![How to Encrypt Python Exploit So It Can Be FUD Again? [DOC EXPLOIT]](https://img.wonderhowto.com/img/31/73/63594733605714/0/encrypt-python-exploit-so-can-be-fud-again-doc-exploit.w1456.jpg)
Hello
I have a silent Doc exploit written in python for the CVE-2015-1650 and CVE-2015-1770 Remote Code Execution ,which had 0 rate detection 2 days ago , somehow a dumb moron uploaded it to virustotal and now it has 15/35 detection rate.
is there a tool or a method to encrypt the python file again so it will be FUD again?
Thanks







































23 Responses
People upload samples to VirusTotal because it's their responsibility as a security analyst or it's someone who doesn't want themselves to get infected so don't go around assuming that it's the behavior of a "dumb moron".
Back on topic: Do you know which part is detected?
the payload
Is it detected on disk or during runtime?
on disk i guess , for example Kaspersky detects it without being executed
Have you tried encrypting it and then decrypting it in memory?
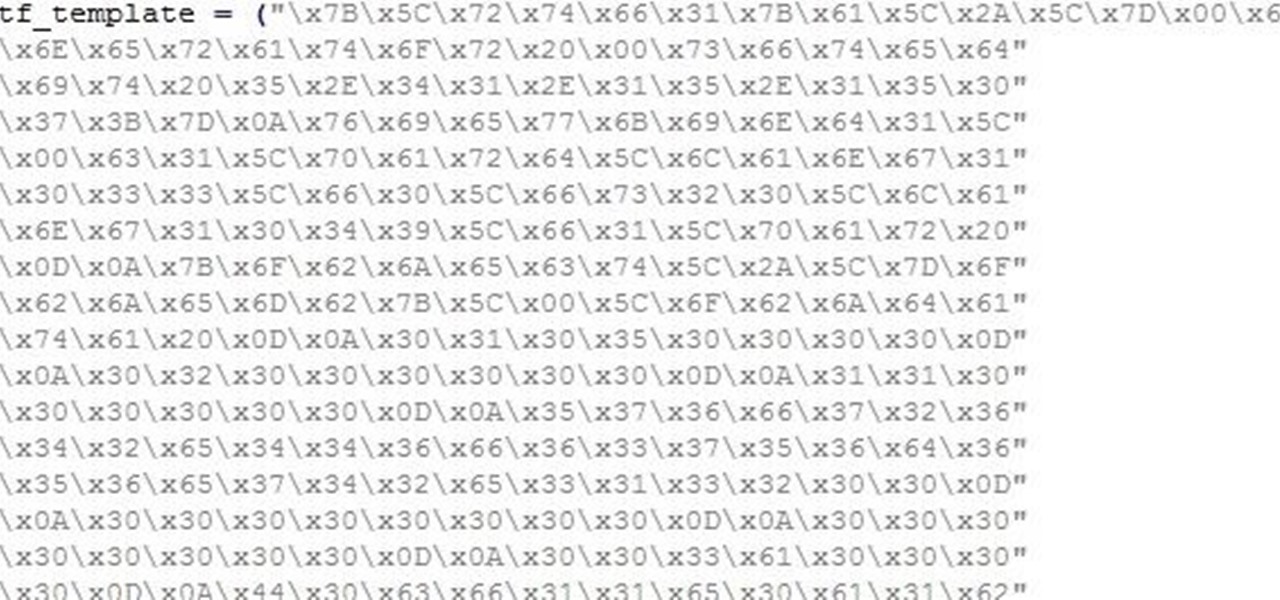
No I didn't .... I have seen other uploads for the same exploit where the payload is being obfuscated ,from this \x7B\x5C\x72\x74\x66\x31\x7B\x61\x5C\x2A\x5C\x7D\x00\x65" to this 7B5C72740A0A0A0A0A0A0A0A0A0A0A0A0A0A0A0A0A0A0A0A0A0A0A0A0A0A0A0A0A"
Perhaps try one of these methods?
can you suggest some tools?
Do you know how to use Python?
basic knowledge
Use XOR to encrypt the shellcode, place the encrypted shellcode into the code, then write a routine to decrypt the buffer. When your code runs, make sure it decrypts the shellcode first before using it.
Thank you so much, a bit hard for me but I will try anyways
Would you please confirm if this shellcode crypter is useful ? Thanks!
http://hacklab.altervista.org/download/shellcodes_crypter_v0.2.c
As long as it's encrypted enough so that the antivirus cannot detect a signature, it's fine. Once you apply the encryption, you'll need the decryption routine inside your code to decode on runtime. For XOR, it should be the exact same operation.
import binascii
header = 'holhola"
binnu=binascii.b2a_hex(header)
print(binnu)
In order to correctly answer this question we need a bit more information like the full exploit code
To refud it you need to figure out what part of the code causes it to be detected like is it the shellcode or maybe the thing that Triggers the vulneribility
If it is the shellcode you can use shelter to generatie new shellcode
If it is the code that Triggers the vulnerebility you can try editing the code so that it still works
Another thing which i very common in buffer overflows is that they randomize the buffer so that the exploit always looks diffrent
ok check it!
this one has a different long shellcode , I've seen others
with shorter ones , thats why i thought maybe its possible to refud it
https://www.indetectables.net/viewtopic.php?f=7&t=54743
Anyone here??
this is cve-2014-1761 not the cve you stated , if your 2015 builder output is rtf send your jabber or skype
yes its rtf skype : saberdz17
I am still waiting for your message mate!
I have failed to encrypt the shellcode , Now i am trying to refud the output .DOC file with Hex editor and Offset locator
Amazing trick by MrTuxracer
https://www.rcesecurity.com/2016/04/slae-polymorphic-shellcodes-linux-x86/
Share Your Thoughts