Null Byte How-Tos
How To: Security-Oriented C Tutorial 0x0A - Man Pages
Okay guys and gals, this will be a quick tutorial on using the incredibly helpful man pages. What Are Man Pages?

How To: Security-Oriented C Tutorial 0x09 - More on Strings
What's up guys! It's time to discuss strings in more detail. Review
How To: Remotely Reset Router P.DG AV4001N
I assume you are on the same network with your router 1 - open a terminal window

TypoGuy Explaining Anonymity: Secure Browsing Habits
to stay secure, you dont just need Tor, and a VPN. You need good browsing habits. What are Browsing Habits You Ask?

How To: Security-Oriented C Tutorial 0x08 - A Trip Down Memory Lane
Before I continue with a topic on strings, we first require some fundamental understanding of how memory works, i.e. what it is, how data looks in memory, etc. as this is crucial when we are analyzing vulnerabilities and exploitation. I highly suggest that your mind is clear and focused when reading the following article because it may prove to be confusing. Also, if you do not understand something, please verify all of your doubts, otherwise you may not completely understand when we touch on...

How To: Web Development 01 - Setting Everything Up
Hello fellow Null-Byters! This is my first post so please be respectful and constructed criticism is much appreciated. I am no professional, however I believe that it is important to understand technologies before you go poking at them and trying to break them, I therefore decided to make this series. In this "tutorial" we are going to setup a web server with php and mysql. I will be doing this with a raspberry pi because a pi is quite versatile.

How To: Security-Oriented C Tutorial 0x07 - Arrays and Strings
Welcome to another C tutorial. We will be looking at arrays, discussing what they are, when they are used and their special relationship with the char variable. Let's begin.

How To: Security-Oriented C Tutorial 0x06 - Operators
Hello again! In this tutorial, we are going to go over something called "operators" which will help us build upon conditions of control structures and also some variable manipulation. Without further ado, let's dive in!
How To: Protect Yourself from Someone Trying to Hack into Your Mac
If you read my previous post, "How to Hack into a Mac Without the Password", you know that it is very easy to break into someone's Mac if you have physical access to the computer. Now the question that lies is, how do we protect ourselves from this happening to us? Well, here is a way that guarantees that no one will be able to change your password through OS X Recovery.

How To: Bypass Two-Way Authentication on Facebook with Android Script
Hi guys, this is going to be kinda like a follow up to my previous post on hacking facebook with the remote keylogger. If you haven't seen that post I suggest you do. So like you can click here. Anyway let's move on.

How To: SQL Injection! -- Detailed Introduction.
Hello NullByte! This will be my first How To series.

How To: Security-Oriented C Tutorial 0x05 - Control Structures Part II: Loops
Welcome back to control structures, part two featuring the three types of loops. Here we go! What Is a Loop?

How To: Security-Oriented C Tutorial 0x04 - Control Structures Part I: If Statements
Welcome back to another C tutorial, this post covering the first part of control structures, if statements. Let's get right into it.

How to Train Your Python: Part 13, Advanced Lists, Slicing, and Comprehension
Welcome back! In the last training session, we covered logical and membership operators. We're going to switch gears and expand our knowledge of lists.

How To: Embed a Metasploit Payload in an Original .Apk File | Part 2 – Do It Manually
UPDATE: This post is outdated, the latest version with the correct links and updated instructions can be found at my blog, here - https://techkernel.org/2015/12/19/embed-metasploit-payload-in-apk-manually/

SPLOIT: Building Android Applications for Hackers: Part 2: Setting Up the Environment
Greetings my fellow aspiring hackers,

How To: Security-Oriented C Tutorial 0x03 - Bits, Bytes, Broken?
Hey there, reader! In this tutorial we are going to explain how values are stored in variables as either signed or unsigned. Try to not get lost!

How To: Security-Oriented C Tutorial 0x02 - Variables && Data Types
Hello again, reader! In this post, we are going to cover some data types and how to declare variables. It shouldn't be too hard so just sit back, relax, grab some popcorn and enjoy the ride (while you still can!).

