Recently I came into that hacking thing, and of course the first thing I tried, was the aircrack-ng. As far as the cracking is concerned, I didn't managed to do it, because I don't have the computer power to crack it under 2.5 days. So I gave up. But I found out that when I start monitoring the particular network, I can dump certain users using their Mac with aireplay-ng, as well as the whole network. But when I tried this, on my school network (just for fun) I realised that I didn't knew which Mac belongs to which user. And I'm asking for any way to identify the person I'd like to dump. For example, to send them to a webpage, which requests a lot of data and to track the biggest number of data or some social engineering way. (sorry for the bad terminological language (I'm new to this stuff) and for my poor English)
- Hot
- Active
-
 Forum Thread:
How to Track Who Is Sms Bombing Me .
4
Replies
Forum Thread:
How to Track Who Is Sms Bombing Me .
4
Replies
1 mo ago -
 Forum Thread:
Removing Pay-as-You-Go Meter on Loan Phones.
1
Replies
Forum Thread:
Removing Pay-as-You-Go Meter on Loan Phones.
1
Replies
2 mo ago -
 Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
3
Replies
Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
3
Replies
2 mo ago -
 Forum Thread:
moab5.Sh Error While Running Metasploit
17
Replies
Forum Thread:
moab5.Sh Error While Running Metasploit
17
Replies
3 mo ago -
 Forum Thread:
Execute Reverse PHP Shell with Metasploit
1
Replies
Forum Thread:
Execute Reverse PHP Shell with Metasploit
1
Replies
4 mo ago -
 Forum Thread:
Install Metasploit Framework in Termux No Root Needed M-Wiz Tool
1
Replies
Forum Thread:
Install Metasploit Framework in Termux No Root Needed M-Wiz Tool
1
Replies
5 mo ago -
 Forum Thread:
Hack and Track People's Device Constantly Using TRAPE
35
Replies
Forum Thread:
Hack and Track People's Device Constantly Using TRAPE
35
Replies
5 mo ago -
 Forum Thread:
When My Kali Linux Finishes Installing (It Is Ready to Boot), and When I Try to Boot It All I Get Is a Black Screen.
8
Replies
Forum Thread:
When My Kali Linux Finishes Installing (It Is Ready to Boot), and When I Try to Boot It All I Get Is a Black Screen.
8
Replies
6 mo ago -
 Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
7 mo ago -
 Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
7 mo ago -
 Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
9 mo ago -
 Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
9 mo ago -
 Metasploit Error:
Handler Failed to Bind
41
Replies
Metasploit Error:
Handler Failed to Bind
41
Replies
9 mo ago -
 Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
10 mo ago -
 How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
10 mo ago -
 How to:
Crack Instagram Passwords Using Instainsane
36
Replies
How to:
Crack Instagram Passwords Using Instainsane
36
Replies
10 mo ago -
 Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
10 mo ago -
 Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
10 mo ago -
 Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
11 mo ago -
 How to:
Sign the APK File with Embedded Payload (The Ultimate Guide)
10
Replies
How to:
Sign the APK File with Embedded Payload (The Ultimate Guide)
10
Replies
11 mo ago
-
 How To:
Scan for Vulnerabilities on Any Website Using Nikto
How To:
Scan for Vulnerabilities on Any Website Using Nikto
-
 How To:
Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
How To:
Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
-
 How To:
Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
How To:
Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
-
 How To:
Spy on Traffic from a Smartphone with Wireshark
How To:
Spy on Traffic from a Smartphone with Wireshark
-
 How To:
Use SpiderFoot for OSINT Gathering
How To:
Use SpiderFoot for OSINT Gathering
-
 How To:
Gain SSH Access to Servers by Brute-Forcing Credentials
How To:
Gain SSH Access to Servers by Brute-Forcing Credentials
-
 How To:
Host Your Own Tor Hidden Service with a Custom Onion Address
How To:
Host Your Own Tor Hidden Service with a Custom Onion Address
-
 Tutorial:
Create Wordlists with Crunch
Tutorial:
Create Wordlists with Crunch
-
 How To:
Enable Monitor Mode & Packet Injection on the Raspberry Pi
How To:
Enable Monitor Mode & Packet Injection on the Raspberry Pi
-
 How To:
Hunt Down Social Media Accounts by Usernames with Sherlock
How To:
Hunt Down Social Media Accounts by Usernames with Sherlock
-
 How To:
Get Root with Metasploit's Local Exploit Suggester
How To:
Get Root with Metasploit's Local Exploit Suggester
-
 How To:
Intercept Images from a Security Camera Using Wireshark
How To:
Intercept Images from a Security Camera Using Wireshark
-
 How To:
Escape Restricted Shell Environments on Linux
How To:
Escape Restricted Shell Environments on Linux
-
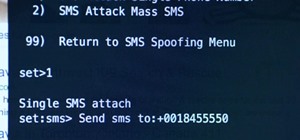
 The Hacks of Mr. Robot:
How to Send a Spoofed SMS Text Message
The Hacks of Mr. Robot:
How to Send a Spoofed SMS Text Message
-
 How To:
Attack Web Applications with Burp Suite & SQL Injection
How To:
Attack Web Applications with Burp Suite & SQL Injection
-
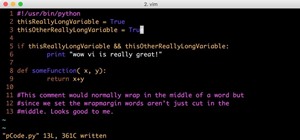
 How To:
An Intro to Vim, the Unix Text Editor Every Hacker Should Be Familiar With
How To:
An Intro to Vim, the Unix Text Editor Every Hacker Should Be Familiar With
-
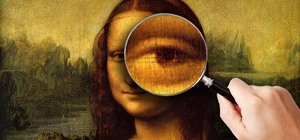
 How To:
An Introduction to Steganography & Its Uses
How To:
An Introduction to Steganography & Its Uses
-
 How To:
Perform Local Privilege Escalation Using a Linux Kernel Exploit
How To:
Perform Local Privilege Escalation Using a Linux Kernel Exploit
-
 How To:
Log into Your Raspberry Pi Using a USB-to-TTL Serial Cable
How To:
Log into Your Raspberry Pi Using a USB-to-TTL Serial Cable
-
 Networking Foundations:
Subnetting Based on Host Requirements
Networking Foundations:
Subnetting Based on Host Requirements













Be the First to Respond
Share Your Thoughts