Well the title said almost everything ...
But I'm curious what kind of material you have to make your thing.
I'm a beginner, and I'm not sur what "to buy" or "build" or "recycled from scratch" ...
tower, laptop, raspberry pi .... and so on
For the software, most using Linux base with some add on like Kali or backtrack ...
So, give me your ex of what you have, your do or don't, etc ;)
Forum Thread: What Are You Using for Hacking?
- Hot
- Active
-
 Forum Thread:
When My Kali Linux Finishes Installing (It Is Ready to Boot), and When I Try to Boot It All I Get Is a Black Screen.
8
Replies
Forum Thread:
When My Kali Linux Finishes Installing (It Is Ready to Boot), and When I Try to Boot It All I Get Is a Black Screen.
8
Replies
1 day ago -
 Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
1 wk ago -
 Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
2
Replies
Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
2
Replies
4 wks ago -
 Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
4 wks ago -
 Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
2 mo ago -
 Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
2 mo ago -
 Metasploit Error:
Handler Failed to Bind
41
Replies
Metasploit Error:
Handler Failed to Bind
41
Replies
3 mo ago -
 Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
3 mo ago -
 How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
3 mo ago -
 How to:
Crack Instagram Passwords Using Instainsane
36
Replies
How to:
Crack Instagram Passwords Using Instainsane
36
Replies
3 mo ago -
 Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
3 mo ago -
 Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
3 mo ago -
 Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
4 mo ago -
 How to:
Sign the APK File with Embedded Payload (The Ultimate Guide)
10
Replies
How to:
Sign the APK File with Embedded Payload (The Ultimate Guide)
10
Replies
4 mo ago -
 Forum Thread:
How to Run and Install Kali Linux on a Chromebook
18
Replies
Forum Thread:
How to Run and Install Kali Linux on a Chromebook
18
Replies
5 mo ago -
 Forum Thread:
How to Find Admin Panel Page of a Website?
13
Replies
Forum Thread:
How to Find Admin Panel Page of a Website?
13
Replies
6 mo ago -
 Forum Thread:
can i run kali lenux in windows 10 without reboting my computer
4
Replies
Forum Thread:
can i run kali lenux in windows 10 without reboting my computer
4
Replies
6 mo ago -
 Forum Thread:
How to Hack School Website
11
Replies
Forum Thread:
How to Hack School Website
11
Replies
6 mo ago -
 Forum Thread:
Make a Phishing Page for Harvesting Credentials Yourself
8
Replies
Forum Thread:
Make a Phishing Page for Harvesting Credentials Yourself
8
Replies
6 mo ago -
 Forum Thread:
Creating an Completely Undetectable Executable in Under 15 Minutes!
38
Replies
Forum Thread:
Creating an Completely Undetectable Executable in Under 15 Minutes!
38
Replies
7 mo ago
-
 How To:
Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
How To:
Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
-
 How To:
Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
How To:
Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
-
 How To:
Crack SSH Private Key Passwords with John the Ripper
How To:
Crack SSH Private Key Passwords with John the Ripper
-
 How To:
Scan for Vulnerabilities on Any Website Using Nikto
How To:
Scan for Vulnerabilities on Any Website Using Nikto
-
 Hack Like a Pro:
How to Find Directories in Websites Using DirBuster
Hack Like a Pro:
How to Find Directories in Websites Using DirBuster
-
 How To:
Enumerate SMB with Enum4linux & Smbclient
How To:
Enumerate SMB with Enum4linux & Smbclient
-
 How To:
Exploit EternalBlue on Windows Server with Metasploit
How To:
Exploit EternalBlue on Windows Server with Metasploit
-
 How To:
Find Vulnerable Webcams Across the Globe Using Shodan
How To:
Find Vulnerable Webcams Across the Globe Using Shodan
-
 How To:
Brute-Force FTP Credentials & Get Server Access
How To:
Brute-Force FTP Credentials & Get Server Access
-
 How To:
Find Identifying Information from a Phone Number Using OSINT Tools
How To:
Find Identifying Information from a Phone Number Using OSINT Tools
-
 How To:
Use SQL Injection to Run OS Commands & Get a Shell
How To:
Use SQL Injection to Run OS Commands & Get a Shell
-
 How To:
Use Ettercap to Intercept Passwords with ARP Spoofing
How To:
Use Ettercap to Intercept Passwords with ARP Spoofing
-
 How To:
Buy the Best Wireless Network Adapter for Wi-Fi Hacking in 2019
How To:
Buy the Best Wireless Network Adapter for Wi-Fi Hacking in 2019
-
 How To:
Automate Wi-Fi Hacking with Wifite2
How To:
Automate Wi-Fi Hacking with Wifite2
-
 Hacking macOS:
How to Hack a Mac Password Without Changing It
Hacking macOS:
How to Hack a Mac Password Without Changing It
-
 The Hacks of Mr. Robot:
How to Spy on Anyone's Smartphone Activity
The Hacks of Mr. Robot:
How to Spy on Anyone's Smartphone Activity
-
 How To:
Hack Networks & Devices Right from Your Wrist with the Wi-Fi Deauther Watch
How To:
Hack Networks & Devices Right from Your Wrist with the Wi-Fi Deauther Watch
-
 How To:
Advanced Techniques to Bypass & Defeat XSS Filters, Part 1
How To:
Advanced Techniques to Bypass & Defeat XSS Filters, Part 1
-
 How To:
Compromise a Web Server & Upload Files to Check for Privilege Escalation, Part 2
How To:
Compromise a Web Server & Upload Files to Check for Privilege Escalation, Part 2
-
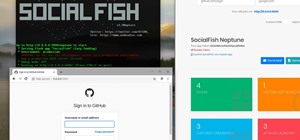
 How To:
Phish Social Media Sites with SocialFish
How To:
Phish Social Media Sites with SocialFish
















5 Responses
I'm pretty new to pentesting myself, but for the hardware you can use just about any computer as long as you can use Kali or other pentesting systems (https://www.concise-courses.com/security/top-ten-distros/) most of the software you'll want will either come on the distro or in the repos but if it doesn't the one or more essential tool(s) that I can think of are Metasploit with some kind of av evasion live veil-evasion or something similar. Anyways, hope this answered your question. :D
You will want to get an alpha wireless card for packet injection. Read a few of OTW's posts and you should get a better idea. Welcome to nullbyte
Bag full of live CDs from I don't even know how many distros.
Ubuntu installed on a relatively new PC with not fantastic specs for developing.
Android phone, alfa wireless adapter, all the love I can give it.
Alfa wireless adapter, BadUSB(My favorite), no log dobule vpn + proxy chains(to protect your anonimity), free hostings and freedomains(for phishing). Kali Linux on USB(microwave it if you do something nasty maybe do the same thing to the RAM too). And last but not least macchanger and Intercepter-NG on my android phone to hijack the http sessions on public networks. Most of these will make you a kinda script kido but you can use them for the beginning.
Welcome to Nullbyte.
I uses Kali Linux on VM and i also recycled a desktop computer for Kali, i've also a laptop with dual boot (win 7 + kali). As they said before, metasploit, free hosting, freedomains, proxychains + no log dobule vpn, webhttrack ( to clone website) macchanger ( to spoof your mac), setoolkit ( useful ) sqlmap, tor, tor-browser, for wireless injection you will need a alfa wireless card (mine is awus36nhr), kind of av evasion live veil-evasion with metasploit, netool.sh (i love this toolbox), Gh0st, Ghost-phisher, dnsspoof, nmap, nikto ...
Share Your Thoughts