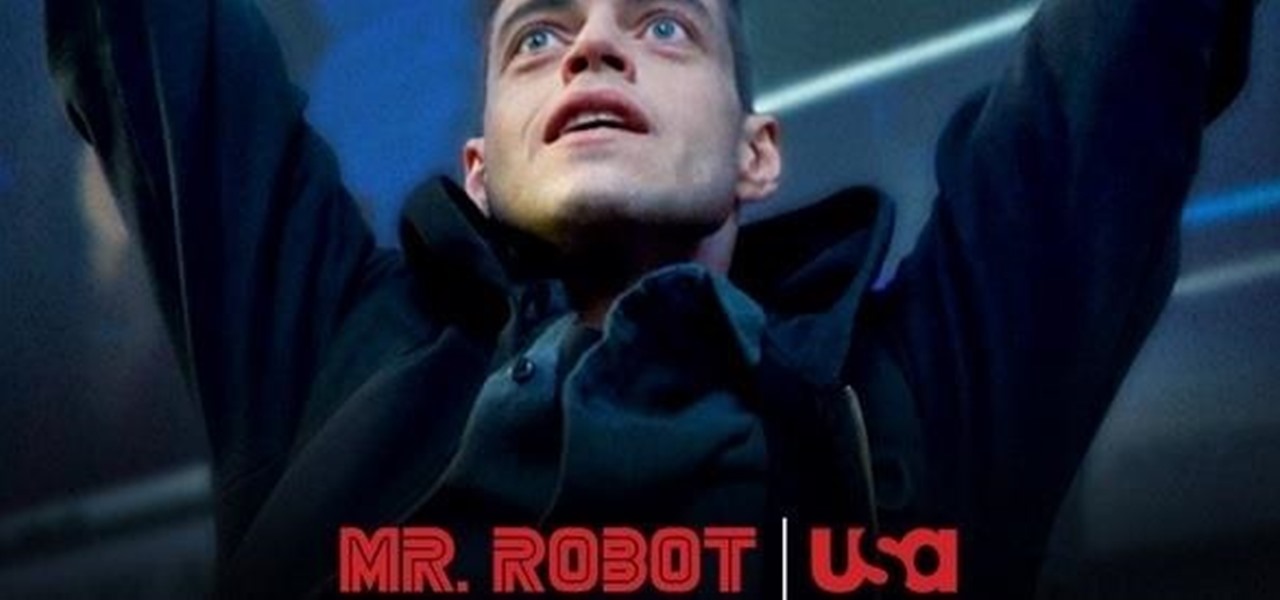
so as you all know last episode of Mr robot finished today whats your opinion on this series specially last episode.
- Hot
- Active
-
 Forum Thread:
Whatsapp Hack?
16
Replies
Forum Thread:
Whatsapp Hack?
16
Replies
1 day ago -
 Forum Thread:
How to Track Who Is Sms Bombing Me .
4
Replies
Forum Thread:
How to Track Who Is Sms Bombing Me .
4
Replies
2 mo ago -
 Forum Thread:
Removing Pay-as-You-Go Meter on Loan Phones.
1
Replies
Forum Thread:
Removing Pay-as-You-Go Meter on Loan Phones.
1
Replies
2 mo ago -
 Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
3
Replies
Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
3
Replies
2 mo ago -
 Forum Thread:
moab5.Sh Error While Running Metasploit
17
Replies
Forum Thread:
moab5.Sh Error While Running Metasploit
17
Replies
3 mo ago -
 Forum Thread:
Execute Reverse PHP Shell with Metasploit
1
Replies
Forum Thread:
Execute Reverse PHP Shell with Metasploit
1
Replies
5 mo ago -
 Forum Thread:
Install Metasploit Framework in Termux No Root Needed M-Wiz Tool
1
Replies
Forum Thread:
Install Metasploit Framework in Termux No Root Needed M-Wiz Tool
1
Replies
5 mo ago -
 Forum Thread:
Hack and Track People's Device Constantly Using TRAPE
35
Replies
Forum Thread:
Hack and Track People's Device Constantly Using TRAPE
35
Replies
6 mo ago -
 Forum Thread:
When My Kali Linux Finishes Installing (It Is Ready to Boot), and When I Try to Boot It All I Get Is a Black Screen.
8
Replies
Forum Thread:
When My Kali Linux Finishes Installing (It Is Ready to Boot), and When I Try to Boot It All I Get Is a Black Screen.
