So i have been going through all the post's on here and practicing on some computers mainly mine, family and friends and learned how easy it was to gain access and browse all files access camera and microphone... but my question is how do i test other services for weakness's ? you hear about people finding bugs in facebook's server and getting rewarded etc.. is it just a matter right "lets sit here and hack facebook, if i get in woohoo (what to do now share or report)"... or is they something else ??? sorry about the dumbness of the question, i just want to take what i have learned into the real world and find weakness, but dont want that weakness to be a honeypot as such and im caught up in a big hacking scandal and spending the rest of my life in jail..
Forum Thread: Testing Skills Learnt to Find Weakness's
- Hot
- Active
-
 Forum Thread:
Whatsapp Hack?
16
Replies
Forum Thread:
Whatsapp Hack?
16
Replies
1 day ago -
 Forum Thread:
How to Track Who Is Sms Bombing Me .
4
Replies
Forum Thread:
How to Track Who Is Sms Bombing Me .
4
Replies
2 mo ago -
 Forum Thread:
Removing Pay-as-You-Go Meter on Loan Phones.
1
Replies
Forum Thread:
Removing Pay-as-You-Go Meter on Loan Phones.
1
Replies
2 mo ago -
 Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
3
Replies
Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
3
Replies
2 mo ago -
 Forum Thread:
moab5.Sh Error While Running Metasploit
17
Replies
Forum Thread:
moab5.Sh Error While Running Metasploit
17
Replies
3 mo ago -
 Forum Thread:
Execute Reverse PHP Shell with Metasploit
1
Replies
Forum Thread:
Execute Reverse PHP Shell with Metasploit
1
Replies
5 mo ago -
 Forum Thread:
Install Metasploit Framework in Termux No Root Needed M-Wiz Tool
1
Replies
Forum Thread:
Install Metasploit Framework in Termux No Root Needed M-Wiz Tool
1
Replies
5 mo ago -
 Forum Thread:
Hack and Track People's Device Constantly Using TRAPE
35
Replies
Forum Thread:
Hack and Track People's Device Constantly Using TRAPE
35
Replies
6 mo ago -
 Forum Thread:
When My Kali Linux Finishes Installing (It Is Ready to Boot), and When I Try to Boot It All I Get Is a Black Screen.
8
Replies
Forum Thread:
When My Kali Linux Finishes Installing (It Is Ready to Boot), and When I Try to Boot It All I Get Is a Black Screen.
8
Replies
7 mo ago -
 Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
7 mo ago -
 Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
8 mo ago -
 Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
9 mo ago -
 Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
9 mo ago -
 Metasploit Error:
Handler Failed to Bind
41
Replies
Metasploit Error:
Handler Failed to Bind
41
Replies
10 mo ago -
 Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
10 mo ago -
 How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
10 mo ago -
 How to:
Crack Instagram Passwords Using Instainsane
36
Replies
How to:
Crack Instagram Passwords Using Instainsane
36
Replies
10 mo ago -
 Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
10 mo ago -
 Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
10 mo ago -
 Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
11 mo ago
-
 How To:
Scan for Vulnerabilities on Any Website Using Nikto
How To:
Scan for Vulnerabilities on Any Website Using Nikto
-
 How To:
Find Vulnerable Webcams Across the Globe Using Shodan
How To:
Find Vulnerable Webcams Across the Globe Using Shodan
-
 How To:
Crack Wi-Fi Passwords—For Beginners!
How To:
Crack Wi-Fi Passwords—For Beginners!
-
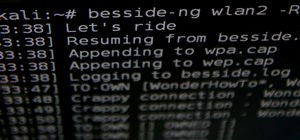 How to Hack Wi-Fi:
Automating Wi-Fi Hacking with Besside-ng
How to Hack Wi-Fi:
Automating Wi-Fi Hacking with Besside-ng
-
 How To:
Take Control of the Mouse & Keyboard in Python
How To:
Take Control of the Mouse & Keyboard in Python
-
 How To:
Find Identifying Information from a Phone Number Using OSINT Tools
How To:
Find Identifying Information from a Phone Number Using OSINT Tools
-
 How To:
Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
How To:
Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
-
 How To:
Spy on Traffic from a Smartphone with Wireshark
How To:
Spy on Traffic from a Smartphone with Wireshark
-
 How To:
Exploit EternalBlue on Windows Server with Metasploit
How To:
Exploit EternalBlue on Windows Server with Metasploit
-
 How To:
Make Your Own Bad USB
How To:
Make Your Own Bad USB
-
 How to Hack Wi-Fi:
Stealing Wi-Fi Passwords with an Evil Twin Attack
How to Hack Wi-Fi:
Stealing Wi-Fi Passwords with an Evil Twin Attack
-
 How To:
Create Custom Wordlists for Password Cracking Using the Mentalist
How To:
Create Custom Wordlists for Password Cracking Using the Mentalist
-
 How To:
Write an XSS Cookie Stealer in JavaScript to Steal Passwords
How To:
Write an XSS Cookie Stealer in JavaScript to Steal Passwords
-
 How To:
Set Up a Headless Raspberry Pi Hacking Platform Running Kali Linux
How To:
Set Up a Headless Raspberry Pi Hacking Platform Running Kali Linux
-
 How To:
Host Your Own Tor Hidden Service with a Custom Onion Address
How To:
Host Your Own Tor Hidden Service with a Custom Onion Address
-
 How to Hack Wi-Fi:
Breaking a WPS PIN to Get the Password with Bully
How to Hack Wi-Fi:
Breaking a WPS PIN to Get the Password with Bully
-
 Video:
How to Crack Weak Wi-Fi Passwords in Seconds with Airgeddon on Parrot OS
Video:
How to Crack Weak Wi-Fi Passwords in Seconds with Airgeddon on Parrot OS
-
 How to Hack Wi-Fi:
Getting Started with Terms & Technologies
How to Hack Wi-Fi:
Getting Started with Terms & Technologies
-
 How To:
Find Anyone's Private Phone Number Using Facebook
How To:
Find Anyone's Private Phone Number Using Facebook
-
 How To:
Intercept & Analyze LAN Traffic with a Packet Squirrel & Wireshark
How To:
Intercept & Analyze LAN Traffic with a Packet Squirrel & Wireshark
















2 Responses
This is a great question.
Finding security holes in large company's websites can be a gray area with a lot of ethical and legal questions that can arise.
Your best bet, especially as a beginner, is to stick to publicly advertised "bug hunts". Like United Airlines which recently awarded a bug finder a bunch of sky miles for a security hole that he found.
If you search the web, there are also limited time events to try to hack public systems to find weaknesses. Stick to those systems and there's no gray area.
Link.
ghost_
Share Your Thoughts