Hi there,
Just a short question.
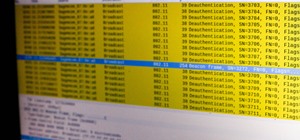
When I set-up a regular handler (use/exploit/multi/handler), with LHOST and LPORT, and click exploit without my test computer being online atm. Metasploit starts sending stages to random unknown IP's after a few minutes, so far I've sent stages to the US, Italy, and most recently to several IP's in Saudi Arabia.
This is not supposed to happen, right? Can I get into trouble if metasploit sends a stage to a computer that's being monitored?
The computer I practice on is outside of my LAN, if that matters.
Thanks in advance,
Ulf.








































7 Responses
Thats not possible..
How did you know it's sending to which countries
it happened to me many times and that's what i noticed:
1) it happened when i set the multi/handler and then checked if port 4444 was open by going to canyouseeme.org...as soon as i clicked on the check button, metasploit started to send stages to a strange ip address on amazon clouds...when i did a whois check on the IP, i found that it belonged to canyouseeme.org.
2) in another instance, it started sending stages to IP addresses that i didn't know...i was using a VPN service then...i checked with some friends of mine and they told me that if someone else using that VPN server and sets up the same multi/handler with the same settings, you and him would get the SAME victims because you're sharing the SAME IP !!!
3) the last instance happens either with old victims that I've forgotten about after setting up persistence on their computers....or sometimes with BOTS that scan the net for specific open ports and pick your computer by chance
Are you using any proxy or vpn??
Depends, maybe you've set the port to some common everyday port by mistake, and for every ping or packet it will try and respond with a payload stage. If it is not making a session with an unknown IP (which would be unlikely and almost impossible) I wouldn't pay too much attention. Of course just change the port you're listening on as well as the one on the payload.
@Se7enpeace: I just input the IP to a IP locator website to get the country. Neither using proxy nor VPN.
@Hxrrofo: I'm using port 443 and I just have one target, no VPN. It happens every time I leave the exploit running for a few minutes, I never open a session but it still keeps trying to send the stage.
@Ne-py: Port 443 like in most tutorials on here, it's not making any sessions just sending stages. I'll try switching ports, any recommendations? At the moment I'm practicing with a veil-evasion .exe so no specific exploit per se.
Thanks for the answers guys!
Is your pc compromised to other malware??
@Se7enpeace: Shouldn't be, but who knows these days. Got Spybot+Malwarebytes and scan regularly.
Share Your Thoughts