What's New in Kali Rolling?
Kali Rolling Release vs Standard Releases
To get a better understanding of the changes that this brings to Kali, a clearer picture of how rolling releases work is needed. Rather than Kali basing itself off standard Debian releases (such as Debian 7, 8, 9) and going through the cyclic phases of "new, mainstream, outdated", the Kali rolling release feeds continuously from Debian testing, ensuring a constant flow of the latest package versions.
Each of these methods of updating software has advantages and disadvantages. For example, with a rolling release, major bugs may appear in a production system. On the other hand, major improvements may take months, or even years, to appear in a fixed-release Linux.
I can see the arguments for both sides. Personally, I believe that rolling releases should only be deployed by experts for their own use or for customers who demand hot, new improvements. For everyone else, I think the stability of fixed-release distributions make them a better choice, especially for production environments.
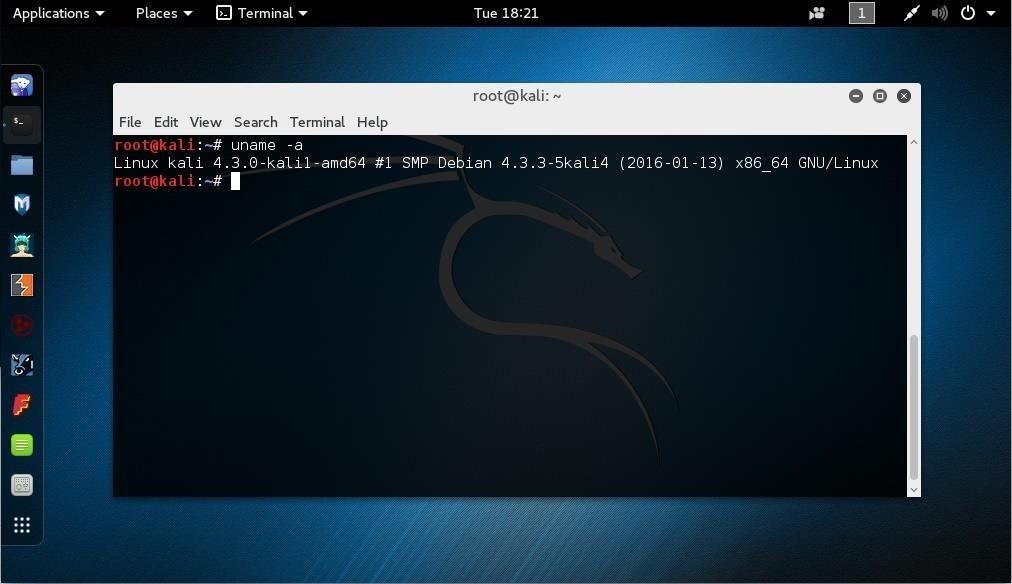
Transitioning from Kali 2.0 to Kali Rolling
Migrating from Kali sana (2.0) to Kali rolling is simple. As root, you can run the following commands and be on your way:
cat << EOF > /etc/apt/sources.list
deb http://http.kali.org/kali kali-rolling main non-free contrib
EOF
apt-get update
apt-get dist-upgrade # get a coffee, or 10.
reboot
Please note that the Kali sana repositories will no longer be updated and will be EOL'd on the 15th of April 2016.
VMware Tools vs Open-VM-Tools
This release also marks a dramatic change around how VMware guest tools are installed. As of Sept 2015, VMware recommends using the distribution-specific open-vm-tools instead of the VMware Tools package for guest machines. We have made sure that our package installs and works correctly with the latest Kali rolling kernel and are happy to see that all the needed functionality such as file copying, clipboard copy/paste and automatic screen resizing are working perfectly. To install open-vm-tools in your Kali Rolling image, enter:
apt-get update
apt-get install open-vm-tools-desktop fuse
reboot
Download Kali Linux Rolling 2016.1
Download at Kali Linux Download Page
& Kali Linux Rolling Virtual & ARM Images Click Offensive Security Page







































1 Response
Another great new feature is that it now breaks every other second :D
For example virtualbox is something that JUST DOESNT WORK :D :D
Other great updates include not being able to upgrade without at least 30 error messages or some mirrors not being up to date.
Share Your Thoughts