I am using a Windows host running vbox and Kali VM in it. My host machine and Kali VM IP is configured static. Network bridged adapter.
When I generate a payload on Metasploit with my public IP port 80 and it does not connect back to my machine. I disabled my firewall to check it. My device is this
(https://i.stack.imgur.com/8pPWb.jpg)
I used to connect to the internet through this WiFi device GSM internet sim in it. I also configured my router for port forwarding.
Added virtual server rule > service name: xyz ,wan port: 80, lan port:80 localip: my kali vm ip ,tcp/udp:on ,service :enabled
So this is my rule
And there is an option of DMZ in my internet device : dmz:enabled with my kali vm ip .
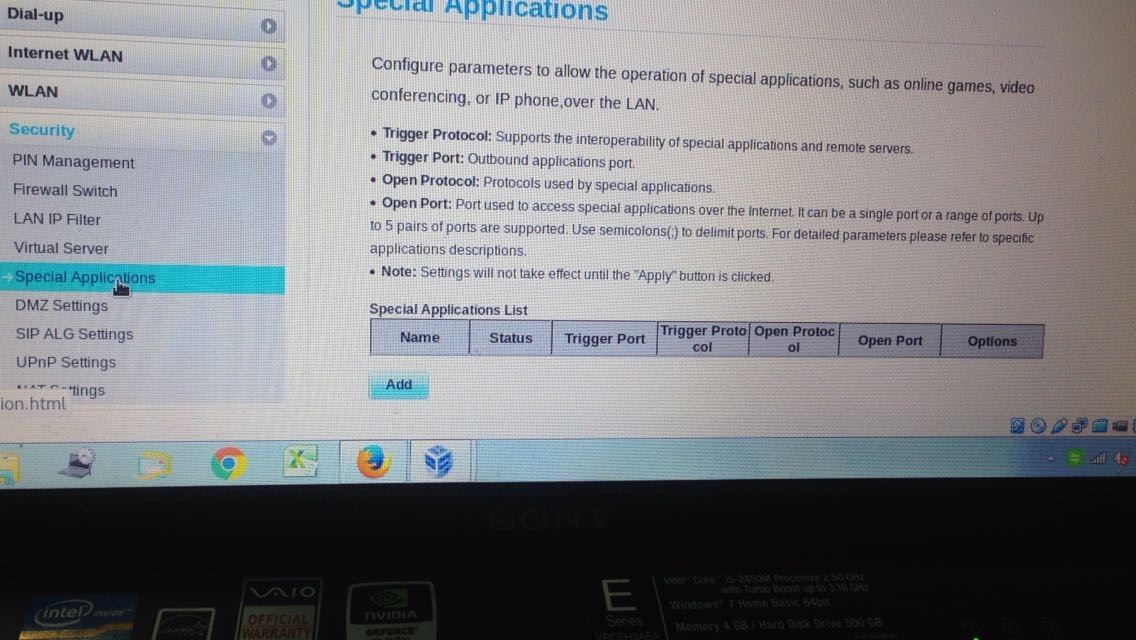
And the third option was this
(https://i.stack.imgur.com/Lap5t.jpg)
rule i added (trigger port:80 and open port:80
I filled out all these three options virtual server, DMZ, and last one trigger port. But it didn't work.
I tried to check my port on canyouseeme.org. Also I generated a payload with my public IP and sent it to my friend living in Italy. He ran in his Android phone. I got no session. Locally everything is working fine.
I tried to connect my another phone with my WLAN device and I got a session on Metasploit.
Can anybody help me to sort out this issue? Any alternate if ISP blocked or filtered my ports? Or did I configure it incorrectly?










































Be the First to Respond
Share Your Thoughts