Botnets and RATs : Precautionary Measures and Detection (Part 2)
Hola my fellow hackers! I promised you the tutorials on setting up RAT's and Botnets, but before jumping into those, i want you to know about the precautionary measures and detection of RATs which might be on the system without your prior knowledge. Of course the Anti-virus do most of the job but there are some RATs which slips past the Anti-viruses (This is where Hacker's skill come into play).
How To: What is An Arduino? (Part 1)
I'm back. School's an ass. On my quest for knowledge, which started approximately 3 years ago, I can upon an interesting little artifact. It is called the Arduino.
How To: Increase TxPower Kali Sana Linux 2.0
This is for those using Kali Linux 2.0 that need to edit the CRDA values to get the increase in Txpower

How To: Security-Oriented C Tutorial 0x01 - Hello, World!
Welcome back, reader! In this tutorial, we will be covering our first program! So let's get to it. We all know the unspoken tradition of the first program when learning a language and of course, here we will respect and complete it. Fire up your favorite text editor (be it vim, emacs, gedit, it's all the same to me, no h8) and try to keep up.
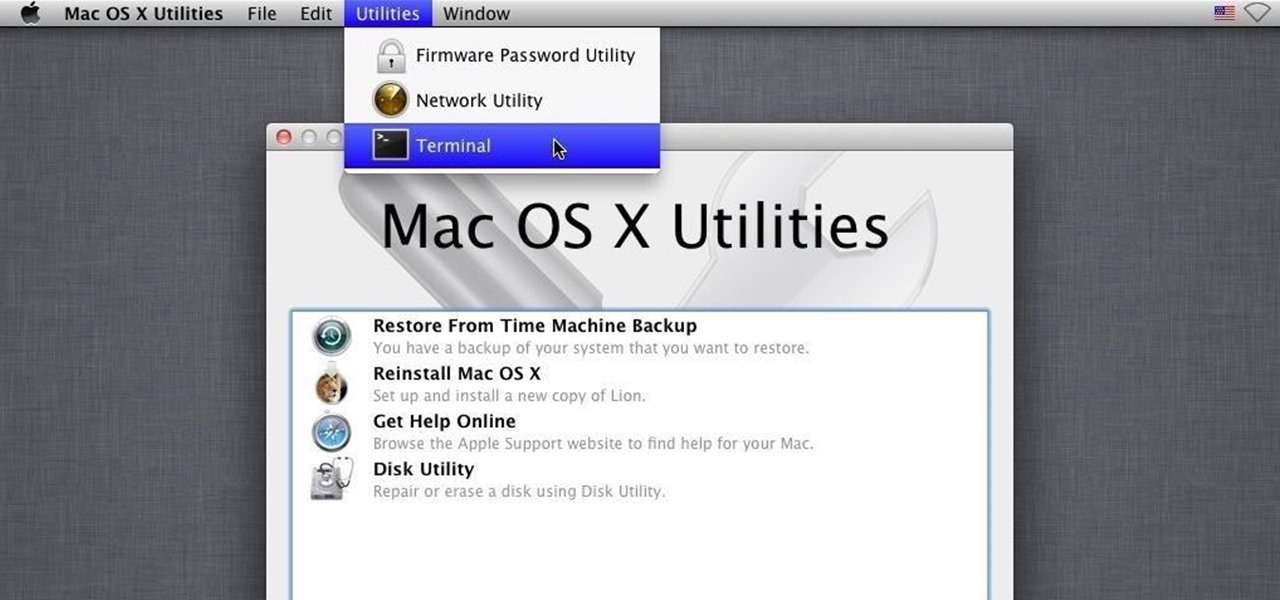
How To: Hack into a Mac Without the Password
Hello, my fellow hackers. My name is cl0ck. I am a senior majoring in Computer Engineering with an emphasis is Security. I have been lurking the site for a while now reading and learning from the great minds that reside here. I, too, have some knowledge that I would like to share with all of you. This post actually comes from a personal problem I faced and had to find a solution for. Without further ado, here it is:

How To: Security-Oriented C Tutorial 0x00 - Introduction
Hello there, reader! If you've clicked on this How-to then it means you are interested in learning some C programming or just generally curious about what this page has to offer. And so I welcome you warmly to the first of many C tutorials!

SPLOIT: Building Android Applications for Hackers : Part 1 : Introduction to Android.
Greetings my fellow aspiring hackers,

Hack Like a Pro: Digital Forensics for the Aspiring Hacker, Part 11 (Using Splunk)
Welcome back, my neophyte hackers! Digital forensics is one of the fields often overlooked by aspiring hackers. In a rush to exploit every and any system they can, they often ignore learning digital forensics—the field that may lead to them being traced.

