Read about this from The Hacker News
- Hot
- Active
-
 Forum Thread:
How to Track Who Is Sms Bombing Me .
4
Replies
Forum Thread:
How to Track Who Is Sms Bombing Me .
4
Replies
2 mo ago -
 Forum Thread:
Removing Pay-as-You-Go Meter on Loan Phones.
1
Replies
Forum Thread:
Removing Pay-as-You-Go Meter on Loan Phones.
1
Replies
2 mo ago -
 Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
3
Replies
Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
3
Replies
2 mo ago -
 Forum Thread:
moab5.Sh Error While Running Metasploit
17
Replies
Forum Thread:
moab5.Sh Error While Running Metasploit
17
Replies
3 mo ago -
 Forum Thread:
Execute Reverse PHP Shell with Metasploit
1
Replies
Forum Thread:
Execute Reverse PHP Shell with Metasploit
1
Replies
5 mo ago -
 Forum Thread:
Install Metasploit Framework in Termux No Root Needed M-Wiz Tool
1
Replies
Forum Thread:
Install Metasploit Framework in Termux No Root Needed M-Wiz Tool
1
Replies
5 mo ago -
 Forum Thread:
Hack and Track People's Device Constantly Using TRAPE
35
Replies
Forum Thread:
Hack and Track People's Device Constantly Using TRAPE
35
Replies
6 mo ago -
 Forum Thread:
When My Kali Linux Finishes Installing (It Is Ready to Boot), and When I Try to Boot It All I Get Is a Black Screen.
8
Replies
Forum Thread:
When My Kali Linux Finishes Installing (It Is Ready to Boot), and When I Try to Boot It All I Get Is a Black Screen.
8
Replies
7 mo ago -
 Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
7 mo ago -
 Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
7 mo ago -
 Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
9 mo ago -
 Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
9 mo ago -
 Metasploit Error:
Handler Failed to Bind
41
Replies
Metasploit Error:
Handler Failed to Bind
41
Replies
10 mo ago -
 Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
10 mo ago -
 How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
10 mo ago -
 How to:
Crack Instagram Passwords Using Instainsane
36
Replies
How to:
Crack Instagram Passwords Using Instainsane
36
Replies
10 mo ago -
 Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
10 mo ago -
 Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
10 mo ago -
 Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
11 mo ago -
 How to:
Sign the APK File with Embedded Payload (The Ultimate Guide)
10
Replies
How to:
Sign the APK File with Embedded Payload (The Ultimate Guide)
10
Replies
11 mo ago
-
 How To:
Hijacking Cookie Sessions
How To:
Hijacking Cookie Sessions
-
 How To:
Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
How To:
Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
-
 How To:
Scan for Vulnerabilities on Any Website Using Nikto
How To:
Scan for Vulnerabilities on Any Website Using Nikto
-
 How To:
Find Vulnerable Webcams Across the Globe Using Shodan
How To:
Find Vulnerable Webcams Across the Globe Using Shodan
-
 How To:
Find Passwords in Exposed Log Files with Google Dorks
How To:
Find Passwords in Exposed Log Files with Google Dorks
-
 How To:
Use SpiderFoot for OSINT Gathering
How To:
Use SpiderFoot for OSINT Gathering
-
 How To:
Hunt Down Social Media Accounts by Usernames with Sherlock
How To:
Hunt Down Social Media Accounts by Usernames with Sherlock
-
 How To:
Use an ESP8266 Beacon Spammer to Track Smartphone Users
How To:
Use an ESP8266 Beacon Spammer to Track Smartphone Users
-
 How To:
Detect When a Device Is Nearby with the ESP8266 Friend Detector
How To:
Detect When a Device Is Nearby with the ESP8266 Friend Detector
-
 How To:
Fix Bidirectional Copy/Paste Issues for Kali Linux Running in VirtualBox
How To:
Fix Bidirectional Copy/Paste Issues for Kali Linux Running in VirtualBox
-
 How To:
Dump a MacOS User's Chrome Passwords with EvilOSX
How To:
Dump a MacOS User's Chrome Passwords with EvilOSX
-
 Hacking Windows 10:
How to Bypass VirusTotal & AMSI Detection Signatures with Chimera
Hacking Windows 10:
How to Bypass VirusTotal & AMSI Detection Signatures with Chimera
-
 Advice from a Real Hacker:
How I Would Build the God's Eye of Furious 7
Advice from a Real Hacker:
How I Would Build the God's Eye of Furious 7
-
 Hack Like a Pro:
Capturing Zero-Day Exploits in the Wild with a Dionaea Honeypot, Part 1
Hack Like a Pro:
Capturing Zero-Day Exploits in the Wild with a Dionaea Honeypot, Part 1
-
 Hack Like a Pro:
How to Evade a Network Intrusion Detection System (NIDS) Using Snort
Hack Like a Pro:
How to Evade a Network Intrusion Detection System (NIDS) Using Snort
-
 How To:
Conduct Wireless Recon on Bluetooth, Wi-Fi & GPS with Sparrow-wifi
How To:
Conduct Wireless Recon on Bluetooth, Wi-Fi & GPS with Sparrow-wifi
-
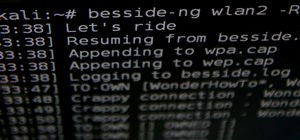
 How to Hack Wi-Fi:
Automating Wi-Fi Hacking with Besside-ng
How to Hack Wi-Fi:
Automating Wi-Fi Hacking with Besside-ng
-
 Advice from a Real Hacker:
How to Know if You've Been Hacked
Advice from a Real Hacker:
How to Know if You've Been Hacked
-
 How To:
Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
How To:
Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
-
 How To:
Find Identifying Information from a Phone Number Using OSINT Tools
How To:
Find Identifying Information from a Phone Number Using OSINT Tools















8 Responses
If these courses are any way decent, that looks like a great resource. Have you taken any of the courses there?
I'm currently trying out systems administration. Some of the courses are still unavailable. You could follow this guide by sir OTW
https://null-byte.wonderhowto.com/forum/train-be-security-professional-ethical-hacker-0158783/
Thanks, and for the share anyway. I tend to be suspicious of free stuff like this, but there's no harm in checking it out.
Your sharing definitely deserve an upvote. Thx for sharing
Yeah knew about this site. No one to explain the content if you have questions and you can just say you completed the course and buy the badge for 3 bucks. Great share for someone though.
So is it a good or a bad thing? Would you recommend that site?
Well as a site to go look at video content sure. As a pure training tool , Negative. Like I said before for some this will be just what they wanted. For me its not what I need in any way shape or form. But at one time I would of loved something like this.
So as with anything it has its pros and cons. I would be more happy with a CISSP or a CEH V8 Torrent.
Ok that was a good review I guess. Thanks.
Share Your Thoughts