packet Capturing
MacOS isn't known as an ideal operating system for hacking without customization, but it includes native tools that allow easy control of the Wi-Fi radio for packet sniffing. Changing channels, scanning for access points, and even capturing packets all can be done from the command line. We'll use aliasing to set some simple commands for easy native packet capture on a macOS system.

How To: Install & Use the Ultra-Secure Operating System OpenBSD in VirtualBox
OpenBSD implements security in its development in a way that no other operating system on the planet does. Learning to use the Unix-like operating system can help a hacker understand secure development, create better servers, and improve their understanding of the BSD operating system. Using VirtualBox, the OS can be installed within a host to create a full-featured test environment.

How To: Gain Control of WordPress by Exploiting XML-RPC
WordPress did not become what is arguably the most popular blogging and CMS platform on the planet because it was difficult to use. Rather, its user-friendly and rich feature set led to it finding a home on somewhere north of 70 million websites—and that's just counting blogs hosted on WordPress.com.
How To: Brute-Force WPA/WPA2 via GPU
Most of you lot would be aware what WPA/WPA2 is so I won't bang on about the encryption or protocols a great deal. In short WPA and WPA2 both have a maximum of 256bit encrypted with a maximum of 64 characters in the password. The encryption is really only 64bit but x 4 because of the way the authentication functions as a 4 way handshake.

Hack Like a Pro: How to Use PowerSploit, Part 1 (Evading Antivirus Software)
Welcome back, my greenhorn hackers! A few years back, Microsoft implicitly recognized the superiority of the Linux terminal over the GUI-based operating system by developing PowerShell. Since Windows 7, every Windows operating system has had PowerShell installed by default, and they even made PowerShell capable of running Linux commands on Windows!

PHP for Hackers: Part 1, Introduction and Setting Up
In this series you will learn how to use PHP to perform attacks, gather information, and setup backdoors. Along with performing attacks you will learn how to protect yourself from them. In this part you will learn about PHP as well as install Apache and PHP. What you'll need for this series

Guide: Wi-Fi Cards and Chipsets
Greetings aspiring hackers. I have observed an increasing number of questions, both here on Null-Byte and on other forums, regarding the decision of which USB wireless network adapter to pick from when performing Wi-Fi hacks. So in today's guide I will be tackling this dilemma. First I will explain the ideal requirements, then I will cover chipsets, and lastly I will talk about examples of wireless cards and my personal recommendations. Without further ado, let's cut to the chase.

How To: Add Proxies to Your ProxyChains Config File the Lazy Way ;)
Hello fellow gray hat hackers, I wrote a program in python that helps me to fill up my proxychains.conf file, so I don't have to manually enter in the proxies. I figured I will give a little how-to of how I did it and maybe I could help some of you(hackers) out there to stay anonymous.

Guide: Privacy Matters
Greetings all. Today I intend to append a new series to my mini-collection of posts. This series will consist of informative guides for the purpose of depicting certain aspects of the White Hat profession that I believe are of profound importance. Furthermore, I will keep this series simple for everyone to follow, regardless of your tech level. So without further ado, let's get right into it.

How To: Successfully Hack a Website in 2016!
Hello partners, first of all I would like to thank all those who have sent me positive feedback about my posts, to say that I'm always willing to learn and teach. I'm also open to answer the appropriate questions.

How To: Bypass Two-Way Authentication on Facebook with Android Script
Hi guys, this is going to be kinda like a follow up to my previous post on hacking facebook with the remote keylogger. If you haven't seen that post I suggest you do. So like you can click here. Anyway let's move on.

How To: Increase TX-Power in Kali 2.0
Hello, *Note This is my first how to post on here, so please correct anything that I have missed and let me know if anything I explained is unclear and I will try to clearify. Also I am a NOOB when it comes to this art, so I might have missed something, if so please inform me so I can better myself*

How To: Anti-Virus in Kali Linux
Hello fellows nullbyters, first of i will start saying that im addicted to this community, i feel the challenge growing up so fast, all the newbies, amateurs,advanced and professionals hackers around trying their best to help the community, badly but we got some script-kids too but anyway, today we are going to learn how to install and use clanAV in kali linux.. INTRODUCTION