How to Train Your Python: Part 12, Logical and Membership Operators
Welcome back! In the last round of python training, we talked about tuples and dictionaries. We'll be diverging again and talking about logical operators as well as membership operators. These are used very similiar to booleans, so if you haven't read that, I suggest you do so first.
How To: Fake Captive Portal with an Android Phone
Have you ever used an open wifi, which after you connect displays a website to enter your credentials to get internet? That website is called captive portal and widely used in airports, hotels, universities etc. Have you ever wondered what would happen if someone would set up an open wifi with the same name displaying a very similar web page asking for credentials? Usually if there are multiple wifi networks with the same name and encryption, devices only display the one with the highest sign...
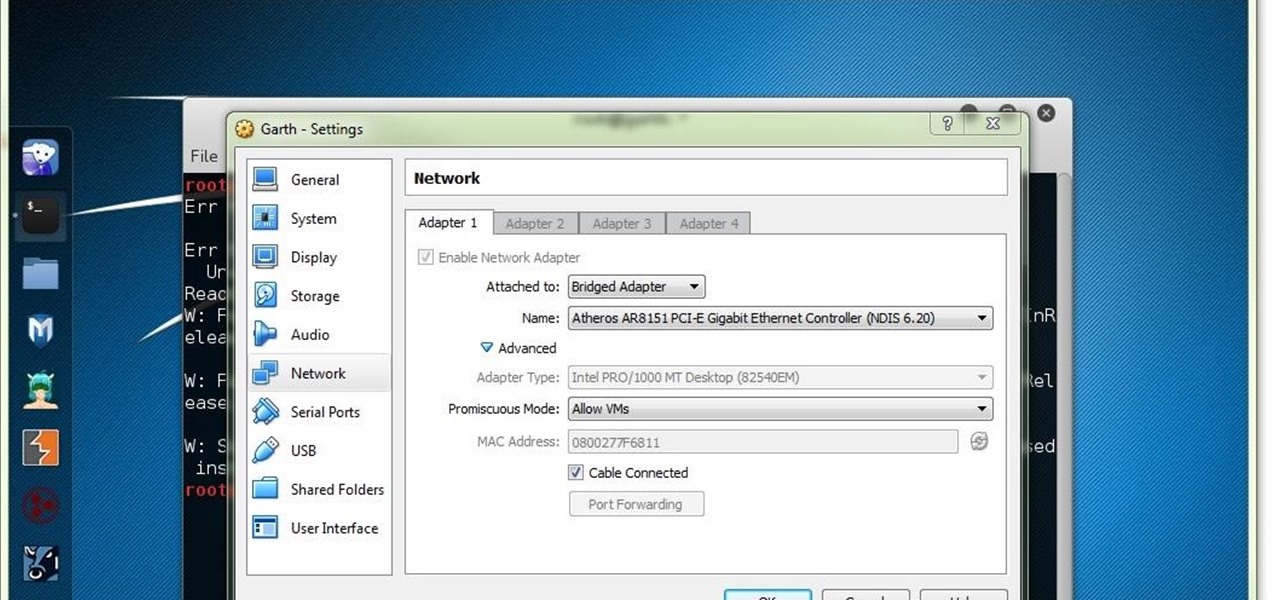
How To: Struggling to Connect to WiFi Network on Kali Linux 2.0 VirtualBox
Hello y'all! I apologize if this question has been solved somewhere else, but I have looked around on Google, Yahoo, and Null Byte and have not been able to find any working solutions.
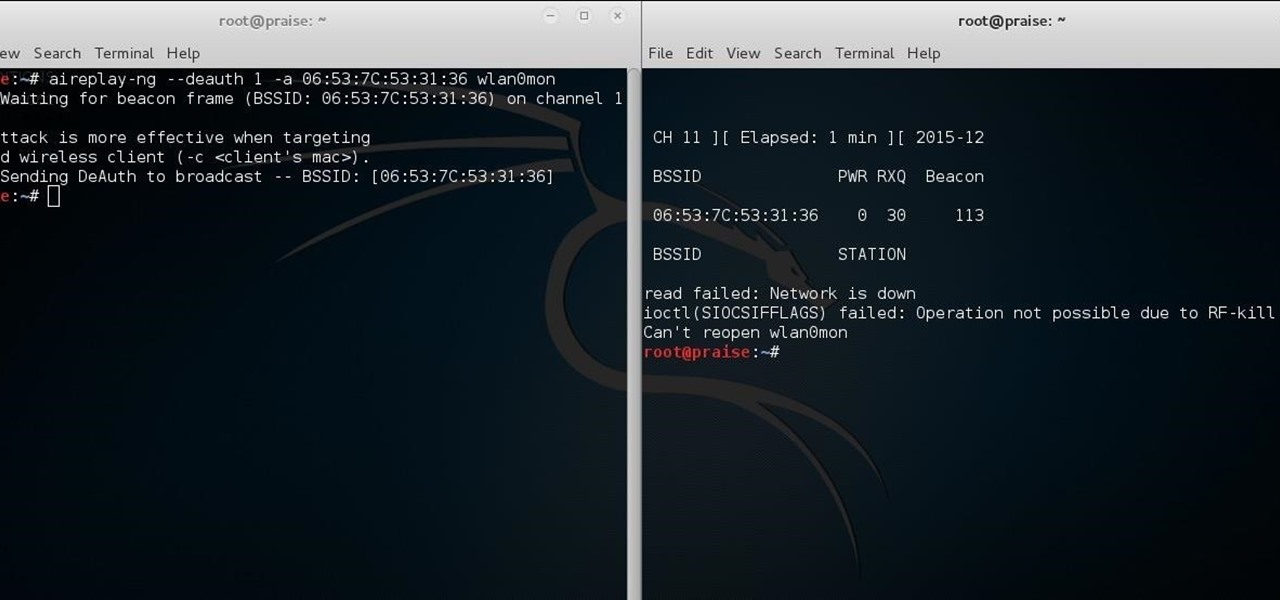
How To: Fix "Network Is Down" on Airodump-Ng
Hello there learners and readers! I figured I'd show you guys my problem and how I solved it, hoping that it would help people who are facing the same issue. Today, we'll be talking about the solution of
How To: Web Development for Hackers 1.1: HTML,CSS,JS
hello hackers,newbies and followers of this great community, after some research here in our community, I noticed that there is not even one tutorial that teach Web Development. We have a lot of tutorials on how to hack web site but many do not know exactly how a web site is composed, then I decided, meeting the community's needs, begin to teach people how to develop web sites.
How To: Install ParrotSec Sealth and Anonsurf Modules on Kali 2.0
First of all, before we start, the modules and some of the tutorials belongs to Und3rf10w, not mine!