8
Replies
7 mo ago -
 Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
7 mo ago -
 Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
8 mo ago -
 Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
9 mo ago -
 Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
9 mo ago -
 Metasploit Error:
Handler Failed to Bind
41
Replies
Metasploit Error:
Handler Failed to Bind
41
Replies
10 mo ago -
 Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
10 mo ago -
 How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
10 mo ago -
 How to:
Crack Instagram Passwords Using Instainsane
36
Replies
How to:
Crack Instagram Passwords Using Instainsane
36
Replies
10 mo ago -
 Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
10 mo ago -
 Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
10 mo ago -
 Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
11 mo ago
-
 How To:
Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
How To:
Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
-
 How To:
Use Kismet to Watch Wi-Fi User Activity Through Walls
How To:
Use Kismet to Watch Wi-Fi User Activity Through Walls
-
 How To:
Find Identifying Information from a Phone Number Using OSINT Tools
How To:
Find Identifying Information from a Phone Number Using OSINT Tools
-
 How To:
Dox Anyone
How To:
Dox Anyone
-
 How To:
Enumerate SMB with Enum4linux & Smbclient
How To:
Enumerate SMB with Enum4linux & Smbclient
-
 How To:
Crack SSH Private Key Passwords with John the Ripper
How To:
Crack SSH Private Key Passwords with John the Ripper
-
 How To:
Pick an Antenna for Wi-Fi Hacking
How To:
Pick an Antenna for Wi-Fi Hacking
-
 How to Hack Wi-Fi:
Cracking WPA2 Passwords Using the New PMKID Hashcat Attack
How to Hack Wi-Fi:
Cracking WPA2 Passwords Using the New PMKID Hashcat Attack
-
 How To:
Set Your Wi-Fi Card's TX Power Higher Than 30 dBm
How To:
Set Your Wi-Fi Card's TX Power Higher Than 30 dBm
-
 How to Hack Wi-Fi:
Get Anyone's Wi-Fi Password Without Cracking Using Wifiphisher
How to Hack Wi-Fi:
Get Anyone's Wi-Fi Password Without Cracking Using Wifiphisher
-
 How To:
Hack Wi-Fi Networks with Bettercap
How To:
Hack Wi-Fi Networks with Bettercap
-
 Mac for Hackers:
How to Install Kali Linux as a Virtual Machine
Mac for Hackers:
How to Install Kali Linux as a Virtual Machine
-
 How To:
Set Up a Headless Raspberry Pi Hacking Platform Running Kali Linux
How To:
Set Up a Headless Raspberry Pi Hacking Platform Running Kali Linux
-
 How To:
Write Your Own Bash Scripts to Automate Tasks on Linux
How To:
Write Your Own Bash Scripts to Automate Tasks on Linux
-
 How to Hack Wi-Fi:
Cracking WPA2-PSK Passwords with Cowpatty
How to Hack Wi-Fi:
Cracking WPA2-PSK Passwords with Cowpatty
-
 How To:
Conduct a Pentest Like a Pro in 6 Phases
How To:
Conduct a Pentest Like a Pro in 6 Phases
-
 Hack Like a Pro:
How to Crack Online Web Form Passwords with THC-Hydra & Burp Suite
Hack Like a Pro:
How to Crack Online Web Form Passwords with THC-Hydra & Burp Suite
-
 How To:
Hack Web Browsers with BeEF to Control Webcams, Phish for Credentials & More
How To:
Hack Web Browsers with BeEF to Control Webcams, Phish for Credentials & More
-
 How To:
Dump a MacOS User's Chrome Passwords with EvilOSX
How To:
Dump a MacOS User's Chrome Passwords with EvilOSX
-
 How to Hack Wi-Fi:
Getting Started with the Aircrack-Ng Suite of Wi-Fi Hacking Tools
How to Hack Wi-Fi:
Getting Started with the Aircrack-Ng Suite of Wi-Fi Hacking Tools
















6 Responses
It got a bid wired towards the end. But more then anything it was still brilliant concerned as to ware Tyrell is haha but can't wait to season 2 in 2016. And its ashamed wouldn't get to see the actual execution.
It's the best realistic hacking drama ever seen.
best thing was when that guy said her wife catch him from ashleymadison dump shit. or how they destroyed hards these dump and methods just got public god damn i love director of this movie.
I think Elliot Alderson is a cool cyber security engineer.
And he has some kind of super power.
He wants to do the things right.
As he said: " I WANTED TO SAVE THE WORLD".
It really shows what a hacker can do.
Hope you have a wonderful day,viewer.
-------------------DAGONCHU
Just realized the main character is Joshua from Until Dawn.
Blew my mind, I love that actor.
Ollie Parker(Angela's boyfriend) is really stupid for someone who works in a cybersecurity firm.
Share Your Thoughts