I know it's possible to use socks proxy on localhost but it makes some problem for me. I can't understand how customize it. For example dante-server for debian. Any thoughts about this?
- Hot
- Active
-
 Forum Thread:
Whatsapp Hack?
16
Replies
Forum Thread:
Whatsapp Hack?
16
Replies
6 hrs ago -
 Forum Thread:
How to Track Who Is Sms Bombing Me .
4
Replies
Forum Thread:
How to Track Who Is Sms Bombing Me .
4
Replies
2 mo ago -
 Forum Thread:
Removing Pay-as-You-Go Meter on Loan Phones.
1
Replies
Forum Thread:
Removing Pay-as-You-Go Meter on Loan Phones.
1
Replies
2 mo ago -
 Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
3
Replies
Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
3
Replies
2 mo ago -
 Forum Thread:
moab5.Sh Error While Running Metasploit
17
Replies
Forum Thread:
moab5.Sh Error While Running Metasploit
17
Replies
3 mo ago -
 Forum Thread:
Execute Reverse PHP Shell with Metasploit
1
Replies
Forum Thread:
Execute Reverse PHP Shell with Metasploit
1
Replies
5 mo ago -
 Forum Thread:
Install Metasploit Framework in Termux No Root Needed M-Wiz Tool
1
Replies
Forum Thread:
Install Metasploit Framework in Termux No Root Needed M-Wiz Tool
1
Replies
5 mo ago -
 Forum Thread:
Hack and Track People's Device Constantly Using TRAPE
35
Replies
Forum Thread:
Hack and Track People's Device Constantly Using TRAPE
35
Replies
6 mo ago -
 Forum Thread:
When My Kali Linux Finishes Installing (It Is Ready to Boot), and When I Try to Boot It All I Get Is a Black Screen.
8
Replies
Forum Thread:
When My Kali Linux Finishes Installing (It Is Ready to Boot), and When I Try to Boot It All I Get Is a Black Screen.
8
Replies
7 mo ago -
 Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
7 mo ago -
 Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
8 mo ago -
 Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
9 mo ago -
 Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
9 mo ago -
 Metasploit Error:
Handler Failed to Bind
41
Replies
Metasploit Error:
Handler Failed to Bind
41
Replies
10 mo ago -
 Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
10 mo ago -
 How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
10 mo ago -
 How to:
Crack Instagram Passwords Using Instainsane
36
Replies
How to:
Crack Instagram Passwords Using Instainsane
36
Replies
10 mo ago -
 Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
10 mo ago -
 Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
10 mo ago -
 Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
11 mo ago
-
 How To:
Scan for Vulnerabilities on Any Website Using Nikto
How To:
Scan for Vulnerabilities on Any Website Using Nikto
-
 How To:
Make Your Own Bad USB
How To:
Make Your Own Bad USB
-
 How To:
Dox Anyone
How To:
Dox Anyone
-
 How To:
Run USB Rubber Ducky Scripts on a Super Inexpensive Digispark Board
How To:
Run USB Rubber Ducky Scripts on a Super Inexpensive Digispark Board
-
 How To:
Top 10 Things to Do After Installing Kali Linux
How To:
Top 10 Things to Do After Installing Kali Linux
-
 How To:
Find Identifying Information from a Phone Number Using OSINT Tools
How To:
Find Identifying Information from a Phone Number Using OSINT Tools
-
 How To:
Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
How To:
Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
-
 How To:
Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
How To:
Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
-
 How To:
Intercept Images from a Security Camera Using Wireshark
How To:
Intercept Images from a Security Camera Using Wireshark
-
 How To:
Automate Wi-Fi Hacking with Wifite2
How To:
Automate Wi-Fi Hacking with Wifite2
-
 How To:
Hunt Down Wi-Fi Devices with a Directional Antenna
How To:
Hunt Down Wi-Fi Devices with a Directional Antenna
-
 How To:
Use SpiderFoot for OSINT Gathering
How To:
Use SpiderFoot for OSINT Gathering
-
 Become an Elite Hacker Part 4:
Hacking a Website. [Part 1]
Become an Elite Hacker Part 4:
Hacking a Website. [Part 1]
-
 How To:
Use MDK3 for Advanced Wi-Fi Jamming
How To:
Use MDK3 for Advanced Wi-Fi Jamming
-
 How To:
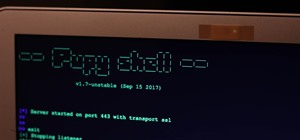
Use Pupy, a Linux Remote Access Tool
How To:
Use Pupy, a Linux Remote Access Tool
-
 How To:
Wardrive on an Android Phone to Map Vulnerable Networks
How To:
Wardrive on an Android Phone to Map Vulnerable Networks
-
 How To:
Gain Complete Control of Any Android Phone with the AhMyth RAT
How To:
Gain Complete Control of Any Android Phone with the AhMyth RAT
-
 How To:
Spy on Network Relationships with Airgraph-Ng
How To:
Spy on Network Relationships with Airgraph-Ng
-
 How To:
Change a Phone's Coordinates by Spoofing Wi-Fi Geolocation Hotspots
How To:
Change a Phone's Coordinates by Spoofing Wi-Fi Geolocation Hotspots
-
 Hack Like a Pro:
How to Hack Remote Desktop Protocol (RDP) to Snatch the Sysadmin Password
Hack Like a Pro:
How to Hack Remote Desktop Protocol (RDP) to Snatch the Sysadmin Password
















8 Responses
I don't know how to answer you.
There Are Proxies, VPN, Addons that help mask a user's address.
If you wanna try tor, check out the link - Tor and A list of pages here.
Try this for The Dante Server
# Sergeant
Hi,
TOR Browser is unsafe. The fed's already have most of the nodes. VPN's and or Proxychains.
Although I agree that ToR has some problems, it is NOT true that the Feds have most of the nodes.
I would personally use a no-logs VPN because:
One down side to VPNs is that Kali Linux doesn't have native support for VPNs, but you can easily set it up. Follow this tutorial to do so:
Use a vpn/proxy like SumRando
Thanks for respounding...Recently I try launching proxychains under tor. It works. Think, VPN will be right choise.
When I try to crack pass (e.g. aircrack, john the ripper) how I can spread bruteforce between targets hosts?
As long as you don't run VPNs with ToR, you should be good.
how do i stay anonymous when i use nmap and other thiings how o i modify my ip
Share Your Thoughts