How To: Embed a Metasploit Payload in an Original .Apk File
UPDATE: This post is outdated, the latest version with the correct links and updated instructions can be found UPDATE: This post is outdated, the latest version with the correct links and updated instructions can be found at my blog, here - at my blog, here - https://techkernel.org/2015/12/11/embed-metasploit-payload-in-apk-easily/

Cryptocurrency for the Hacker : Part 3 (Why It May Be a Bad Idea for You)
Of course, if it were a perfect form of currency, it would have become the standard by now. But it hasn't. Wanna know why? The story begins with the advent of agriculture, when humans had settled down under groups as units called villages, over 10,000 years ago.

Hack Like a Pro: Networking Basics for the Aspiring Hacker, Part 1
Welcome back, my greenhorn hackers! As expected with Null Byte's dramatic growth over the last year, we have added many new aspiring hackers who are still lacking in the basics of networking. In addition, with the new "White Hat" certifications coming out shortly, the exam will require some basic networking skills and knowledge to pass.

How To: Displaying Text from a File C++
This is a little c++ program that I thought would be handy in the future. Although, I apologize in advance for any errors in the code since I haven't had the chance to compile it yet. Anyway, please if you are a script kiddie please do me a favor and at least read this article fully. :)
How To: Antisocial Engine
A.E Hi again this is my second post on nullbyte. The first one was on how to make a remote screenshot captor, now I will give you a presentation for a project of mine(I have named It Antisocial Engine) that It is not something extraordinary but will help many guys.
How To: Hack Any Windows 7/8/10 User Password Without Logging In
Hello! This is my first post on this awesome website! I know that Windows exploits are less common than the more advanced hacks, but I found something I deem pretty cool and figured why not share it with you all. Alright, enough about me, lets begin.

How To: Properly Submit Tools for the Null Byte Suite
Hello everyone. I've recently made the annoucement of the Null Byte suite of tools, and we've covered how to download and install it. Now it's time we cover how to submit a tool for inclusion into the suite. It's relatively simple, but we need to get a few ground rules out of the way.

How To: Learn How Elliot from Mr. Robot Hacked into His Therapist's New Boyfriend's Email & Bank Accounts (Using Metasploit)
Social engineering is a pretty important item in a hacker's toolkit. In Mr robot there was a time, we saw Elliot using social engineering to gain access to his therapist's boyfriend's email and bank accounts by calling him and pretending to be someone from his bank, then Elliot asked him for some info that were really useful to gain access to his account, the target believed to be someone from the bank and gave him the info Elliot was looking for. But How Is It in the Real World?







