SOLVED:
Delete your current wifiphisher, go back to OTW's article and use the git hub copy command to download the newest version. You also have to amplify your tx power on your wireless adapter. You can find my guide on that here.
----------------
The Problem I had
I'm having an issue with the attached post.
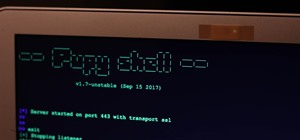
I am running Kali on a Live USB stick and using the -jI selector to use my Alfa (AWUS036H) on monitor mode and using my built in adapter (PCI Adapter) for Internet access. I then select my network and the script goes into a loop (Im assuming that is causing the issue?) where it continually repeats this screen.
![[Solved] Wifiphisher Help - Looping Jam and Not Allowing Connection to False AP](https://img.wonderhowto.com/img/31/17/63589308906633/0/solved-wifiphisher-help-looping-jam-and-not-allowing-connection-false-ap.w1456.jpg)
I am presuming this is continually booting off all users (as this is whats happening) thus, disallowing anyone to connect and even reach the fake webpage.
Hopefully I have given you enough to work off of. If not, I will be happy to add more. Thanks.
Also, don't know if it matters, but BOTH my adapters are running at txpower: 20. (Due to having several issues with changing TX power) I don't believe this is an issue as I have selected wlan2 (my Alfa adapter) to be in monitor mode manually using: python wifiphisher.py -jI wlan2
How to Hack Wi-Fi: Get Anyone's Wi-Fi Password Without Cracking Using Wifiphisher « Null Byte
 Welcome back, my tenderfoot hackers! Do you need to get a Wi-Fi password but don't have the time to crack it? In previous tutorials, I have shown how to crack WEP, WPA2, and WPS, but some people have complained that cracking WPA2 takes too long and that not all access points have WPS enabled (even though quite a few do). To help out in these situations, I present to you an almost surefire way to get a Wi-Fi password without cracking—Wifiphisher. Steps in the Wifiphisher Strategy The idea here is to create an evil twin AP, then de-authenticate or DoS the user from their real AP. When they
Welcome back, my tenderfoot hackers! Do you need to get a Wi-Fi password but don't have the time to crack it? In previous tutorials, I have shown how to crack WEP, WPA2, and WPS, but some people have complained that cracking WPA2 takes too long and that not all access points have WPS enabled (even though quite a few do). To help out in these situations, I present to you an almost surefire way to get a Wi-Fi password without cracking—Wifiphisher. Steps in the Wifiphisher Strategy The idea here is to create an evil twin AP, then de-authenticate or DoS the user from their real AP. When they








































3 Responses
having he same issue
Delete your current wifiphisher, go back to OTW's article and use the git hub copy command to download the newest version. You also have to amplify your tx power on your wireless adapter. You can find my guide on that here.
Please Do Provide The link To OTW's Article!
having the same problem
Share Your Thoughts