If you were hacked and you could attribute that hack to a specific IP address, what would you do?
Forum Thread: If You Were Hacked, What Would You Do?
- Hot
- Active
-
 Forum Thread:
Whatsapp Hack?
16
Replies
Forum Thread:
Whatsapp Hack?
16
Replies
1 day ago -
 Forum Thread:
How to Track Who Is Sms Bombing Me .
4
Replies
Forum Thread:
How to Track Who Is Sms Bombing Me .
4
Replies
2 mo ago -
 Forum Thread:
Removing Pay-as-You-Go Meter on Loan Phones.
1
Replies
Forum Thread:
Removing Pay-as-You-Go Meter on Loan Phones.
1
Replies
2 mo ago -
 Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
3
Replies
Forum Thread:
Hydra Syntax Issue Stops After 16 Attempts
3
Replies
2 mo ago -
 Forum Thread:
moab5.Sh Error While Running Metasploit
17
Replies
Forum Thread:
moab5.Sh Error While Running Metasploit
17
Replies
3 mo ago -
 Forum Thread:
Execute Reverse PHP Shell with Metasploit
1
Replies
Forum Thread:
Execute Reverse PHP Shell with Metasploit
1
Replies
5 mo ago -
 Forum Thread:
Install Metasploit Framework in Termux No Root Needed M-Wiz Tool
1
Replies
Forum Thread:
Install Metasploit Framework in Termux No Root Needed M-Wiz Tool
1
Replies
5 mo ago -
 Forum Thread:
Hack and Track People's Device Constantly Using TRAPE
35
Replies
Forum Thread:
Hack and Track People's Device Constantly Using TRAPE
35
Replies
6 mo ago -
 Forum Thread:
When My Kali Linux Finishes Installing (It Is Ready to Boot), and When I Try to Boot It All I Get Is a Black Screen.
8
Replies
Forum Thread:
When My Kali Linux Finishes Installing (It Is Ready to Boot), and When I Try to Boot It All I Get Is a Black Screen.
8
Replies
7 mo ago -
 Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
Forum Thread:
HACK ANDROID with KALI USING PORT FORWARDING(portmap.io)
12
Replies
7 mo ago -
 Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
Forum Thread:
Hack Instagram Account Using BruteForce
208
Replies
8 mo ago -
 Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
Forum Thread:
Metasploit reverse_tcp Handler Problem
47
Replies
9 mo ago -
 Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
Forum Thread:
How to Train to Be an IT Security Professional (Ethical Hacker)
22
Replies
10 mo ago -
 Metasploit Error:
Handler Failed to Bind
41
Replies
Metasploit Error:
Handler Failed to Bind
41
Replies
10 mo ago -
 Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
Forum Thread:
How to Hack Android Phone Using Same Wifi
21
Replies
10 mo ago -
 How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
How to:
HACK Android Device with TermuX on Android | Part #1 - Over the Internet [Ultimate Guide]
177
Replies
10 mo ago -
 How to:
Crack Instagram Passwords Using Instainsane
36
Replies
How to:
Crack Instagram Passwords Using Instainsane
36
Replies
10 mo ago -
 Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
Forum Thread:
How to Hack an Android Device Remotely, to Gain Acces to Gmail, Facebook, Twitter and More
5
Replies
10 mo ago -
 Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
Forum Thread:
How Many Hackers Have Played Watch_Dogs Game Before?
