Hello all, I am about to ask probably one of the newbiest questions ever. I won't give much background info of myself as this profile is my last resort to getting a certain answer. I live in a place where people like to pretend to have done impossible things. A friend of mine told me that he knew a person who can hack "by sending an image" to the other person and basically owning him. I have a little background in exploitation and all that fun stuff, and from what I know I don't think this is possible. I saw a question asked here about something similar and the answer was "yes" by OTW, though I guess he referred to php vulnerabilities making jpeg payloads/viruses possible. I would love to know if such thing is possible outside of that scope, and to what degree. Thanks in advance, hope I wasn't too annoying.
Forum Thread: Mystery Still Unsolved
- Hot
- Active
-
 Forum Thread:
When My Kali Linux Finishes Installing (It Is Ready to Boot), and When I Try to Boot It All I Get Is a Black Screen.
8
Replies
Forum Thread:
When My Kali Linux Finishes Installing (It Is Ready to Boot), and When I Try to Boot It All I Get Is a Black Screen.
8
Replies
16 hrs ago -
 Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
1 wk ago -
 Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
2
Replies
Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
2
Replies
4 wks ago -
 Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
4 wks ago -
 Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
2 mo ago -
 Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
2 mo ago -
 Metasploit Error:
Handler Failed to Bind
41
Replies
Metasploit Error:
Handler Failed to Bind
41
Replies
3 mo ago -
 Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
3 mo ago -
 How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
3 mo ago -
 How to:
Crack Instagram Passwords Using Instainsane
36
Replies
How to:
Crack Instagram Passwords Using Instainsane
36
Replies
3 mo ago -
 Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
3 mo ago -
 Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
3 mo ago -
 Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
4 mo ago -
 How to:
Sign the APK File with Embedded Payload (The Ultimate Guide)
10
Replies
How to:
Sign the APK File with Embedded Payload (The Ultimate Guide)
10
Replies
4 mo ago -
 Forum Thread:
How to Run and Install Kali Linux on a Chromebook
18
Replies
Forum Thread:
How to Run and Install Kali Linux on a Chromebook
18
Replies
5 mo ago -
 Forum Thread:
How to Find Admin Panel Page of a Website?
13
Replies
Forum Thread:
How to Find Admin Panel Page of a Website?
13
Replies
6 mo ago -
 Forum Thread:
can i run kali lenux in windows 10 without reboting my computer
4
Replies
Forum Thread:
can i run kali lenux in windows 10 without reboting my computer
4
Replies
6 mo ago -
 Forum Thread:
How to Hack School Website
11
Replies
Forum Thread:
How to Hack School Website
11
Replies
6 mo ago -
 Forum Thread:
Make a Phishing Page for Harvesting Credentials Yourself
8
Replies
Forum Thread:
Make a Phishing Page for Harvesting Credentials Yourself
8
Replies
6 mo ago -
 Forum Thread:
Creating an Completely Undetectable Executable in Under 15 Minutes!
38
Replies
Forum Thread:
Creating an Completely Undetectable Executable in Under 15 Minutes!
38
Replies
7 mo ago
-
 How To:
Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
How To:
Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
-
 How To:
Scan for Vulnerabilities on Any Website Using Nikto
How To:
Scan for Vulnerabilities on Any Website Using Nikto
-
 Hacking Windows 10:
How to Dump NTLM Hashes & Crack Windows Passwords
Hacking Windows 10:
How to Dump NTLM Hashes & Crack Windows Passwords
-
 How To:
Generate Crackable Wi-Fi Handshakes with an ESP8266-Based Test Network
How To:
Generate Crackable Wi-Fi Handshakes with an ESP8266-Based Test Network
-
 How To:
Crack SSH Private Key Passwords with John the Ripper
How To:
Crack SSH Private Key Passwords with John the Ripper
-
 How To:
Find Identifying Information from a Phone Number Using OSINT Tools
How To:
Find Identifying Information from a Phone Number Using OSINT Tools
-
 How to Hack Wi-Fi:
Cracking WPA2 Passwords Using the New PMKID Hashcat Attack
How to Hack Wi-Fi:
Cracking WPA2 Passwords Using the New PMKID Hashcat Attack
-
 BT Recon:
How to Snoop on Bluetooth Devices Using Kali Linux
BT Recon:
How to Snoop on Bluetooth Devices Using Kali Linux
-
 How To:
Scrape Target Email Addresses with TheHarvester
How To:
Scrape Target Email Addresses with TheHarvester
-
 How To:
Get Root with Metasploit's Local Exploit Suggester
How To:
Get Root with Metasploit's Local Exploit Suggester
-
 Hack Like a Pro:
How to Find Directories in Websites Using DirBuster
Hack Like a Pro:
How to Find Directories in Websites Using DirBuster
-
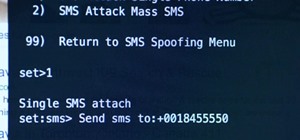
 The Hacks of Mr. Robot:
How to Send a Spoofed SMS Text Message
The Hacks of Mr. Robot:
How to Send a Spoofed SMS Text Message
-
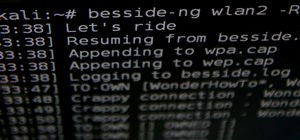
 How to Hack Wi-Fi:
Automating Wi-Fi Hacking with Besside-ng
How to Hack Wi-Fi:
Automating Wi-Fi Hacking with Besside-ng
-
 How To:
Load Kali Linux on the Raspberry Pi 4 for the Ultimate Miniature Hacking Station
How To:
Load Kali Linux on the Raspberry Pi 4 for the Ultimate Miniature Hacking Station
-
 How To:
Dox Anyone
How To:
Dox Anyone
-
 How To:
Crack Shadow Hashes After Getting Root on a Linux System
How To:
Crack Shadow Hashes After Getting Root on a Linux System
-
 How To:
Find Vulnerable Webcams Across the Globe Using Shodan
How To:
Find Vulnerable Webcams Across the Globe Using Shodan
-
 How To:
Gain SSH Access to Servers by Brute-Forcing Credentials
How To:
Gain SSH Access to Servers by Brute-Forcing Credentials
-
 How To:
Exploit Shellshock on a Web Server Using Metasploit
How To:
Exploit Shellshock on a Web Server Using Metasploit
-
 How To:
Brute-Force Nearly Any Website Login with Hatch
How To:
Brute-Force Nearly Any Website Login with Hatch















6 Responses
search youtube using these terms: backdoor image armitage... you'll be surprised
Not a single one found that actually results in a "functioning backdoored image" (sounds pretty rediculous to me, even though I know mostly anything is possible with a cpu and the correct additions :D)
I guess something similar is possible using steganography, don't remember where I read it, but it was a reputed source.
-The Joker
Stenography is really just storing information in an image.video/etc. It doesn't have any thing to do with having a backdoored image.
Cheers,
Washu
Yes I know that, but that was how I was introduced to the term steganography. I don't remember the exact place of reading it, but it was a reputed one.
-The Joker
Recently there was an android exploit called "Stagefright" with which you could send a video to an android phone and exploit it yet its been fixed and its very hard to pull off.
Cheers,
Washu
Share Your Thoughts