I did see a site with an old IIS 6.5, as a government site. Is the site 100% hackable for this reason ? Or is he probably really secure, but old... ?
Thanks

I did see a site with an old IIS 6.5, as a government site. Is the site 100% hackable for this reason ? Or is he probably really secure, but old... ?
Thanks
 Forum Thread:
When My Kali Linux Finishes Installing (It Is Ready to Boot), and When I Try to Boot It All I Get Is a Black Screen.
8
Replies
Forum Thread:
When My Kali Linux Finishes Installing (It Is Ready to Boot), and When I Try to Boot It All I Get Is a Black Screen.
8
Replies Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
2
Replies
Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
2
Replies Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies Metasploit Error:
Handler Failed to Bind
41
Replies
Metasploit Error:
Handler Failed to Bind
41
Replies Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies How to:
Crack Instagram Passwords Using Instainsane
36
Replies
How to:
Crack Instagram Passwords Using Instainsane
36
Replies Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies How to:
Sign the APK File with Embedded Payload (The Ultimate Guide)
10
Replies
How to:
Sign the APK File with Embedded Payload (The Ultimate Guide)
10
Replies Forum Thread:
How to Run and Install Kali Linux on a Chromebook
18
Replies
Forum Thread:
How to Run and Install Kali Linux on a Chromebook
18
Replies Forum Thread:
How to Find Admin Panel Page of a Website?
13
Replies
Forum Thread:
How to Find Admin Panel Page of a Website?
13
Replies Forum Thread:
can i run kali lenux in windows 10 without reboting my computer
4
Replies
Forum Thread:
can i run kali lenux in windows 10 without reboting my computer
4
Replies Forum Thread:
How to Hack School Website
11
Replies
Forum Thread:
How to Hack School Website
11
Replies Forum Thread:
Make a Phishing Page for Harvesting Credentials Yourself
8
Replies
Forum Thread:
Make a Phishing Page for Harvesting Credentials Yourself
8
Replies Forum Thread:
Creating an Completely Undetectable Executable in Under 15 Minutes!
38
Replies
Forum Thread:
Creating an Completely Undetectable Executable in Under 15 Minutes!
38
Replies How To:
Dox Anyone
How To:
Dox Anyone
 How To:
Scan for Vulnerabilities on Any Website Using Nikto
How To:
Scan for Vulnerabilities on Any Website Using Nikto
 How To:
Brute-Force FTP Credentials & Get Server Access
How To:
Brute-Force FTP Credentials & Get Server Access
 How To:
Crack Shadow Hashes After Getting Root on a Linux System
How To:
Crack Shadow Hashes After Getting Root on a Linux System
 How To:
Find Identifying Information from a Phone Number Using OSINT Tools
How To:
Find Identifying Information from a Phone Number Using OSINT Tools
 How To:
Enumerate SMB with Enum4linux & Smbclient
How To:
Enumerate SMB with Enum4linux & Smbclient
 Hack Like a Pro:
How to Conduct a Simple Man-in-the-Middle Attack
Hack Like a Pro:
How to Conduct a Simple Man-in-the-Middle Attack
 How To:
Find Vulnerable Webcams Across the Globe Using Shodan
How To:
Find Vulnerable Webcams Across the Globe Using Shodan
 How To:
Check if Your Wireless Network Adapter Supports Monitor Mode & Packet Injection
How To:
Check if Your Wireless Network Adapter Supports Monitor Mode & Packet Injection
 How To:
Get Root with Metasploit's Local Exploit Suggester
How To:
Get Root with Metasploit's Local Exploit Suggester
 How To:
Top 10 Things to Do After Installing Kali Linux
How To:
Top 10 Things to Do After Installing Kali Linux
 How To:
Use MDK3 for Advanced Wi-Fi Jamming
How To:
Use MDK3 for Advanced Wi-Fi Jamming
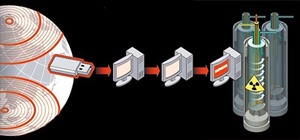 News:
What the Heck Was Stuxnet!?
News:
What the Heck Was Stuxnet!?