13
Replies
10 mo ago -
 Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
Forum Thread:
How to Hack an Android Device with Only a Ip Adress
55
Replies
11 mo ago
-
 Steganography:
How to Hide Secret Data Inside an Image or Audio File in Seconds
Steganography:
How to Hide Secret Data Inside an Image or Audio File in Seconds
-
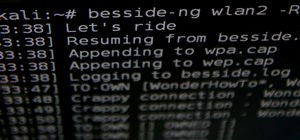 How to Hack Wi-Fi:
Automating Wi-Fi Hacking with Besside-ng
How to Hack Wi-Fi:
Automating Wi-Fi Hacking with Besside-ng
-
 How To:
Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
How To:
Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
-
 How To:
Spy on Traffic from a Smartphone with Wireshark
How To:
Spy on Traffic from a Smartphone with Wireshark
-
 How To:
Find Vulnerable Webcams Across the Globe Using Shodan
How To:
Find Vulnerable Webcams Across the Globe Using Shodan
-
 How To:
Enable Monitor Mode & Packet Injection on the Raspberry Pi
How To:
Enable Monitor Mode & Packet Injection on the Raspberry Pi
-
 How To:
Exploit Recycled Credentials with H8mail to Break into User Accounts
How To:
Exploit Recycled Credentials with H8mail to Break into User Accounts
-
 Zanti:
Nmap
Zanti:
Nmap
-
 How To:
Find Identifying Information from a Phone Number Using OSINT Tools
How To:
Find Identifying Information from a Phone Number Using OSINT Tools
-
 How To:
Find Passwords in Exposed Log Files with Google Dorks
How To:
Find Passwords in Exposed Log Files with Google Dorks
-
 How To:
Gain SSH Access to Servers by Brute-Forcing Credentials
How To:
Gain SSH Access to Servers by Brute-Forcing Credentials
-
 How To:
Check if Your Wireless Network Adapter Supports Monitor Mode & Packet Injection
How To:
Check if Your Wireless Network Adapter Supports Monitor Mode & Packet Injection
-
 How to Hack Wi-Fi:
Cracking WPA2 Passwords Using the New PMKID Hashcat Attack
How to Hack Wi-Fi:
Cracking WPA2 Passwords Using the New PMKID Hashcat Attack
-
 How To:
The Top 80+ Websites Available in the Tor Network
How To:
The Top 80+ Websites Available in the Tor Network
-
 How To:
Use SpiderFoot for OSINT Gathering
How To:
Use SpiderFoot for OSINT Gathering
-
 How To:
Hunt Down Social Media Accounts by Usernames with Sherlock
How To:
Hunt Down Social Media Accounts by Usernames with Sherlock
-
 How To:
Escape Restricted Shell Environments on Linux
How To:
Escape Restricted Shell Environments on Linux
-
 How To:
Use SQL Injection to Run OS Commands & Get a Shell
How To:
Use SQL Injection to Run OS Commands & Get a Shell
-
 The Hacks of Mr. Robot:
How to Spy on Anyone's Smartphone Activity
The Hacks of Mr. Robot:
How to Spy on Anyone's Smartphone Activity
-
 Hack Like a Pro:
Metasploit for the Aspiring Hacker, Part 10 (Finding Deleted Webpages)
Hack Like a Pro:
Metasploit for the Aspiring Hacker, Part 10 (Finding Deleted Webpages)

















9 Responses
First of all ,im going to plug off my internet ,then check my network as well as firewall settings to see any forwarded/opened ports ,or any suspicious connection that i didn't make lately .
Then ,checking logs to get the latest activities on my machine .
I think these two steps are the most essential for any one on any OS ,after that it really depends on everyone's knowledge and OS ,for example ,a Microsoft windows user ,might want to check registry ,as well as file system activity to see if any file/key/hive was added/edited/removed and thus can be analysed .
A Linux user might need to check ( and maybe twice ) his network activities and then analyze them .
Disconnect the internet. Since I know that hack came from a specific address, I'd write an iptable rule to block all packets from that address. Then I'd check the logs for any recent activity.
Would you consider retaliating?
yes ,i would definitely do !!
Even if it is illegal to retaliate?
Master OTW, why don't you just do another article on how to check ..all ways of checking..if one has been hacked..for both windows and linux? I am sure the community will very much appreciate...
thanks
isnt it illegal in the first place to hack into someone? so why not retaliate legally? See if you know enough info to be able to hack them back, then im pretty sure you could get that user in a lot of trouble if you report them.
sure, it's not nearly as fun and may take alot longer then hacking them back but i dont know, thats just what i think.
i definately would want to hack them back, but me personally as being pretty new to the hacking world, i wouldnt be able to actually retaliate on their level
Well ,i didn't quite understand that retaliating him is the same as hacking him back as he did against my network ,i would just rather block him ,and analyze every single bit came from him and try to see what tools he did use ,what methods he used to complete the attack ,and try to stop/block them from sending packets to my firewall .
my girlfriends email was hacked and all the mail was forwarded to an email address >>>>>> what a nugget (beats me why he would leave his email address). He gained access to her paypal account and tried to transfer £80.00 luckily there was no funds. So i did retaliate even though i broke the law but i don't think the viruses was enough truth is i come on this site to teach my self how to gain access to him by any means necessary and i wont stop until he has felt the invasion that my girlfriend felt ! Hence why i follow OTW as he is a great teacher.
Share Your Thoughts