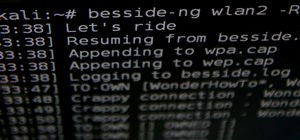
To keep things short I've been experimenting with cracking wpa in aircrack following the tutorial here by OTW. Everything works fine except a handshake is never captured as I am told when I go to run aircrack against the .cap file. I am using the panda PAU09 which plenty of people say works great, and yes the deauth command does work.
I'm testing this in a home lab type set up so I know for sure the device reconnects to the AP, but for some reason I cannot capture the handshake.
I am using the latest version of kali linux on the rpi







































4 Responses
Also I will add that connected clients for the ap do not show up when running the airodump commands to target the specific ap
Try this comand in terminal:
Wifite
Then choose which wifi u want to choose then wifite will automatically handshake with wpa.then go to the aircrack-ng
Wifite also does not work its stays in a loop of deauth and listening for handshake. I even manually connect and disconnect my phone to create a handshake but still no dice.
I considered the problem might be in kali so I flashed parrotsec to another sd card and still have the same problem :(
This is driving me crazy
I managed to get it working. Turns out not all drivers are ported over correctly to arm and that was my issue. There's a user named re4son that puts a lot of work into fixing things on the kali arm image. He has a kernel patch he updates with lots of driver support and supposedly makes kali more efficient. It even adds Onboard Bluetooth support.
It's an easy to run patch that can be found here
https://whitedome.com.au/re4son/re4son-kernel/
Share Your Thoughts