 How To:
Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
How To:
Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
 How To:
Gain SSH Access to Servers by Brute-Forcing Credentials
How To:
Gain SSH Access to Servers by Brute-Forcing Credentials
 BT Recon:
How to Snoop on Bluetooth Devices Using Kali Linux
BT Recon:
How to Snoop on Bluetooth Devices Using Kali Linux
 How To:
Hack Apache Tomcat via Malicious WAR File Upload
How To:
Hack Apache Tomcat via Malicious WAR File Upload
 Android for Hackers:
How to Turn an Android Phone into a Hacking Device Without Root
Android for Hackers:
How to Turn an Android Phone into a Hacking Device Without Root
 How To:
Make Your Own Bad USB
How To:
Make Your Own Bad USB
 How To:
Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
How To:
Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
21 Responses
It's hard to say. You can run some vulnerability scans against it and find out.
Anyway, the ports are probably closed.
There must be either port 80 or 443 open for you to access the site, so some ports are open.
Random thought: About 121 exploits for IE6. Last one found was 2 weeks ago with 9.3 out of 10 in not goodness.
We just had a guy with a similar post about his port 80 from india. Some light digging found he was being port forwarded to some random high ports above 1000 by his ISP. (Don't ask me how I know.)
Like he said run a scan against it if you would like to be certain.
What kind of scanners should we be using?
Nikto, Nmap, Burp?
There are many web application scanners. nmap won't help. It's used to determine the ports, OS and services that are running.
Nikto or Wikto are both good and free. There are many commercial web app vulnerability scanners that will give you a free trial license like Qualys, Acunetix, Nexpose and many others. Usually these free trials are full featured and good for 7-30 days.
This is my Nikto scan result : (Fast scan)
VM-HoneyPot
eth1 Link encap:Ethernet HWaddr 00:0D:60:xx:xx:xx
inet addr:xxx.xx.xx.x Bcast:xxx.xx.xx.xxx Mask:255.255.255.0
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:2679782 errors:0 dropped:0 overruns:0 frame:0
TX packets:46733 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:497213909 (474.1 Mb) TX bytes:2991455 (2.8 Mb)
Interrupt:17
wut
Exactly..
BTW that is from a public recon run against the pot. Always follow the right path and do recon on the target before you scan anything.
Brilliant demonstration.
i see, it's a trap...
How did you figure out it was a honeypot?
yup. care to explain how you figured it was a honeypot ? Thx
Greetings, allow me to explain. The nikito scan hinted, well screamed at my conclusion.
The target IP was not scanned or visited once during this process.
Protocol dictates that actionable Intel is needed before any force of action is taken. You don't close your eyes then pull out a gun and fire wildly, do you?
Total Time: About 3 mins
Scripts : 0
Technique: GOOGLE DORK
0.5 First clue was out of date Gov website. : They have checklists for any and all devices to be set up to SPEC.
ARIN LOOKUP
3.1 clue maybe http://datatracker.ietf.org/doc/rfc1918/
3.5 Domain Records shows something like a game site or Data Center?? ~NOT A GOV SITE as we thought! WTF is it???
Let's Dork it!
4.05 "ADMIN: Mxxxx Szxxxx"
TITLE: Systems Admin/Engineer
DEPT: Enterprise Web Services
COMPANY: Cxxxx TECHxxxxxx
ADDRESS: Level xx, xxxx Ann Street, BRISBANE QLD 4000
PHONE: +61 x xxxx 7151"
4.1 Dork results also gave network topology,IP's in use, Ports, iwconfig tails and hostnames.
*Far too much EASY info for legit server found. Yeah right!*
5.0 Admin made various forum posts about pot ARP poison issue.
5.1 Other INTEL supports 2 other pots reside on the same network
5.2 Hostnames LVS:a & LVS:b - (L)INUX (V)IRTUAL (S)ERVER
WHT TIME LINE :
P.S. Really annoying I had to re write this 3 times because the st00pid editor keeps giving me ajax error........
Excellent work, CyberHitchiker!
Now, this is information gathering! Amazing!
Share Your Thoughts