I recently tried looking for vulnerabilities to a computer with armitage but I couldn't find any.Besides a Payload would they be another way in?
Forum Thread: Any Other Way into a System?
- Hot
- Active
-
 Forum Thread:
Whatsapp Hack?
16
Replies
Forum Thread:
Whatsapp Hack?
16
Replies
18 hrs ago -
 Forum Thread:
How to Track Who Is Sms Bombing Me .
4
Replies
Forum Thread:
How to Track Who Is Sms Bombing Me .
4
Replies
2 mo ago -
 Forum Thread:
Removing Pay-as-You-Go Meter on Loan Phones.
1
Replies
Forum Thread:
Removing Pay-as-You-Go Meter on Loan Phones.
1
Replies
2 mo ago -
 Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
3
Replies
Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
3
Replies
2 mo ago -
 Forum Thread:
moab5.Sh Error While Running Metasploit
17
Replies
Forum Thread:
moab5.Sh Error While Running Metasploit
17
Replies
3 mo ago -
 Forum Thread:
Execute Reverse PHP Shell with Metasploit
1
Replies
Forum Thread:
Execute Reverse PHP Shell with Metasploit
1
Replies
5 mo ago -
 Forum Thread:
Install Metasploit Framework in Termux No Root Needed M-Wiz Tool
1
Replies
Forum Thread:
Install Metasploit Framework in Termux No Root Needed M-Wiz Tool
1
Replies
5 mo ago -
 Forum Thread:
Hack and Track People's Device Constantly Using TRAPE
35
Replies
Forum Thread:
Hack and Track People's Device Constantly Using TRAPE
35
Replies
6 mo ago -
 Forum Thread:
When My Kali Linux Finishes Installing (It Is Ready to Boot), and When I Try to Boot It All I Get Is a Black Screen.
8
Replies
Forum Thread:
When My Kali Linux Finishes Installing (It Is Ready to Boot), and When I Try to Boot It All I Get Is a Black Screen.
8
Replies
7 mo ago -
 Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
7 mo ago -
 Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
8 mo ago -
 Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
9 mo ago -
 Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
9 mo ago -
 Metasploit Error:
Handler Failed to Bind
41
Replies
Metasploit Error:
Handler Failed to Bind
41
Replies
10 mo ago -
 Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
10 mo ago -
 How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
10 mo ago -
 How to:
Crack Instagram Passwords Using Instainsane
36
Replies
How to:
Crack Instagram Passwords Using Instainsane
36
Replies
10 mo ago -
 Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
10 mo ago -
 Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
10 mo ago -
 Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
11 mo ago
-
How To: Fake Captive Portal with an Android Phone
-
 How To:
Hack WPA & WPA2 Wi-Fi Passwords with a Pixie-Dust Attack Using Airgeddon
How To:
Hack WPA & WPA2 Wi-Fi Passwords with a Pixie-Dust Attack Using Airgeddon
-
 How To:
Phish for Social Media & Other Account Passwords with BlackEye
How To:
Phish for Social Media & Other Account Passwords with BlackEye
-
 How To:
Use Meterpeter on OS X
How To:
Use Meterpeter on OS X
-
 How To:
Scan for Vulnerabilities on Any Website Using Nikto
How To:
Scan for Vulnerabilities on Any Website Using Nikto
-
 How To:
Find Vulnerable Webcams Across the Globe Using Shodan
How To:
Find Vulnerable Webcams Across the Globe Using Shodan
-
 How To:
Exploit EternalBlue on Windows Server with Metasploit
How To:
Exploit EternalBlue on Windows Server with Metasploit
-
 How to Hack Wi-Fi:
Stealing Wi-Fi Passwords with an Evil Twin Attack
How to Hack Wi-Fi:
Stealing Wi-Fi Passwords with an Evil Twin Attack
-
 How To:
Beginner's Guide to OWASP Juice Shop, Your Practice Hacking Grounds for the 10 Most Common Web App Vulnerabilities
How To:
Beginner's Guide to OWASP Juice Shop, Your Practice Hacking Grounds for the 10 Most Common Web App Vulnerabilities
-
 How To:
Control Anything with a Wi-Fi Relay Switch Using aRest
How To:
Control Anything with a Wi-Fi Relay Switch Using aRest
-
 How To:
Host Your Own Tor Hidden Service with a Custom Onion Address
How To:
Host Your Own Tor Hidden Service with a Custom Onion Address
-
 How To:
Wardrive with the Kali Raspberry Pi to Map Wi-Fi Devices
How To:
Wardrive with the Kali Raspberry Pi to Map Wi-Fi Devices
-
 How To:
Hack Wi-Fi Networks with Bettercap
How To:
Hack Wi-Fi Networks with Bettercap
-
 The Hacks of Mr. Robot:
How to Build a Hacking Raspberry Pi
The Hacks of Mr. Robot:
How to Build a Hacking Raspberry Pi
-
 How to Hack Wi-Fi:
Get Anyone's Wi-Fi Password Without Cracking Using Wifiphisher
How to Hack Wi-Fi:
Get Anyone's Wi-Fi Password Without Cracking Using Wifiphisher
-
 How To:
Track Wi-Fi Devices & Connect to Them Using Probequest
How To:
Track Wi-Fi Devices & Connect to Them Using Probequest
-
 Exploit Development:
How to Write Specific Values to Memory with Format String Exploitation
Exploit Development:
How to Write Specific Values to Memory with Format String Exploitation
-
 How To:
Scrape Target Email Addresses with TheHarvester
How To:
Scrape Target Email Addresses with TheHarvester
-
 The Hacks of Mr. Robot:
How to Hide Data in Audio Files
The Hacks of Mr. Robot:
How to Hide Data in Audio Files
-
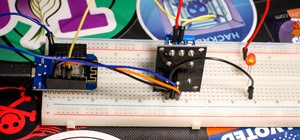
 Hacking Gear:
10 Essential Gadgets Every Hacker Should Try
Hacking Gear:
10 Essential Gadgets Every Hacker Should Try
















2 Responses
Armitage is a bit of a script kiddies tool, there are plenty of exploits on exploit-db that armitage won't pick up. You are much better off scanning with nmap, and researching the services/ results etc that come back until you find an exploit. Armitage is a good tool when you know what you're doing and can research on your own. But i wouldn't use it when starting out, it will make things difficult for you in the long run.
thx!
Share Your Thoughts